Recognition: no theorem link
Sensing-Aided Secure Multicast in Two-Level Rotatable Antenna-Enabled ISAC Systems: Modeling and Optimization
Pith reviewed 2026-05-12 00:51 UTC · model grok-4.3
The pith
A two-level rotatable antenna scheme with sensing improves secrecy rates in multicast ISAC by jointly rotating arrays and elements to boost user signals while suppressing eavesdroppers over CRB-derived uncertainty regions.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
In the two-level rotatable antenna-enabled ISAC architecture, array-level and element-wise rotations are jointly optimized with analog beamforming to maintain strong gains toward legitimate users and create a low-gain region over the eavesdropper angular uncertainty interval, where the uncertainty region is built from the Cramér-Rao bound on sensing-based angle estimates, yielding higher CRB-aware max-min secrecy rates for multicast.
What carries the argument
The two-level rotatable antenna architecture, in which array-level rotations and element-wise rotations are jointly exploited with analog beamforming and guided by a probabilistic angular uncertainty region constructed from the Cramér-Rao bound on eavesdropper angle estimates.
Load-bearing premise
The probabilistic angular uncertainty region built from the Cramér-Rao bound sufficiently represents the true eavesdropper directions, and the Jensen-based lower bound plus smooth approximation stays tight enough for the alternating optimization to produce near-optimal solutions.
What would settle it
Placing actual eavesdroppers at angles outside the modeled high-probability uncertainty interval and measuring whether the realized secrecy rates fall significantly below the optimized values, or checking whether the Jensen lower bound remains close to the true secrecy rate in detailed numerical trials.
Figures






read the original abstract
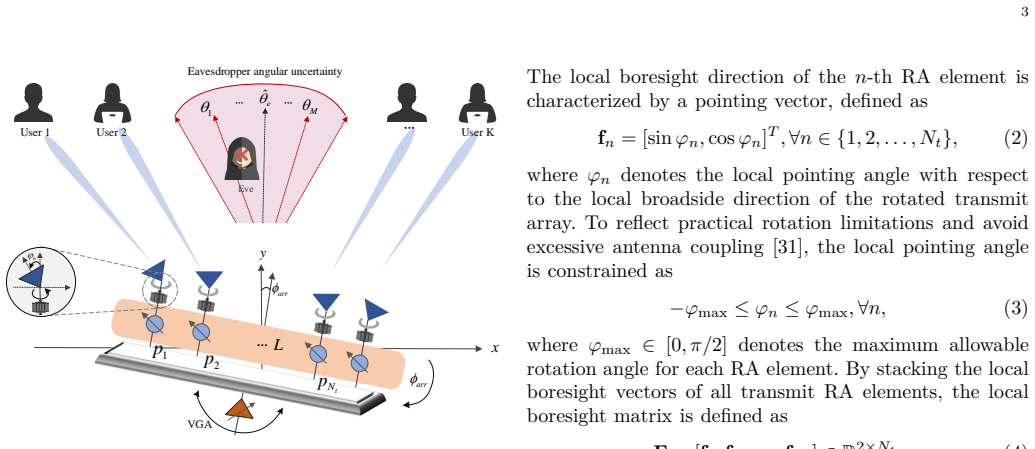
In physical layer security, the channel state information (CSI) of passive eavesdroppers is usually difficult to obtain, which has motivated sensing-aided secure communication (SASC). However, in secure multicast scenarios, conventional fixed-position antennas (FPAs) provide limited spatial flexibility for simultaneously serving multiple legitimate users and suppressing leakage toward possible eavesdropper directions. Motivated by this, a novel two-level rotatable antenna (RA)-enabled sensing-aided secure multicast scheme is proposed in this paper. In the proposed architecture, array-level and element-wise rotations are jointly exploited with analog beamforming for user enhancement and leakage suppression. To characterize imperfect eavesdropper sensing, the maximum likelihood estimator and the corresponding Cram\'er-Rao bound (CRB) are derived to quantify the angular estimation accuracy. Based on the derived CRB, a probabilistic angular uncertainty region is constructed. A CRB-aware max-min secrecy-rate problem is then formulated by evaluating the eavesdropper leakage over sampled high-probability directions within this region. The non-convex problem is handled through a tractable lower-bound reformulation based on Jensen's inequality and smooth approximation, followed by an alternating optimization algorithm combining manifold optimization and projected-gradient updates. Simulation results show the effectiveness and robustness of the proposed scheme compared with various benchmarks. Beam patterns further reveal that array-level and element-wise rotations play complementary roles in maintaining strong gains toward legitimate users and forming a low-gain region over the eavesdropper angular uncertainty interval.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The manuscript proposes a two-level rotatable antenna (RA) architecture for sensing-aided secure multicast in ISAC systems. It derives the maximum likelihood estimator (MLE) and Cramér-Rao bound (CRB) for eavesdropper angular estimation, constructs a probabilistic angular uncertainty region from the CRB, formulates a CRB-aware max-min secrecy-rate optimization problem by sampling high-probability directions within the region, solves the resulting non-convex problem via a Jensen inequality lower bound, smooth approximation, and alternating optimization combining manifold optimization with projected-gradient updates, and validates the approach through simulations demonstrating performance gains over benchmarks and the complementary roles of array-level and element-wise rotations in beam patterns.
Significance. If the CRB-based uncertainty model and optimization approximations prove sufficiently accurate, the work advances physical-layer security for integrated sensing and communication by exploiting rotatable antennas to provide spatial flexibility in multicast settings with sensing-derived eavesdropper information. The demonstration of complementary rotation levels for user enhancement and leakage suppression offers a concrete design insight for future ISAC systems.
major comments (3)
- [§IV] §IV (Optimization formulation and reformulation): The Jensen-based lower bound and smooth approximation to the max-min secrecy-rate objective are introduced without a quantitative bound on the approximation gap or tightness analysis relative to the original problem; this is load-bearing for the central claim that the alternating manifold+projected-gradient solver yields near-optimal rotatable-antenna configurations.
- [§III] §III (CRB and uncertainty region construction): The probabilistic angular uncertainty region is built from the CRB Gaussian approximation and a finite number of sampled high-probability directions, yet no analysis is provided of sensitivity to the sample count or validity of the Gaussian tail assumption under finite sensing snapshots; this directly affects the worst-case secrecy-rate guarantee against actual MLE error distributions.
- [§V] §V (Simulation results): The reported robustness and complementary rotation gains rest on simulations whose sensing snapshot count, exact channel models, eavesdropper MLE error statistics, and statistical significance are not detailed; without these, it is impossible to confirm that the optimized solutions remain secure when eavesdropper directions are drawn from the true finite-sample distribution rather than the CRB surrogate.
minor comments (2)
- [Notation and §II] A table summarizing all optimization variables, rotation angles, and beamforming parameters would improve readability of the system model.
- [§V] Beam pattern figures in §V would benefit from explicit overlay of the CRB-derived uncertainty interval to visually support the low-gain region claim.
Simulated Author's Rebuttal
We thank the referee for the constructive and detailed comments, which have helped us improve the clarity and rigor of the manuscript. We provide point-by-point responses to the major comments below, indicating the revisions made to address the concerns raised.
read point-by-point responses
-
Referee: [§IV] §IV (Optimization formulation and reformulation): The Jensen-based lower bound and smooth approximation to the max-min secrecy-rate objective are introduced without a quantitative bound on the approximation gap or tightness analysis relative to the original problem; this is load-bearing for the central claim that the alternating manifold+projected-gradient solver yields near-optimal rotatable-antenna configurations.
Authors: We agree that an explicit quantitative bound on the approximation gap would strengthen the theoretical foundation. The Jensen inequality yields a valid and conservative lower bound on the expected secrecy rate over the uncertainty region, while the smooth approximation facilitates differentiability for the manifold optimization. Deriving a closed-form gap bound is non-trivial given the dependence on the joint optimization variables. In the revised manuscript, we have added a subsection in §IV discussing the approximation quality and included numerical results in §V quantifying the gap (typically below 0.4 bits/s/Hz across tested scenarios). We have also strengthened the convergence analysis of the alternating algorithm to better support the near-optimality of the obtained solutions. revision: partial
-
Referee: [§III] §III (CRB and uncertainty region construction): The probabilistic angular uncertainty region is built from the CRB Gaussian approximation and a finite number of sampled high-probability directions, yet no analysis is provided of sensitivity to the sample count or validity of the Gaussian tail assumption under finite sensing snapshots; this directly affects the worst-case secrecy-rate guarantee against actual MLE error distributions.
Authors: The CRB-based Gaussian approximation is standard for constructing uncertainty sets in sensing-aided PHY security literature, but we acknowledge its asymptotic nature and potential deviation for small snapshot counts. In the revised manuscript, we have added a sensitivity study in §III and §V varying the sample count (10 to 200) and comparing the CRB-derived region against empirical MLE error histograms obtained via Monte Carlo trials. A new remark discusses the validity of the Gaussian tail assumption for moderate-to-large snapshot counts (N ≥ 30), with supporting figures showing that the worst-case secrecy rate remains robust under the empirical distribution. revision: yes
-
Referee: [§V] §V (Simulation results): The reported robustness and complementary rotation gains rest on simulations whose sensing snapshot count, exact channel models, eavesdropper MLE error statistics, and statistical significance are not detailed; without these, it is impossible to confirm that the optimized solutions remain secure when eavesdropper directions are drawn from the true finite-sample distribution rather than the CRB surrogate.
Authors: We thank the referee for pointing out the insufficient simulation details. The revised §V now explicitly states the sensing snapshot count (N=50), the channel models (Rician fading with K=10 dB for legitimate users and Rayleigh for the eavesdropper), and the MLE error statistics derived from 5000 Monte Carlo realizations. All results are averaged over 1000 independent channel realizations with error bars indicating one standard deviation. We have also added a new set of curves comparing performance when eavesdropper angles are drawn from the empirical finite-sample MLE distribution versus the CRB surrogate, confirming that positive secrecy rates are maintained and the reported robustness holds. revision: yes
Circularity Check
No significant circularity in derivation chain
full rationale
The paper derives the MLE and corresponding CRB directly from the sensing model to quantify angular estimation accuracy, then uses the CRB to construct a probabilistic uncertainty region for formulating the CRB-aware max-min secrecy-rate optimization problem. The non-convex problem is addressed via a Jensen lower-bound reformulation and smooth approximation, solved by alternating manifold optimization and projected-gradient updates. These are standard sequential modeling, bounding, and algorithmic steps with independent content; the final simulation claims of effectiveness are presented as empirical validation rather than quantities forced by construction to equal the inputs. No self-definitional reductions, fitted inputs renamed as predictions, load-bearing self-citations, or imported uniqueness theorems appear in the described chain.
Axiom & Free-Parameter Ledger
free parameters (1)
- number of sampled high-probability directions
axioms (2)
- standard math Jensen's inequality provides a valid lower bound for the expectation over the eavesdropper angle distribution
- domain assumption The Cramér-Rao bound accurately quantifies the angular estimation variance for the maximum-likelihood estimator under the assumed sensing model
Reference graph
Works this paper leans on
-
[1]
Secure transmission with multi- ple antennas—Part II: The MIMOME wiretap channel,
A. Khisti and G. W. Wornell, “Secure transmission with multi- ple antennas—Part II: The MIMOME wiretap channel,” IEEE Trans. Inf. Theory, vol. 56, no. 11, pp. 5515-5532, Nov. 2010
work page 2010
-
[2]
Security and privacy for 6G: A survey on prospective technologies and challenges,
V. -L. Nguyen et al., “Security and privacy for 6G: A survey on prospective technologies and challenges,” IEEE Commun. Surveys Tuts., vol. 23, no. 4, pp. 2384-2428, 4th Quart., 2021
work page 2021
-
[3]
Y. Liu et al., “Physical layer security for next generation wireless networks: Theories, technologies, and challenges,” IEEE Commun. Surveys Tuts., vol. 19, no. 1, pp. 347-376, 1st Quart., 2017
work page 2017
-
[4]
W. Xiong et al., “Enhancing physical layer security in MIMO systems assisted by beyond-diagonal reconfigurable intelligent surfaces,” IEEE Trans. Commun., vol. 73, no. 11, pp. 10824- 10839, Nov. 2025
work page 2025
-
[5]
W. Xiong et al., “Constant-modulus secure analog beamforming for an IRS-assisted communication system with large-scale antenna array,” IEEE Trans. Inf. Forensics Security, vol. 20, pp. 2957-2969, 2025. 14
work page 2025
-
[6]
J. Lin et al., “Physical-layer security for proximal legitimate user and eavesdropper: A frequency diverse array beamforming approach,” IEEE Trans. Inf. Forensics Security, vol. 13, no. 3, pp. 671-684, Mar. 2018
work page 2018
-
[7]
Time-invariant and localized secure reception with sequential multicarrier receive-FDA,
A. Akkoc et al., “Time-invariant and localized secure reception with sequential multicarrier receive-FDA,” IEEE Trans. Anten- nas and Propag., vol. 71, no. 9, pp. 7064-7072, Sept. 2023
work page 2023
-
[8]
Joint secure transmit beamforming designs for integrated sensing and communication systems,
J. Chu et al., “Joint secure transmit beamforming designs for integrated sensing and communication systems,” IEEE Trans. Veh. Technol., vol. 72, no. 4, pp. 4778-4791, Apr. 2023
work page 2023
-
[9]
Artificial-noise-aided optimal beamforming in layered physical layer security,
W. Zhang et al., “Artificial-noise-aided optimal beamforming in layered physical layer security,” IEEE Commun. Lett., vol. 23, no. 1, pp. 72-75, Jan. 2019
work page 2019
-
[10]
Physical layer security for integrated sensing and communication: A survey,
T. Matsumine et al., “Physical layer security for integrated sensing and communication: A survey,” IEEE Open J. Commun. Soc., vol. 6, pp. 6690-6743, 2025
work page 2025
-
[11]
Sensing-assisted eavesdropper estimation: An ISAC breakthrough in physical layer security,
N. Su et al., “Sensing-assisted eavesdropper estimation: An ISAC breakthrough in physical layer security,” IEEE Trans. Wireless Commun., vol. 23, no. 4, pp. 3162-3174, Apr. 2024
work page 2024
-
[12]
Sensing for secure communication in ISAC: Protocol design and beamforming optimization,
Y. Cao et al., “Sensing for secure communication in ISAC: Protocol design and beamforming optimization,” IEEE Trans. Wireless Commun., vol. 24, no. 2, pp. 1207-1220, Feb. 2025
work page 2025
-
[13]
Sensing-aided near-field secure communications with mobile eavesdroppers,
Y. Xu et al., “Sensing-aided near-field secure communications with mobile eavesdroppers,” IEEE Trans. Wireless Commun., vol. 24, no. 11, pp. 9338-9356, Nov. 2025
work page 2025
-
[14]
Sensing-assisted secure communications: A rate- splitting approach,
P. Liu et al., “Sensing-assisted secure communications: A rate- splitting approach,” IEEE Internet Things J., vol. 12, no. 20, pp. 42876-42890, 15 Oct.15, 2025
work page 2025
-
[15]
Two-Stage transmission framework and re- source allocation for mmWave-ISAC systems,
S. Zhang et al., “Two-Stage transmission framework and re- source allocation for mmWave-ISAC systems,” IEEE Trans. Wireless Commun., vol. 25, pp. 5797-5810, 2026
work page 2026
-
[16]
Hybrid STAR-RIS-assisted short packet ISAC systems: Transmission Paradigm and Resource Optimization,
S. Zhang et al., “Hybrid STAR-RIS-assisted short packet ISAC systems: Transmission Paradigm and Resource Optimization,” IEEE Trans. Wireless Commun., vol. 25, pp. 14069-14085, 2026
work page 2026
-
[17]
6D movable antenna enhanced wireless network via discrete position and rotation optimization,
X. Shao et al., “6D movable antenna enhanced wireless network via discrete position and rotation optimization,” IEEE J. Sel. Areas Commun., vol. 43, no. 3, pp. 674-687, Mar. 2025
work page 2025
-
[18]
X. Shao et al., “6DMA enhanced wireless network with flexible antenna position and rotation: Opportunities and challenges,” IEEE Commun. Mag., vol. 63, no. 4, pp. 121-128, Apr. 2025
work page 2025
-
[19]
6D movable antenna based on user distribution: Modeling and optimization,
X. Shao et al., “6D movable antenna based on user distribution: Modeling and optimization,” IEEE Trans. Wireless Commun., vol. 24, no. 1, pp. 355-370, Jan. 2025
work page 2025
-
[20]
Rotatable antenna enabled wireless com- munication and sensing: Opportunities and challenges,
B. Zheng et al., “Rotatable antenna enabled wireless com- munication and sensing: Opportunities and challenges,” IEEE Wireless Commun., early access, 2026
work page 2026
-
[21]
Rotatable antenna-enabled wireless commu- nication: Modeling and optimization,
B. Zheng et al., “Rotatable antenna-enabled wireless commu- nication: Modeling and optimization,” IEEE Trans. Commun., vol. 74, pp. 6825-6842, 2026
work page 2026
-
[22]
Rotatable antenna-enabled secure wireless com- munication,
L. Dai et al., “Rotatable antenna-enabled secure wireless com- munication,” IEEE Wireless Commun. Lett., vol. 14, no. 11, pp. 3440-3444, Nov. 2025
work page 2025
-
[23]
Rotatable array-aided hybrid beamforming for integrated sensing and communication,
Z. Wang et al., “Rotatable array-aided hybrid beamforming for integrated sensing and communication,” IEEE Internet Things J., vol. 13, no. 7, pp. 14364-14377, 1 Apr.1, 2026
work page 2026
-
[24]
Rotatable antennas for integrated sensing and communications,
C. Zhou et al., “Rotatable antennas for integrated sensing and communications,” IEEE Wireless Commun. Lett., vol. 14, no. 9, pp. 2838-2842, Sept. 2025
work page 2025
-
[25]
Rotatable antennas for near-field integrated sensing and communication,
Y. Zhang et al., “Rotatable antennas for near-field integrated sensing and communication,” IEEE Trans. Wireless Commun., vol. 25, pp. 10986-11001, 2026
work page 2026
-
[26]
Rotatable and movable antenna-enabled near- field integrated sensing and communication,
Y. Sun et al., “Rotatable and movable antenna-enabled near- field integrated sensing and communication,” IEEE Internet Things J., vol. 12, no. 21, pp. 45119-45132, 1 Nov.1, 2025
work page 2025
-
[27]
S. K. Mohammed et al., “Single-user beamforming in large-scale MISO systems with per-antenna constant-envelope constraints: The doughnut channel,” IEEE Trans. Wireless Commun., vol. 11, no. 11, pp. 3992-4005, Nov. 2012
work page 2012
-
[28]
J. Pan et al., “Constant envelope precoding for single-user large- scale MISO channels: Efficient precoding and optimal designs,” IEEE J. Sel. Topics Signal Process., vol. 8, no. 5, pp. 982-995, Oct. 2014
work page 2014
-
[29]
Constant envelope precoding for MIMO systems,
S. Zhang et al., “Constant envelope precoding for MIMO systems,” IEEE Trans. Commun., vol. 66, no. 1, pp. 149-162, Jan. 2018
work page 2018
-
[30]
Secure analog beamforming for multi-user MISO systems with movable antennas,
W. Xiong et al., “Secure analog beamforming for multi-user MISO systems with movable antennas,” IEEE Trans. Wireless Commun., vol. 25, pp. 8164-8178, 2026
work page 2026
-
[31]
R. Kumar et al., “Mutual coupling reduction techniques for UWB-MIMO antenna for band notch characteristics: A com- prehensive review,” Wireless Pers. Commun., vol. 131, pp. 1207- 1247, May 2023
work page 2023
-
[32]
C. A. Balanis, Antenna Theory: Analysis and Design. John Wiley & sons, 2015
work page 2015
-
[33]
Synesthesia of machines (SoM)-enhanced ISAC precoding for vehicular networks with double dynamics,
Z. Yang et al., “Synesthesia of machines (SoM)-enhanced ISAC precoding for vehicular networks with double dynamics,” IEEE Trans. Commun., vol. 73, no. 9, pp. 7967-7984, Sep. 2025
work page 2025
-
[34]
Random ISAC signals deserve dedicated Precod- ing,
S. Lu et al., “Random ISAC signals deserve dedicated Precod- ing,” IEEE Trans. Signal Process., vol. 72, pp. 3453-3469, 2024
work page 2024
-
[35]
V. Chandola et al., “Anomaly detection: A survey,” ACM Comput. Surveys, vol. 41, no. 3, pp. 1-58, Jul. 2009
work page 2009
-
[36]
S. Boyd and L. Vandenberghe, Convex Optimization. Cam- bridge, U.K.: Cambridge Univ. Press, 2004
work page 2004
-
[37]
Nesterov, Introductory Lectures on Convex Optimization: A Basic Course, vol
Y. Nesterov, Introductory Lectures on Convex Optimization: A Basic Course, vol. 87. Cham, Switzerland: Springer, 2013
work page 2013
-
[38]
Alternating minimization algorithms for hybrid precoding in millimeter wave MIMO systems,
X. Yu et al., “Alternating minimization algorithms for hybrid precoding in millimeter wave MIMO systems,” IEEE J. Sel. Topics Signal Process., vol. 10, no. 3, pp. 485-500, Apr. 2016
work page 2016
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.