Recognition: no theorem link
On the Verification Problem of Remote Direct Memory Access programs (Extended Version with Appendix)
Pith reviewed 2026-05-12 05:17 UTC · model grok-4.3
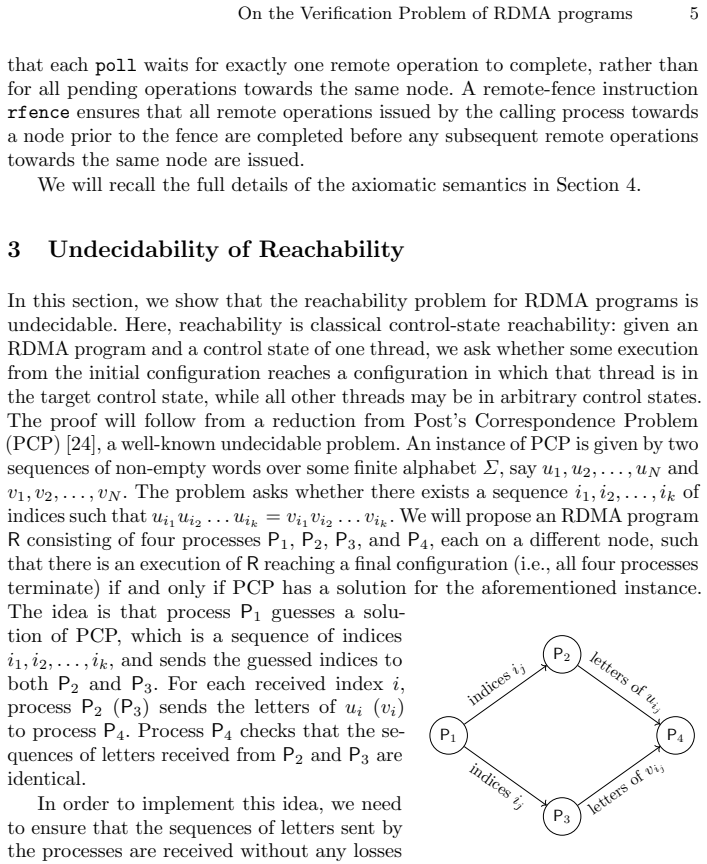
The pith
RDMA programs have undecidable reachability but decidable robustness to sequential consistency.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
Reachability is undecidable for RDMA programs even in restricted fragments. Robustness is decidable because any non-robust program admits a violating execution of a specific normal form; this form allows reduction of robustness to reachability in finite-state programs with counters, producing an EXPSPACE upper bound in general and a PSPACE upper bound without poll operations, with matching lower bounds.
What carries the argument
The normal form for robustness violations, which forces any violating execution into a specific restricted shape that can be checked via reachability in counter programs.
Load-bearing premise
The operational semantics used for RDMA operations correctly capture all possible behaviors of actual hardware without omitting cases that would require separate handling.
What would settle it
A concrete RDMA program with a robustness violation whose shortest violating execution fails to match the normal form would refute the central technical result.
Figures









read the original abstract
Remote Direct Memory Access (RDMA) is a technology that allows direct memory access from the memory of one computer into that of another without involving either one's operating system. This enables high-throughput, low-latency networking, which is especially useful in massively parallel computer clusters. In this paper, we study the reachability and robustness problems for RDMA programs. We show that reachability is undecidable in general, even for a restricted fragment of the model. We then focus on robustness, which asks whether a program exhibits the same behaviours under the RDMA and sequential consistency (SC) semantics, and prove that this problem is decidable. Our central technical result establishes a normal form for robustness violations, showing that any non-robust program admits a violating execution of a specific form. We then leverage this normal form to obtain a decision procedure that reduces robustness to reachability in finite-state programs with counters, yielding an EXPSPACE upper bound in the general case, and a PSPACE upper bound in the absence of poll operations. Finally, we also show that both of these bounds are optimal.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The paper studies verification of RDMA programs. It proves reachability is undecidable even for a restricted fragment. For robustness (whether RDMA executions match sequential consistency), it establishes a normal form for all violating executions, reduces the problem to reachability in finite-state counter machines, and derives tight EXPSPACE (general) and PSPACE (no poll operations) upper bounds that match lower bounds.
Significance. If the normal-form argument and reductions hold, the results supply the first decidability and tight complexity classification for robustness in RDMA, a practically important model for high-performance networking. The normal form is a reusable technical device, the reduction to known counter-machine problems is standard and clean, and the optimality proofs give a complete picture. These are genuine strengths for the verification community.
minor comments (1)
- Abstract: a one-sentence description of the core RDMA operations (e.g., RDMA read/write, poll) would help readers immediately grasp the model without consulting the body.
Simulated Author's Rebuttal
We thank the referee for the positive summary of our work on reachability and robustness for RDMA programs, and for recognizing the significance of the normal-form result and the tight complexity classification. The recommendation for minor revision is noted; however, the report contains no specific major comments or requested changes.
Circularity Check
No significant circularity
full rationale
The paper establishes undecidability of reachability by reduction from a known undecidable problem, then derives a normal form for robustness violations directly from the RDMA operational semantics (showing every violating execution can be transformed into a specific shape), and finally reduces robustness checking to reachability in finite-state counter machines whose decidability and complexity are independently known. None of these steps is self-definitional, none renames a fitted parameter as a prediction, and no load-bearing premise rests on a self-citation chain; the normal form is proved rather than assumed, and the final bounds are obtained by standard complexity results external to the paper.
Axiom & Free-Parameter Ledger
axioms (1)
- standard math Standard undecidability of reachability in counter machines or similar models
Reference graph
Works this paper leans on
-
[1]
Abdulla, P.A., Arora, J., Atig, M.F., Krishna, S.N.: Verification of programs under the release-acquire semantics. In: PLDI. pp. 1117–1132. ACM (2019). https: //doi.org/https://doi.org/10.1145/3314221.3314649
-
[2]
Abdulla, P.A., Atig, M.F., Bouajjani, A., Derevenetc, E., Leonardsson, C., Meyer, R.: On the state reachability problem for concurrent programs under power. In: NETYS. Lecture Notes in Computer Science, vol. 12129, pp. 47–59. Springer (2020). https://doi.org/https://doi.org/10.1007/978-3-030-67087-0_4
-
[3]
Abdulla, P.A., Atig, M.F., Bouajjani, A., Kumar, K.N., Saivasan, P.: Deciding reachability under persistent x86-tso. Proc. ACM Program. Lang.5(POPL), 1–32 (2021).https://doi.org/https://doi.org/10.1145/3434337
-
[4]
Abdulla, P.A., Atig, M.F., Bouajjani, A., Kumar, K.N., Saivasan, P.: Verification under intel-x86 with persistency. Proc. ACM Program. Lang.8(PLDI), 1189–1212 (2024).https://doi.org/https://doi.org/10.1145/3656425
-
[5]
Abdulla, P.A., Atig, M.F., Bouajjani, A., Ngo, T.P.: The benefits of duality in verifying concurrent programs under TSO. In: CONCUR. LIPIcs, vol. 59, pp. 5:1– 5:15. Schloss Dagstuhl - Leibniz-Zentrum f¨ ur Informatik (2016).https://doi.org/ https://doi.org/10.4230/LIPIcs.CONCUR.2016.5
-
[6]
Abdulla, P.A., Atig, M.F., Godbole, A., Krishna, S., Vafeiadis, V.: The decidability of verification under PS 2.0. In: ESOP. Lecture Notes in Computer Science, vol. 12648, pp. 1–29. Springer (2021). https://doi.org/https://doi.org/10.26226/ morressier.604907f41a80aac83ca25d26
work page 2021
- [7]
-
[8]
Abdulla, P.A., Atig, M.F., Phong, N.T.: The best of both worlds: Trading efficiency and optimality in fence insertion for TSO. In: ESOP. Lecture Notes in Computer Science, vol. 9032, pp. 308–332. Springer (2015). https://doi.org/https://doi. org/10.1007/978-3-662-46669-8_13
-
[9]
Ambal, G., Dongol, B., Eran, H., Klimis, V., Lahav, O., Raad, A.: Semantics of remote direct memory access: Operational and declarative models of RDMA on TSO architectures. Proc. ACM Program. Lang.8(OOPSLA2), 1982–2009 (2024). https://doi.org/https://doi.org/10.1145/3689781
-
[10]
Ambal, G., Lahav, O., Raad, A.: Sufficient conditions for robustness of RDMA programs. In: ESOP (1). Lecture Notes in Computer Science, vol. 15694, pp. 56–87. Springer (2025). https://doi.org/https://doi.org/10.1007/ 978-3-031-91118-7_3
work page 2025
-
[11]
Atig, M.F., Bouajjani, A., Burckhardt, S., Musuvathi, M.: On the verification problem for weak memory models. In: POPL. pp. 7–18. ACM (2010). https: //doi.org/https://doi.org/10.1145/1706299.1706303
-
[12]
Lecture Notes in Computer Science, vol
Atig, M.F., Bouajjani, A., Burckhardt, S., Musuvathi, M.: What’s decidable about weak memory models? In: ESOP. Lecture Notes in Computer Science, vol. 7211, pp. 26–46. Springer (2012). https://doi.org/https://doi.org/10. 1007/978-3-642-28869-2_2
work page 2012
-
[13]
Bouajjani, A., Derevenetc, E., Meyer, R.: Checking and enforcing robustness against TSO. In: ESOP. Lecture Notes in Computer Science, vol. 7792, pp. 533–553. Springer (2013).https://doi.org/https://doi.org/10.1007/978-3-642-37036-6_29 22 P.A. Abdulla, M.F. Atig, G. Rajanbabu, S. Spengler
-
[14]
Bouajjani, A., Derevenetc, E., Meyer, R.: Robustness against relaxed memory models. In: Software Engineering. LNI, vol. P-227, pp. 85–86. GI (2014), https: //dl.gi.de/handle/20.500.12116/30973
work page 2014
-
[15]
In: Aceto, L., Henzinger, M., Sgall, J
Bouajjani, A., Meyer, R., M¨ ohlmann, E.: Deciding robustness against total store ordering. In: Aceto, L., Henzinger, M., Sgall, J. (eds.) Automata, Languages and Programming - 38th International Colloquium, ICALP 2011, Zurich, Switzer- land, July 4-8, 2011, Proceedings, Part II. Lecture Notes in Computer Science, vol. 6756, pp. 428–440. Springer (2011). ...
work page 2011
-
[16]
Calin, G., Derevenetc, E., Majumdar, R., Meyer, R.: A theory of partitioned global address spaces. In: FSTTCS. LIPIcs, vol. 24, pp. 127–139. Schloss Dagstuhl - Leibniz-Zentrum f¨ ur Informatik (2013).https://doi.org/https://doi.org/10. 4230/LIPIcs.FSTTCS.2013.127
work page 2013
-
[17]
Cheng, A., Esparza, J., Palsberg, J.: Complexity results for 1-safe nets. Theor. Comput. Sci.147(1&2), 117–136 (1995). https://doi.org/https://doi.org/10. 1016/0304-3975(94)00231-7
work page 1995
-
[18]
Dan, A.M., Lam, P., Hoefler, T., Vechev, M.T.: Modeling and analysis of remote memory access programming. In: OOPSLA. pp. 129–144. ACM (2016). https: //doi.org/https://doi.org/10.1145/2983990.2984033
-
[19]
Derevenetc, E.: Robustness against Relaxed Memory Models. Ph.D. thesis, Uni- versity of Kaiserslautern (2015), https://nbn-resolving.org/urn:nbn:de:hbz: 386-kluedo-40743
work page 2015
-
[20]
Derevenetc, E., Meyer, R.: Robustness against power is pspace-complete. In: ICALP (2). Lecture Notes in Computer Science, vol. 8573, pp. 158–170. Springer (2014). https://doi.org/https://doi.org/10.1007/978-3-662-43951-7_14
-
[21]
Hopcroft, J.E., Pansiot, J.: On the reachability problem for 5-dimensional vector addition systems. Theor. Comput. Sci.8, 135–159 (1979). https://doi.org/https: //doi.org/10.1016/0304-3975(79)90041-0
-
[22]
Lahav, O., Boker, U.: What’s decidable about causally consistent shared memory? ACM Trans. Program. Lang. Syst.44(2), 8:1–8:55 (2022). https://doi.org/https: //doi.org/10.1145/3505273
-
[23]
Research report (Yale University
Lipton, R.J.: The reachability problem requires exponential space. Research report (Yale University. Department of Computer Science), Department of Computer Sci- ence, Yale University (1976), https://books.google.de/books?id=7iSbGwAACAAJ
work page 1976
-
[24]
Bulletin of the American Mathematical Society52(4), 264–268 (1946)
Post, E.L.: A variant of a recursively unsolvable problem. Bulletin of the American Mathematical Society52(4), 264–268 (1946). https://doi.org/https://doi.org/ 10.1090/S0002-9904-1946-08555-9
-
[25]
Rackoff, C.: The covering and boundedness problems for vector addition systems. Theor. Comput. Sci.6, 223–231 (1978). https://doi.org/https://doi.org/10. 1016/0304-3975(78)90036-1
work page 1978
-
[26]
Singh, A.K., Lahav, O.: Decidable verification under localized release-acquire concurrency. In: TACAS (3). Lecture Notes in Computer Science, vol. 14572, pp. 235–254. Springer (2024). https://doi.org/https://doi.org/10.1007/ 978-3-031-57256-2_12
work page 2024
-
[27]
Sistla, A.P., Clarke, E.M.: The complexity of propositional linear temporal logics. J. ACM32(3), 733–749 (Jul 1985). https://doi.org/https://doi.org/10.1145/ 3828.3837 On the Verification Problem of RDMA programs 23 A Program Code for the Undecidability Proof This section holds the full program code for each of the processes in the reduction from PCP to R...
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.