Recognition: no theorem link
Confidentiality of Linear Control Systems with Quadratic Output Under Sensor Attacks [Extended Version]
Pith reviewed 2026-05-11 02:09 UTC · model grok-4.3
The pith
An adversary with sensor read-write access can induce local observability in an otherwise unobservable linear system with quadratic output by injecting a suitable signal, enabling construction of a locally exponentially convergent observer.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
For linear systems with quadratic outputs that are locally unobservable at equilibrium, an adversary who injects an appropriate signal into the sensor measurements can make the augmented system locally observable. In the successful cases the paper identifies the conditions on the injected signal and builds an observer that achieves local exponential convergence of the estimated states to the true states of the original system.
What carries the argument
The injected signal that augments the quadratic measurement equation to produce local observability of the extended system, together with the observer constructed from the resulting observability properties.
If this is right
- Certain classes of injected signals turn the unobservable linear-quadratic system into a locally observable augmented system.
- An observer can be explicitly designed that achieves local exponential convergence of state estimates under successful injection.
- The paper supplies necessary and sufficient conditions that separate signals able to induce observability from those that cannot.
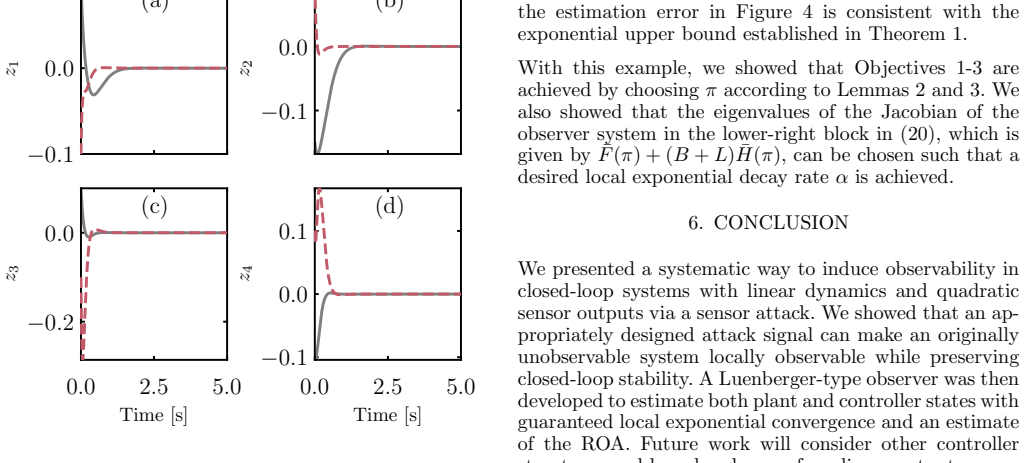
- Simulation examples confirm that the constructed observer converges when the injection conditions hold.
Where Pith is reading between the lines
- Designers of secure control systems may need to treat signal-injection attacks as a potential information-gathering rather than purely disruptive threat.
- The same mechanism could be studied in discrete-time or sampled-data settings to assess whether sampling rates affect the adversary's ability to induce observability.
- The result suggests examining whether similar injection techniques can create observability in other classes of nonlinear or switched systems that are nominally unobservable.
Load-bearing premise
The original linear-quadratic system is locally unobservable at equilibrium and there exist injected signals that satisfy the conditions needed to make the augmented system locally observable.
What would settle it
A concrete linear-quadratic system and a family of candidate injected signals for which the augmented dynamics remain locally unobservable at equilibrium, or for which the constructed observer fails to show exponential convergence of estimates.
Figures



read the original abstract
We study the state estimation problem for linear control systems with quadratic outputs which are locally unobservable at the equilibrium. We show that, despite this inherent lack of observability, an adversary with sensor read and write capability can induce observability by injecting an appropriate signal into the measurement channel. Taking the role of an adversary, we characterize when an injected signal can or cannot induce observability and, in the successful case, construct an observer that achieves local exponential convergence of state estimates to the true states of the system. A simulation study demonstrates our results.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
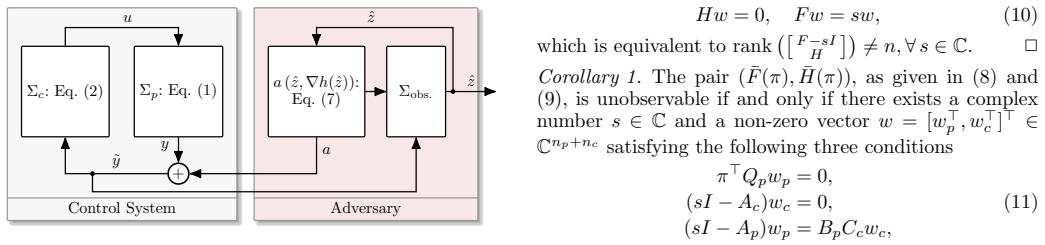
Summary. The manuscript studies state estimation for linear control systems with quadratic outputs, which are locally unobservable at the equilibrium because h(0)=0 and Dh(0)=0. It shows that an adversary with sensor read/write access can inject a signal to drive a trajectory x*(t) along which the time-varying linearization becomes observable, characterizes when such injection succeeds, and constructs a time-varying observer achieving local exponential convergence of estimates to true states, supported by a simulation.
Significance. If the claims hold, the work offers a novel angle on sensor attacks in control systems by showing how they can paradoxically enable observability and estimation in otherwise locally unobservable quadratic-output systems. The characterization of successful injections and the explicit observer construction are technically interesting contributions with potential relevance to secure control and attack-aware estimation. The simulation provides concrete validation of the theoretical approach.
major comments (1)
- [Observer Design and Convergence Analysis] In the observer design and convergence analysis (likely around the main theorem on local exponential convergence), the error dynamics are derived from the time-varying linearization along the excited trajectory x*(t), but the quadratic output map introduces higher-order remainder terms in y - h(hat x). The proof must show these O(|e|^2) terms are dominated to yield local exponential stability; if the argument relies solely on linear time-varying observability without an explicit Lyapunov function or small-gain bound on the nonlinear perturbation, the local exponential convergence claim does not necessarily follow. Please provide the precise error equation and the step that absorbs the quadratic remainder.
minor comments (2)
- [Abstract] The abstract states the main result cleanly but could briefly indicate the key assumption on the injected signal (e.g., that it renders the linearization observable) to help readers assess the scope.
- [Simulation Study] Figure captions in the simulation section should explicitly label the injected signal, the true vs. estimated states, and the error norm to make the empirical support easier to interpret.
Simulated Author's Rebuttal
We thank the referee for the detailed review and constructive feedback on our manuscript. The major comment raises a valid point about clarifying the handling of nonlinear remainder terms in the convergence proof. We address this below and will incorporate the requested details in the revision.
read point-by-point responses
-
Referee: In the observer design and convergence analysis (likely around the main theorem on local exponential convergence), the error dynamics are derived from the time-varying linearization along the excited trajectory x*(t), but the quadratic output map introduces higher-order remainder terms in y - h(hat x). The proof must show these O(|e|^2) terms are dominated to yield local exponential stability; if the argument relies solely on linear time-varying observability without an explicit Lyapunov function or small-gain bound on the nonlinear perturbation, the local exponential convergence claim does not necessarily follow. Please provide the precise error equation and the step that absorbs the quadratic remainder.
Authors: We agree that an explicit treatment of the quadratic remainder is necessary for rigor. In the manuscript (Section IV, around Theorem 1), the state estimation error e = x - hat{x} satisfies the dynamics dot{e} = A e - L(t) C(t) e + r(e, x*(t)), where the remainder r arises from the quadratic output map h(x) = x^T Q x (with h(0)=0, Dh(0)=0) and takes the form r(e) = O(|e|^2) uniformly along the bounded trajectory x*(t). The output injection uses the time-varying gain L(t) constructed from the observability Gramian of the linearized pair (A, C(t)) along x*(t), which is assumed to satisfy the uniform observability condition stated in Assumption 2. To establish local exponential stability, we employ the quadratic Lyapunov function V(e,t) = e^T P(t) e, where P(t) solves the differential Lyapunov equation dot{P} + A_cl(t)^T P + P A_cl(t) = -Q(t) with A_cl(t) = A - L(t)C(t) and Q(t) positive definite. Differentiating V along the error trajectories yields dot{V} <= -lambda_min(Q(t)) |e|^2 + 2 |e| |P(t)| |r(e)|. Since |r(e)| <= K |e|^2 for some K (locally, by smoothness of h), and the linear closed-loop system is exponentially stable with rate mu > 0 (by the observability Gramian construction), standard perturbation arguments show that for |e(0)| sufficiently small, dot{V} <= - (mu/2) |e|^2, implying local exponential convergence. We will insert the precise error equation and this Lyapunov comparison step (including the bound on the remainder) into the proof of Theorem 1 in the revised manuscript. revision: yes
Circularity Check
No significant circularity; derivation uses explicit constructions on standard linear-system properties
full rationale
The paper's core claim is that an adversary can inject a signal to render a locally unobservable quadratic-output system observable along a trajectory, followed by an explicit observer construction for local exponential convergence. This rests on time-varying linearization observability (standard Kalman rank or PBH test applied to the pair (A, Dh(x*(t)))) and standard time-varying observer design, without any fitted parameters renamed as predictions, self-definitional loops, or load-bearing self-citations. The injected-signal characterization and observer gain are derived directly from the system matrices and the chosen u(t), not by construction from the target convergence result. The skeptic concern about quadratic remainders pertains to proof completeness rather than circularity.
Axiom & Free-Parameter Ledger
axioms (2)
- domain assumption The plant is a linear time-invariant system with quadratic output map.
- domain assumption The system is locally unobservable at the equilibrium.
Reference graph
Works this paper leans on
-
[1]
2019 18th European Control Conference (ECC) , pages =
A tutorial introduction to security and privacy for cyber-physical systems , author =. 2019 18th European Control Conference (ECC) , pages =. 2019 , organization =
work page 2019
-
[2]
A systems and control perspective of
Dibaji, Seyed Mehran and Pirani, Mohammad and Flamholz, David Bezalel and Annaswamy, Anuradha M and Johansson, Karl Henrik and Chakrabortty, Aranya , journal =. A systems and control perspective of. 2019 , publisher =
work page 2019
-
[3]
Proceedings of the 6th ACM symposium on information, computer and communications security , pages =
Attacks against process control systems: risk assessment, detection, and response , author =. Proceedings of the 6th ACM symposium on information, computer and communications security , pages =
-
[4]
IET Control Theory & Applications , volume =
On model-based detectors for linear time-invariant stochastic systems under sensor attacks , author =. IET Control Theory & Applications , volume =. 2019 , publisher =
work page 2019
-
[5]
IEEE Transactions on Automatic Control , volume =
Secure switched observers for cyber-physical systems under sparse sensor attacks: A set cover approach , author =. IEEE Transactions on Automatic Control , volume =. 2019 , publisher =
work page 2019
-
[6]
ACM Transactions on Cyber-Physical Systems , volume =
SMT-based observer design for cyber-physical systems under sensor attacks , author =. ACM Transactions on Cyber-Physical Systems , volume =. 2018 , publisher =
work page 2018
-
[7]
Worst-case stealthy innovation-based linear attack on remote state estimation , author =. Automatica , volume =. 2018 , publisher =
work page 2018
-
[8]
On the confidentiality of controller states under sensor attacks , author =. Automatica , volume =. 2021 , publisher =
work page 2021
- [9]
-
[10]
J. P. Hespanha , title =
-
[11]
N. Kazantzis and C. Kravaris , title =. Systems and Control Letters , volume =
- [12]
- [13]
-
[14]
R. Hermann and A. J. Krener , title =. IEEE Transactions on Automatic Control , volume =
-
[15]
A. N. Montanari and R. Song and D. S. Bassett , title =. Physical Review Research , volume =
-
[16]
A. N. Montanari and P. S. Krishnaprasad , title =. Automatica , volume =. 2025 , note =
work page 2025
-
[17]
D. Theodosis and S. Berkane and T. Hamel and D. V. Dimarogonas , title =. IFAC-PapersOnLine , pages =
-
[18]
S. Berkane and D. Theodosis and T. Hamel and D. V. Dimarogonas , title =. IEEE Control Systems Letters , year =
-
[19]
P. Combes and A. K. Jebai and F. Malrait and P. Martin and P. Rouchon , title =. 2015 , note =
work page 2015
- [20]
-
[21]
IEEE transactions on industrial electronics , volume =
Sensorless control of induction machines—With or without signal injection? , author =. IEEE transactions on industrial electronics , volume =. 2006 , publisher =
work page 2006
-
[22]
A. Kunapareddy and B. Twu and N. J. Cowan , title =. Proceedings of the American Control Conference , pages =
-
[23]
E. D. Sontag and D. Biswas and N. J. Cowan , title =. 2022 , note =
work page 2022
-
[24]
V. Andrieu and L. Praly , title =. SIAM Journal on Control and Optimization , volume =
-
[25]
L. Brivadis and V. Andrieu and L. Praly , title =. Systems & Control Letters , volume =
- [26]
-
[27]
M. Krsti. Stability of extremum seeking feedback for general nonlinear dynamic systems , journal =
-
[28]
K. B. Ariyur and M. Krsti. Real-Time Optimization by Extremum-Seeking Control , publisher =
- [29]
-
[30]
SIAM Journal on Control and Optimization , volume =
Convergence and stability properties of the discrete Riccati operator equation and the associated optimal control and filtering problems , author =. SIAM Journal on Control and Optimization , volume =. 1976 , publisher =
work page 1976
-
[31]
J. Duerr and M. Krsti. Extremum seeking for dynamic maps using Lie brackets and singular perturbations , journal =
-
[32]
J. Kiefer and J. Wolfowitz , title =. Annals of Mathematical Statistics , volume =
-
[33]
J. C. Spall , title =. IEEE Transactions on Automatic Control , volume =
-
[34]
IEEE transactions on automatic control , volume =
Observers for multivariable systems , author =. IEEE transactions on automatic control , volume =. 2003 , publisher =
work page 2003
-
[35]
Observers for multivariable systems , author =. 1966 , publisher =
work page 1966
-
[36]
Output feedback stabilization of a class of
Ne. Output feedback stabilization of a class of. IEEE Transactions on Automatic Control , volume =. 2000 , publisher =
work page 2000
- [37]
-
[38]
2022 American Control Conference (ACC) , pages =
Controller confidentiality for nonlinear systems under sensor attacks , author =. 2022 American Control Conference (ACC) , pages =. 2022 , organization =
work page 2022
-
[39]
On the region of attraction of nonlinear quadratic systems , author =. Automatica , volume =. 2007 , publisher =
work page 2007
-
[40]
2018 IEEE conference on decision and control (CDC) , pages =
Secure control of wide-area power systems: Confidentiality and integrity threats , author =. 2018 IEEE conference on decision and control (CDC) , pages =. 2018 , organization =
work page 2018
-
[41]
2017 American Control Conference (ACC) , pages =
Linear systems with quadratic outputs , author =. 2017 American Control Conference (ACC) , pages =. 2017 , organization =
work page 2017
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.