Recognition: 2 theorem links
· Lean TheoremLUDB++: Enabling LUDB for the Analysis of Shaped Feedforward FIFO Networks using Network Calculus
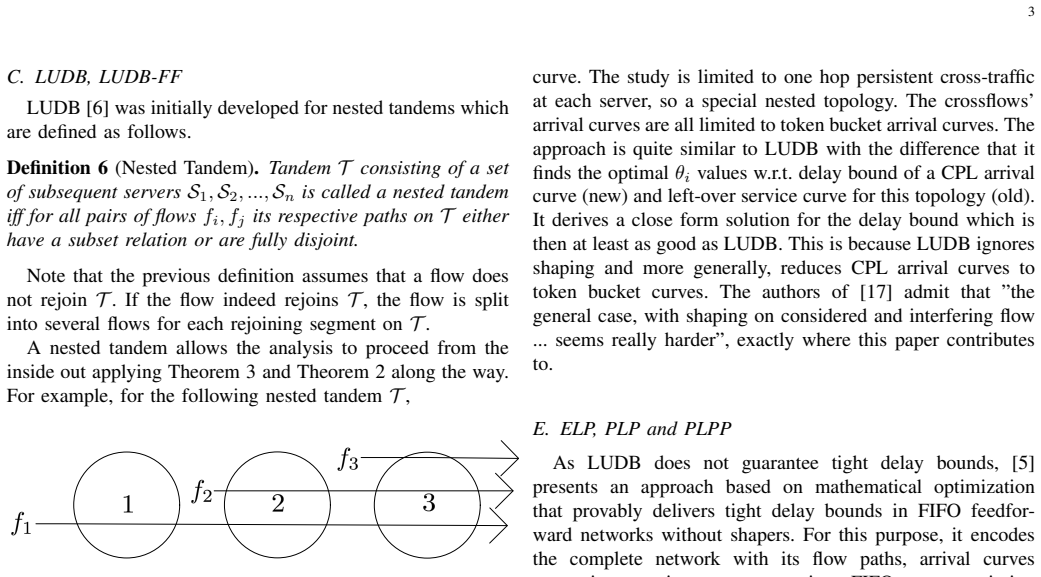
Pith reviewed 2026-05-12 01:45 UTC · model grok-4.3
The pith
LUDB++ extends the least upper delay bound method to include shaper constraints and compute tighter latency bounds for feedforward FIFO networks.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
The paper establishes that modifying the least upper delay bound analysis to incorporate the rate and burst limits imposed by shapers at each location yields more accurate upper bounds on end-to-end latency for flows in feedforward FIFO networks. The original LUDB method ignored these shaping effects and therefore produced looser bounds. Numerical tests confirm that the new LUDB++ bounds are tighter than those from standard LUDB and, in the majority of tested setups, tighter than those obtained from the exponential linear program approach.
What carries the argument
LUDB++ is the extended least-upper-delay-bound computation that folds shaping parameters (rate and burst) into the arrival and service curve constraints used for each flow and each server.
If this is right
- Tighter bounds allow network designers to allocate smaller buffers and schedules while still meeting latency targets.
- The method applies to both simple line topologies and branched tree topologies common in time-sensitive networking.
- In most of the 130 tested cases LUDB++ produces better results than the exponential linear program method.
- Resource utilization improves because overestimation of required capacity is reduced.
- The technique supports direct analysis of networks that already contain rate limiters.
Where Pith is reading between the lines
- Similar shaping adjustments could be applied to other network-calculus bound techniques that currently ignore shapers.
- If shaper parameters contain uncertainty the bounds would need additional margins not computed here.
- The accuracy gains suggest that earlier designs without shaping awareness were unnecessarily conservative.
- The approach could be tested on larger networks or mixed traffic patterns to check scalability.
Load-bearing premise
The analysis assumes that shaping parameters are known exactly at every shaper and that the network topology contains no feedback loops.
What would settle it
A concrete falsifier would be a simulation or hardware measurement on one of the evaluated topologies where the observed worst-case latency exceeds the bound produced by LUDB++.
Figures













read the original abstract
This paper discusses how latency guarantees for non-cyclic (feedforward) First-In-First-Out (FIFO) networks with shapers can be computed within the Network Calculus (NC) framework. Shapers are methods implemented in software or hardware and may reside inside the network and at the endpoint which constrain the rate and maximum packet sizes for the transmission of specific data streams (flows) or groups thereof. Shaping can improve latencies and is an important aspect of Time-Sensitive Networking (TSN). Several methods in NC exist to analyze FIFO networks. Among them is the Least Upper Delay Bound (LUDB) methodology. So far, LUDB does not incorporate shaping assumptions into its analysis. This paper addresses this gap resulting in the new methodology called LUDB++. The evaluation on a set of different line topologies and a tree topology with a total of 130 configurations shows that LUDB++ delivers more accurate latency bounds compared to LUDB. Moreover, the Exponential Linear Program (ELP) method, which considers FIFO and shaping inside the network, yields the most accurate bounds to this date. ELP is superseded by LUDB++ for most of cases by a margin of up to 9.13%.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The manuscript extends the Least Upper Delay Bound (LUDB) method from Network Calculus to incorporate traffic shapers (rate and burst constraints) in feedforward FIFO networks, producing LUDB++. It evaluates the approach on 130 configurations of line and tree topologies and reports that LUDB++ yields tighter latency bounds than plain LUDB and, in most cases, improves upon the Exponential Linear Program (ELP) method by up to 9.13%.
Significance. If the derivation correctly preserves valid upper bounds while tightening them, LUDB++ would supply a lighter-weight alternative to ELP for analyzing shaped TSN networks under the feedforward assumption. The scale of the evaluation (130 configurations) is a positive feature that allows direct numerical comparison across methods.
major comments (2)
- [Evaluation section (130 configurations)] The central claim that LUDB++ produces 'more accurate' bounds rests on numerical tightness versus LUDB and ELP, yet the evaluation provides no cross-validation against simulated worst-case latencies or exact analysis on the same topologies. Without this check, it is impossible to confirm that the incorporation of shaping parameters does not introduce an unsound relaxation that invalidates the upper-bound guarantee.
- [Abstract and Evaluation] The abstract and evaluation description supply no derivation steps showing how shaping (rate and burst) is folded into the LUDB equations, nor any error bars or sensitivity analysis on the reported 9.13% margin. This omission makes it impossible to assess whether the improvement is load-bearing or an artifact of the specific topologies chosen.
minor comments (1)
- [Methodology] Notation for shaped arrival curves and service curves should be introduced with explicit equations early in the methodology section to aid readability.
Simulated Author's Rebuttal
We thank the referee for the constructive feedback on our manuscript extending LUDB to shaped feedforward FIFO networks. We address the major comments point by point below, providing clarifications on the theoretical soundness and outlining revisions to improve presentation and analysis.
read point-by-point responses
-
Referee: [Evaluation section (130 configurations)] The central claim that LUDB++ produces 'more accurate' bounds rests on numerical tightness versus LUDB and ELP, yet the evaluation provides no cross-validation against simulated worst-case latencies or exact analysis on the same topologies. Without this check, it is impossible to confirm that the incorporation of shaping parameters does not introduce an unsound relaxation that invalidates the upper-bound guarantee.
Authors: The incorporation of shaping preserves the upper-bound property because LUDB++ extends the original LUDB linear program by adding standard network calculus arrival-curve constraints that model the shaper's rate and burst limits at each hop. These constraints tighten the feasible set of arrival processes without relaxing any worst-case assumptions, so the optimized solution remains a valid least upper delay bound. The full derivation appears in Section 3. We agree that simulation cross-validation would be valuable; however, exact worst-case simulation for the evaluated topologies is computationally intractable. We will add a dedicated paragraph in the revised evaluation section explaining the theoretical soundness and the practical barriers to simulation. revision: partial
-
Referee: [Abstract and Evaluation] The abstract and evaluation description supply no derivation steps showing how shaping (rate and burst) is folded into the LUDB equations, nor any error bars or sensitivity analysis on the reported 9.13% margin. This omission makes it impossible to assess whether the improvement is load-bearing or an artifact of the specific topologies chosen.
Authors: The derivation of shaping integration is given in full in Section 3, where the LUDB equations are updated to include shaper-induced arrival curves. We will revise the abstract to include a concise statement of this extension. The 9.13% figure is the maximum observed improvement over ELP across the 130 deterministic configurations; because each result is exact for its parameter set, error bars are not applicable. We will add a sensitivity analysis subsection to the evaluation that varies utilization, burst sizes, and topology depth to demonstrate that the gains are consistent rather than topology-specific artifacts. revision: yes
Circularity Check
LUDB++ extends standard NC FIFO analysis with shaper constraints; no derivation reduces to fitted inputs or self-citation by construction
full rationale
The paper defines LUDB++ by incorporating known shaper rate/burst parameters into the existing LUDB methodology for feedforward FIFO networks using standard network calculus operations (arrival curves, service curves, and delay bound computations). The 130-configuration evaluation compares the resulting numerical upper bounds against LUDB and ELP but does not fit parameters to the target result or rename a known pattern; the comparison is external. No load-bearing step equates the claimed tighter bounds to the inputs by definition, and the feedforward/shaper assumptions are stated explicitly rather than smuggled via self-citation. The derivation chain remains self-contained against external NC benchmarks.
Axiom & Free-Parameter Ledger
Lean theorems connected to this paper
-
IndisputableMonolith/Cost/FunctionalEquation.leanwashburn_uniqueness_aczel unclear?
unclearRelation between the paper passage and the cited Recognition theorem.
LUDB++ ... MSLC ... Theorem 5 (Delay Bound Shaped Arrival Curve and MSLC Service Curve) ... inf θ≥0 hdev(α2, β2 ⊗ (β1 ⊖θ α1)↑)
-
IndisputableMonolith/Foundation/RealityFromDistinction.leanreality_from_one_distinction unclear?
unclearRelation between the paper passage and the cited Recognition theorem.
evaluation on ... 130 configurations ... LUDB++ delivers more accurate latency bounds ... up to 9.13%
What do these tags mean?
- matches
- The paper's claim is directly supported by a theorem in the formal canon.
- supports
- The theorem supports part of the paper's argument, but the paper may add assumptions or extra steps.
- extends
- The paper goes beyond the formal theorem; the theorem is a base layer rather than the whole result.
- uses
- The paper appears to rely on the theorem as machinery.
- contradicts
- The paper's claim conflicts with a theorem or certificate in the canon.
- unclear
- Pith found a possible connection, but the passage is too broad, indirect, or ambiguous to say the theorem truly supports the claim.
Reference graph
Works this paper leans on
-
[1]
802.1q–ieee standard for local and metropolitan area networks– bridges and bridged networks,
IEEE, “802.1q–ieee standard for local and metropolitan area networks– bridges and bridged networks,” 2018. [Online]. Available: https: //standards.ieee.org/standard/802-1Q-2018.html
work page 2018
-
[2]
A calculus for network delay. i. network elements in isolation,
R. L. Cruz, “A calculus for network delay. i. network elements in isolation,”IEEE Transactions on information theory, vol. 37, no. 1, pp. 114–131, 2002
work page 2002
-
[3]
A calculus for network delay. ii. network analysis,
——, “A calculus for network delay. ii. network analysis,”IEEE Transactions on information theory, vol. 37, no. 1, pp. 132–141, 2002
work page 2002
-
[4]
Trade-off between accuracy and tractability of network calculus in fifo networks,
A. Bouillard, “Trade-off between accuracy and tractability of network calculus in fifo networks,”Performance Evaluation, vol. 153, p. 102250, 2022
work page 2022
-
[5]
Exact worst-case delay in fifo-multiplexing feed-forward networks,
A. Bouillard and G. Stea, “Exact worst-case delay in fifo-multiplexing feed-forward networks,”IEEE/ACM Transactions on Networking, vol. 23, no. 5, pp. 1387–1400, 2014
work page 2014
-
[6]
A methodology for computing end-to-end delay bounds in fifo-multiplexing tandems,
L. Lenzini, E. Mingozzi, and G. Stea, “A methodology for computing end-to-end delay bounds in fifo-multiplexing tandems,”Performance Evaluation, vol. 65, no. 11-12, pp. 922–943, 2008
work page 2008
-
[7]
Network calculus for bounding delays in feedforward networks of FIFO queueing systems,
A. Scheffler and S. Bondorf, “Network calculus for bounding delays in feedforward networks of FIFO queueing systems,” inProc. of the International Conference on Quantitative Evaluation of Systems (QEST), August 2021
work page 2021
-
[8]
A. Bouillard, M. Boyer, and E. Le Corronc,Deterministic network calculus: From theory to practical implementation. John Wiley & Sons, 2018
work page 2018
-
[9]
J.-Y . Le Boudec and P. Thiran,Network calculus: a theory of deter- ministic queuing systems for the internet. Springer LNCS, 2001, vol. 2050
work page 2001
-
[10]
On cyclic dependencies and regulators in time-sensitive networks,
L. Thomas, J.-Y . Le Boudec, and A. Mifdaoui, “On cyclic dependencies and regulators in time-sensitive networks,” in2019 IEEE Real-Time Systems Symposium (RTSS). IEEE, 2019, pp. 299–311
work page 2019
-
[11]
J. Grieu, “Analyse et ´evaluation de techniques de commutation ethernet pour l’interconnexion des syst `emes avioniques,”PhD Thesis, 2004
work page 2004
-
[12]
A. Mifdaoui and T. Leydier, “Beyond the accuracy-complexity trade- offs of compositional analyses using network calculus for complex networks,” in10th International Workshop on Compositional Theory and Technology for Real-Time Embedded Systems (co-located with RTSS 2017), 2017, pp. pp–1
work page 2017
-
[13]
Efficient and accurate handling of periodic flows in time-sensitive networks,
S. M. Tabatabaee, M. Boyer, J.-Y . Le Boudec, and J. Migge, “Efficient and accurate handling of periodic flows in time-sensitive networks,” in 2023 IEEE 29th Real-Time and Embedded Technology and Applications Symposium (RTAS). IEEE, 2023, pp. 303–315
work page 2023
-
[14]
Admission shaping with network calculus,
A. Bouillard, “Admission shaping with network calculus,”IEEE Net- working Letters, 2024
work page 2024
-
[15]
Tight end-to- end per-flow delay bounds in fifo multiplexing sink-tree networks,
L. Lenzini, L. Martorini, E. Mingozzi, and G. Stea, “Tight end-to- end per-flow delay bounds in fifo multiplexing sink-tree networks,” Performance Evaluation, vol. 63, no. 9-10, pp. 956–987, 2006
work page 2006
-
[16]
Numerical analysis of worst-case end-to-end delay bounds in fifo tandem networks,
L. Bisti, L. Lenzini, E. Mingozzi, and G. Stea, “Numerical analysis of worst-case end-to-end delay bounds in fifo tandem networks,”Real-Time Systems, vol. 48, no. 5, pp. 527–569, 2012
work page 2012
-
[17]
Half-modeling of shaping in fifo net with network calculus,
M. Boyer, “Half-modeling of shaping in fifo net with network calculus,” in18th International Conference on Real-Time and Network Systems, 2010, pp. 59–68
work page 2010
-
[18]
Chang,Performance guarantees in communication networks
C.-S. Chang,Performance guarantees in communication networks. Springer Science & Business Media, 2012
work page 2012
-
[19]
Network calculus with flow prolongation – a feedforward fifo analysis enabled by ml,
F. Geyer, A. Scheffler, and S. Bondorf, “Network calculus with flow prolongation – a feedforward fifo analysis enabled by ml,”IEEE Transactions on Computers, vol. 72, no. 1, pp. 97–110, 2023
work page 2023
-
[20]
Searching for upper delay bounds in FIFO multiplexing feedforward networks,
A. Scheffler, J. B. Schmitt, and S. Bondorf, “Searching for upper delay bounds in FIFO multiplexing feedforward networks,” inthe 30th International Conference on Real-Time Networks and Systems (RTNS 2022), June 2022
work page 2022
-
[21]
Short paper: Analyzing fifo- multiplexing tandems with network calculus and a tailored grid search,
A. Scheffler, S. Bondorf, and J. B. Schmitt, “Short paper: Analyzing fifo- multiplexing tandems with network calculus and a tailored grid search,” inthe 34th International Teletraffic Congress (ITC 2022), September 2022
work page 2022
-
[22]
The deterministic network calculus analysis: Reliability insights and performance improvements,
A. Scheffler, M. F ¨ogen, and S. Bondorf, “The deterministic network calculus analysis: Reliability insights and performance improvements,” inProc. of the IEEE International Workshop on Computer Aided Modeling and Design of Communication Links and Networks (CAMAD), 2018. Alexander Schefflerreceived the MSc degree in computer science from TU (now RPTU) Kai...
work page 2018
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.