Recognition: unknown
When Graph Traversal Meets Structured Preferences: Unified Framework and Complexity Results
Pith reviewed 2026-05-08 15:36 UTC · model grok-4.3
The pith
Recognizing whether voter preferences come from a graph traversal is NP-hard when the graph has few edges or low degree.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
For each of the six traversal paradigms the problem of deciding whether a preference profile admits a support graph with at most k edges is NP-hard; the same holds when the support is required only to have maximum degree k. For the depth-first search paradigm, the existence of a tree support can be decided in polynomial time. Polynomial-time solvability for tree supports under the other five paradigms follows from prior results, except that the complexity for BFS and LexBFS remains open.
What carries the argument
A graph support for a preference profile under a traversal paradigm is a graph on the candidates such that each ranking is exactly the sequence of vertices visited by running the chosen search algorithm on that graph.
If this is right
- When the support graph is forced to be sparse, no efficient algorithm exists to check whether the profile is consistent with any of the six traversals.
- Bounded-degree supports do not make the recognition problem easier; hardness persists for every paradigm.
- For DFS, the existence of a tree support can be verified efficiently, giving a practical test when the underlying structure is acyclic.
- Polynomial-time methods for tree supports under LexDFS, MCS and MNS follow directly from earlier graph-theoretic results.
Where Pith is reading between the lines
- The framework could be used to generate synthetic preference data whose structure is controlled by the choice of traversal and graph size.
- If real-world preferences often admit tree supports, then efficient checks are available for DFS but may still be missing for BFS.
- The results suggest studying approximation versions that seek a graph whose traversals come close to the observed rankings rather than matching them exactly.
Load-bearing premise
The observed preferences must be generated exactly by the visit sequences of the chosen graph traversal algorithms.
What would settle it
A concrete family of preference profiles for which the existence of a support graph with at most five edges can be decided in polynomial time under BFS would falsify the NP-hardness claim.
Figures







read the original abstract
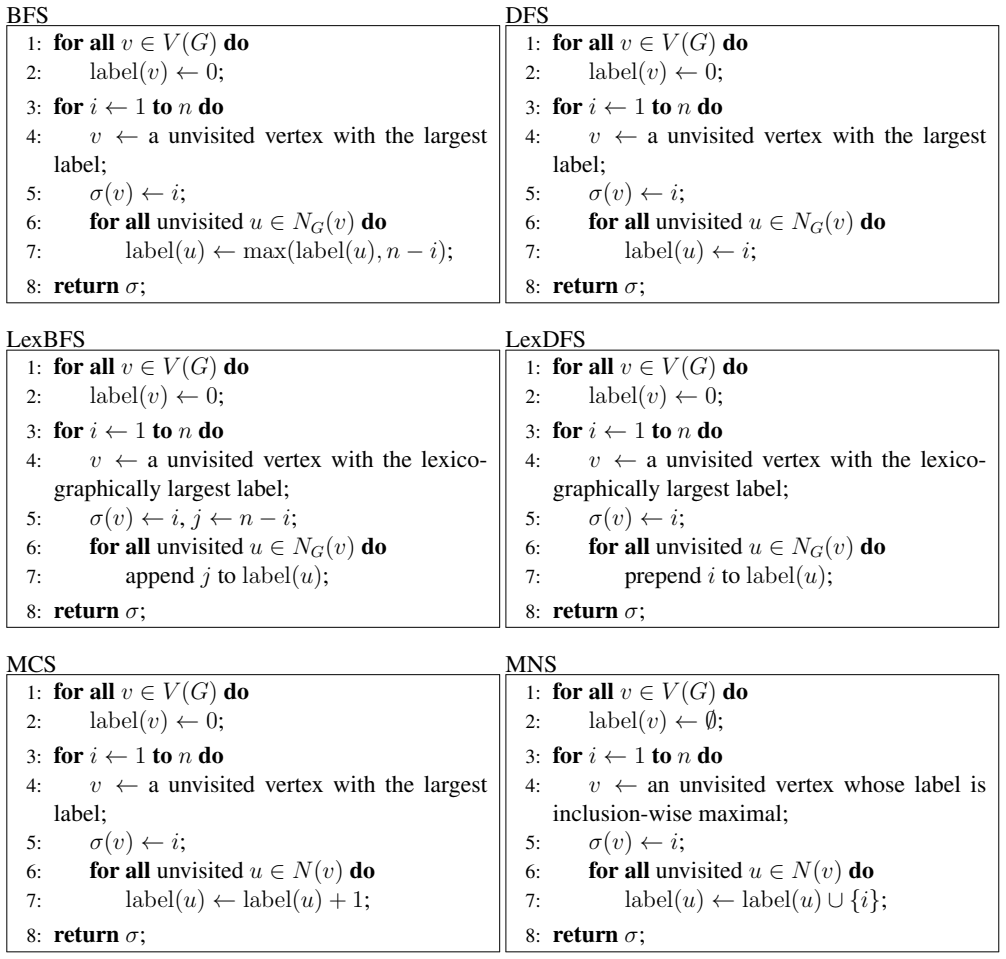
Preference restrictions have played a significant role in computational social choice. This paper studies a framework that connects preference restrictions with classical graph search paradigms. We model candidates as vertices of a graph and interpret the preference ordering of each voter as the outcome of traversing the graph according to a graph search. We focus on six fundamental paradigms: breadth-first search (BFS), depth-first search (DFS), breadth-first search (LexBFS), lexicographic depth-first (LexDFS), maximum cardinality search (MCS), and maximal neighborhood search (MNS). Within this framework, we study the problem of determining whether a given preference profile admits a graph support subject to structural restrictions, that is, whether there exists a graph such that each preference ordering can be generated by traversing the graph under the chosen paradigm. For all considered paradigms, we show that this problem is NP-hard when the graph support is required to have at most $k$ edges, where $k$ is a given integer. We further extend these hardness results to the case where the graph support is required to have maximum degree $k$. For DFS, we prove that recognizing whether a preference profile admits a tree support can be solved in polynomial time. Moreover, existing results imply polynomial-time solvability of the problem for all remaining graph traversals, except BFS and LexBFS, for which the complexity remains open.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The paper develops a unified framework modeling voter preferences as traversal orders from six graph search paradigms (BFS, DFS, LexBFS, LexDFS, MCS, MNS) on a common graph. It studies the recognition problem of whether a preference profile admits a graph support, establishing NP-hardness for all paradigms when the support has at most k edges or maximum degree k. It further shows a polynomial-time algorithm for recognizing tree supports under DFS and notes that polynomial-time recognition holds for tree supports under the remaining paradigms except BFS and LexBFS, which remain open.
Significance. If correct, the results meaningfully connect computational social choice with graph algorithms by defining preference restrictions via traversal orders. The NP-hardness results for bounded-edge and bounded-degree supports establish intractability of finding compact realizations, while the polynomial-time results for trees provide algorithmic value. The unified treatment across paradigms and the identification of open problems for BFS and LexBFS are useful for guiding follow-up work. The modeling framework appears internally consistent with standard reductions and prior algorithms.
minor comments (2)
- Abstract: the reference to 'existing results' implying polynomial-time solvability for tree supports (except BFS and LexBFS) would be strengthened by citing the specific prior works or theorems being invoked.
- The manuscript would benefit from a summary table (perhaps in the introduction or conclusion) listing the complexity status for each paradigm under the edge-bounded, degree-bounded, and tree-support cases.
Simulated Author's Rebuttal
We thank the referee for the positive summary and significance assessment of our work, as well as the recommendation for minor revision. No specific major comments were raised in the report.
Circularity Check
No significant circularity; claims rest on independent reductions and algorithms
full rationale
The paper defines a modeling framework that interprets voter preferences as outputs of standard graph traversal algorithms (BFS, DFS, LexBFS, etc.) on a shared graph. It then proves NP-hardness of recognizing supports with at most k edges (or max degree k) via reductions that operate on this model without presupposing the target hardness result. The polynomial-time algorithm for DFS tree supports is shown directly, and other cases are dispatched by citing prior independent results. No step equates a derived quantity to its input by construction, renames a known pattern as a new theorem, or relies on a self-citation chain for the central claims. The derivation chain is therefore self-contained against external benchmarks.
Axiom & Free-Parameter Ledger
axioms (1)
- standard math NP-hardness via polynomial-time reductions from known hard problems in complexity theory
Reference graph
Works this paper leans on
-
[1]
Amgoud and S
L. Amgoud and S. Vesic. Rich preference-based argumentation frameworks.Int. J. Approx. Reason., 55(2):585–606, 2014
2014
-
[2]
Beynier, N
A. Beynier, N. Maudet, S. Rey, and P. Shams. Swap dynamics in single-peaked housing markets. Auton. Agents Multi Agent Syst., 35(2):Nr. 20, 2021
2021
-
[3]
D. Black. On the rationale of group decision-making.J. Polit. Econ., 56(1):23–34, 1948
1948
-
[4]
A. G. Bonifacio. Bribe-proof reallocation with single-peaked preferences.Soc. Choice Welfare, 44(3):617–638, 2015. 41
2015
-
[5]
Brandt, M
F. Brandt, M. Brill, E. Hemaspaandra, and L. A. Hemaspaandra. Bypassing combinatorial protec- tions: Polynomial-time algorithms for single-peaked electorates.J. Artif. Intell. Res., 53:439–496, 2015
2015
-
[6]
Bretscher, D
A. Bretscher, D. G. Corneil, M. Habib, and C. Paul. A simple linear time LexBFS cograph recog- nition algorithm.SIAM J. Discrete Math., 22(4):1277–1296, 2008
2008
-
[7]
Di Caro and M
G. Di Caro and M. Dorigo. Antnet: Distributed stigmergetic control for communications networks. J. Artif. Intell. Res., 9:317–365, 1998
1998
-
[8]
Clearwater, C
A. Clearwater, C. Puppe, and A. Slinko. Generalizing the single-crossing property on lines and trees to intermediate preferences on median graphs. InIJCAI, pages 32–38, 2015
2015
-
[9]
Cornaz, L
D. Cornaz, L. Galand, and O. Spanjaard. Kemeny elections with bounded single-peaked or single- crossing width. InIJCAI, pages 76–82, 2013
2013
-
[10]
D. G. Corneil and R. Krueger. A unified view of graph searching.SIAM J. Discret. Math., 22(4):1259–1276, 2008
2008
-
[11]
G. Demange. Single-peaked orders on a tree.Math. Soc. Sci., 3(3):389–396, 1983
1983
-
[12]
Escoffier, O
B. Escoffier, O. Spanjaard, and M. Tydrichov ´a. Recognizing single-peaked preferences on an arbi- trary graph: Complexity and algorithms.Discret. Appl. Math., 348:301–319, 2024
2024
-
[13]
Faliszewski, E
P. Faliszewski, E. Hemaspaandra, L. A. Hemaspaandra, and J. Rothe. The shield that never was: Societies with single-peaked preferences are more open to manipulation and control.Inf. Comput., 209(2):89–107, 2011
2011
-
[14]
M. R. Garey, D. S. Johnson, and L. J. Stockmeyer. Some simplified NP-complete graph problems. Theor. Comput. Sci., 1(3):237–267, 1976
1976
-
[15]
K.-I. Inada. A note on the simple majority decision rule.Econometrica, 32(4):525–531, 1964
1964
-
[16]
K.-I. Inada. The simple majority decision rule.Econometrica, 37(3):490–506, 1969
1969
-
[17]
Kleiner and B
A. Kleiner and B. Moldovanu. V oting agendas and preferences on trees: Theory and practice.Am. Econ. J.: Microecon., 14(4):583–615, 2022
2022
-
[18]
R. E. Korf. Depth-first iterative-deepening: An optimal admissible tree search.Artif. Intell., 27(1):97–109, 1985
1985
-
[19]
Krnc and N
M. Krnc and N. Pivac. Graphs where Search Methods are Indistinguishable. InEuroComb, pages 351–358, 2021
2021
-
[20]
J. A. Mirrlees. An exploration in the theory of optimum income taxation.Rev. Econ. Stud., 38(114):175–208, 1971
1971
-
[21]
Nofal, K
S. Nofal, K. Atkinson, and P. E. Dunne. Algorithms for decision problems in argument systems under preferred semantics.Artif. Intell., 207:23–51, 2014
2014
-
[22]
Peters and E
D. Peters and E. Elkind. Preferences single-peaked on nice trees. InAAAI, pages 594–600, 2016
2016
-
[23]
Peters and M
D. Peters and M. Lackner. Preferences single-peaked on a circle.J. Artif. Intell. Res., 68:463–502, 2020
2020
-
[24]
Peters, L
D. Peters, L. Yu, H. Chan, and E. Elkind. Preferences single-peaked on a tree: Multiwinner elections and structural results.J. Artif. Intell. Res., 73:231–276, 2022
2022
-
[25]
S. R. Rad and O. Roy. Deliberation, single-peakedness, and coherent aggregation.Am. Polit. Sci. Rev., 115(2):629–648, 2021
2021
-
[26]
S. Rey, U. Endriss, and R. de Haan. A general framework for participatory budgeting with additional constraints.Soc. Choice Welf., 64(1-2):5–41, 2025
2025
-
[27]
K. W. S. Roberts. V oting over income tax schedules.J. Public Econ., 8(3):329–340, 1977
1977
-
[28]
D. J. Rose, R. E. Tarjan, and G. S. Lueker. Algorithmic aspects of vertex elimination on graphs. SIAM J. Comput., 5(2):266–283, 1976
1976
-
[29]
R. E. Tarjan. Depth-first search and linear graph algorithms.SIAM J. Comput., 1(2):146–160, 1972
1972
-
[30]
M. A. Trick. Recognizing single-peaked preferences on a tree.Math. Soc. Sci., 17(3):329–334, 1989
1989
-
[31]
S. Yang, F. Han, Y . Wu, and X. Yan. Fast top-ksearch in knowledge graphs. InICDE, pages 990–1001, 2016. 42
2016
-
[32]
Y . Yang. Manipulation with bounded single-peaked width: A parameterized study. InAAMAS, pages 77–85, 2015
2015
-
[33]
Yang and J
Y . Yang and J. Guo. The control complexity ofr-approval: From the single-peaked case to the general case.J. Comput. Syst. Sci., 89:432–449, 2017
2017
-
[34]
Yang and J
Y . Yang and J. Wang. Multiwinner voting with restricted admissible sets: Complexity and strate- gyproofness. InIJCAI, pages 576–582, 2018
2018
-
[35]
Zhang, Z
K. Zhang, Z. Yang, H. Liu, T. Zhang, and T. Basar. Fully decentralized multi-agent reinforcement learning with networked agents. InICML, pages 5867–5876, 2018
2018
-
[36]
C. Zhu, K. Ren, X. Liu, H. Wang, Y . Tian, and Y . Yu. A graph traversal based approach to answer non-aggregation questions over DBpedia. InJIST, pages 219–234, 2015. 43
2015
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.