Recognition: 2 theorem links
· Lean TheoremSecret Communication with Plausible Deniability
Pith reviewed 2026-05-12 02:24 UTC · model grok-4.3
The pith
Secret communication can provide plausible deniability only if directional messages reveal at most whether the state is above or below a cutoff.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
Under single-crossing preferences, plausible deniability holds when every action induced by the sender's message can be rationalized from the receiver's baseline information alone. When combined with secrecy, directional baseline messages restrict frontier communication to structures that reveal at most whether the state lies above or below a cutoff. The paper also identifies conditions under which a greatest feasible communication structure exists and can be constructed explicitly.
What carries the argument
Frontier communication structures that jointly satisfy secrecy (message independent of the state) and plausible deniability (actions rationalizable by baseline information alone) under directional baseline messages.
If this is right
- Plausible deniability restricts additional communication exactly when the baseline message is directional.
- For directional messages, the most informative feasible structures reveal only a binary cutoff signal about the state.
- A greatest feasible communication structure exists and admits an explicit construction under the identified conditions.
- Joint information structures satisfying both secrecy and plausible deniability are fully characterized.
Where Pith is reading between the lines
- The cutoff restriction suggests that optimal secret signals in repeated interactions would take the form of simple threshold rules rather than richer partitions.
- The same logic may apply to settings with multiple receivers who share different baseline information, limiting the feasible secret layers accordingly.
- In mechanism design, contracts or policies could embed these structures to allow private adjustments while preserving the appearance of public rationality.
Load-bearing premise
Single-crossing preferences make every induced action rationalizable from baseline information without reference to the hidden message.
What would settle it
A concrete example, under single-crossing preferences, in which a directional secret message induces an action that cannot be justified using only the receiver's baseline information.
Figures


read the original abstract
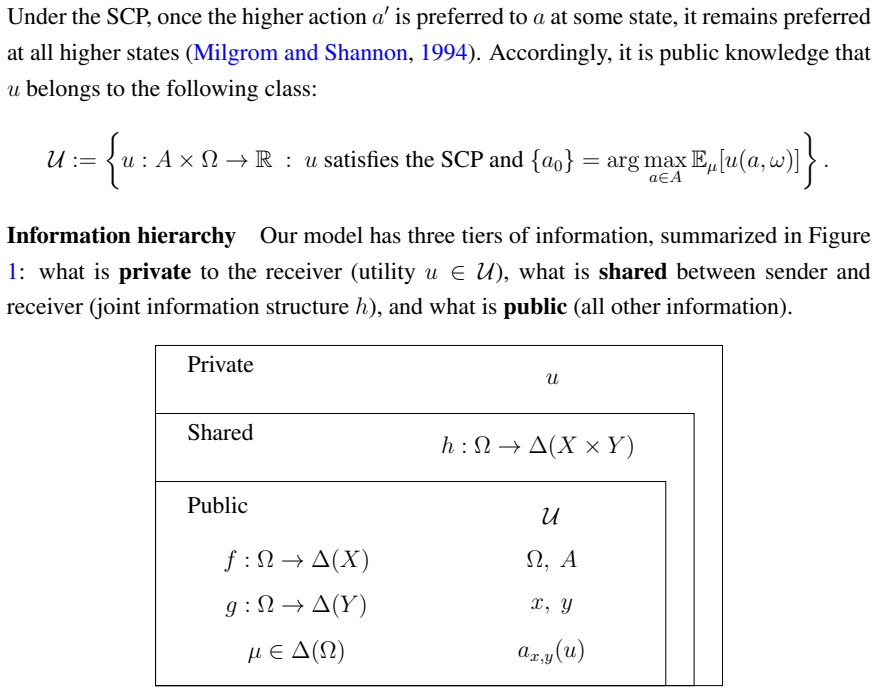
Communication is secret if a message is independent of the state; however, the receiver's subsequent action may still reveal that she has acted on hidden information. This paper studies when secret communication can also provide plausible deniability: under single-crossing preferences, every action induced by the sender's message must be rationalizable using the receiver's baseline information alone. We characterize joint information structures that satisfy both secrecy and plausible deniability. We show that plausible deniability restricts communication exactly when the baseline message is directional -- meaning its likelihood is monotone in the state. Combining this restriction with secrecy, we show that, for directional messages, frontier communication reveals at most whether the state lies above or below a cutoff. Finally, we identify conditions under which a greatest feasible communication structure exists and can be constructed explicitly in a simple way.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
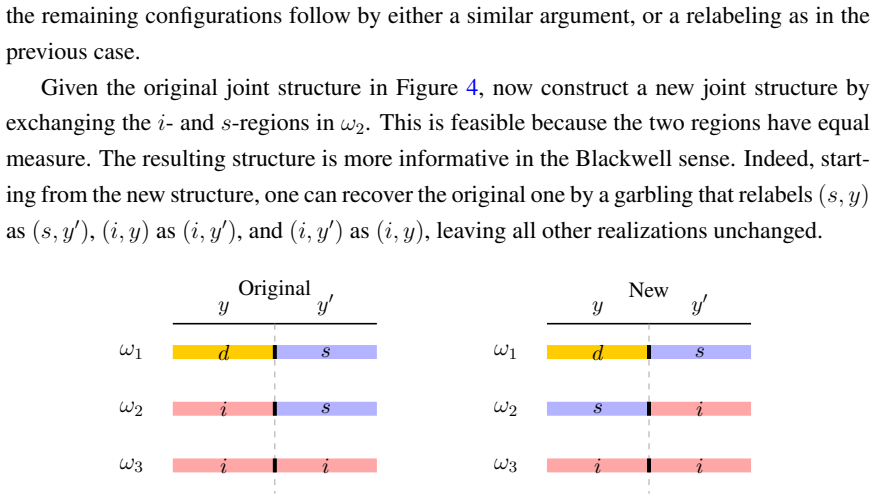
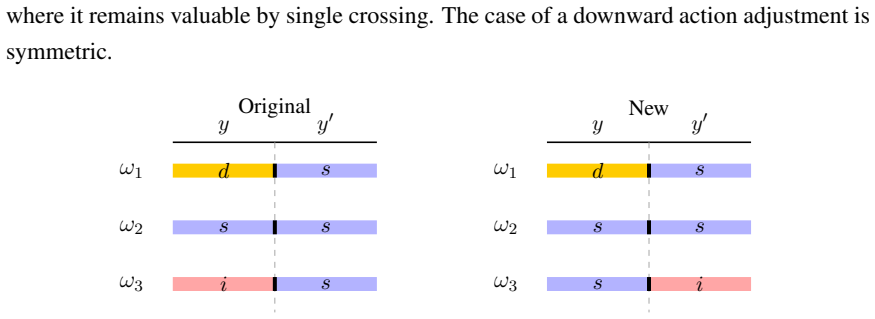
Summary. The paper studies secret communication (messages independent of the state) that also satisfies plausible deniability under single-crossing preferences, where every action induced by the sender's message is rationalizable using only the receiver's baseline information. It characterizes the admissible joint information structures satisfying both conditions. For directional baseline messages (monotone likelihood ratios in the state), the combination restricts frontier communication to revealing at most whether the state lies above or below a cutoff. The paper further identifies conditions for existence of a greatest feasible communication structure and provides an explicit construction.
Significance. If the characterizations hold, this provides a precise delineation of the limits imposed by secrecy and deniability on strategic communication, which is a useful contribution to information design and mechanism design in economics. The explicit construction of the maximal feasible structure is a particular strength, as it offers a concrete and potentially implementable object. The result on cutoff revelations for directional messages yields a clean, testable restriction.
minor comments (2)
- The definition of plausible deniability (every induced action rationalizable from baseline information alone) is load-bearing; a short remark comparing it to related notions in the cheap-talk or information-design literature would aid readers.
- The abstract states the characterizations and the cutoff result without proof sketches; ensure the main text or appendix makes the deductive steps from single-crossing and monotonicity fully explicit for verification.
Simulated Author's Rebuttal
We thank the referee for their careful reading of the manuscript and for recommending minor revision. The referee's summary accurately reflects the paper's focus on characterizing joint information structures that satisfy both secrecy and plausible deniability under single-crossing preferences, as well as the key results on directional baseline messages and the explicit construction of maximal feasible structures. We appreciate the positive assessment of the contribution to information design.
Circularity Check
No significant circularity; derivation is deductive from definitions
full rationale
The paper derives characterizations of admissible joint information structures directly from its explicit definitions of secrecy and plausible deniability, together with the single-crossing preference assumption. The key result—that directional messages under these constraints reveal at most a cutoff—follows by logical implication from the stated conditions without any parameter fitting, self-referential equations, or load-bearing self-citations. The explicit construction of the greatest feasible structure is obtained by applying the identified restrictions, keeping the argument self-contained and independent of the target claims.
Axiom & Free-Parameter Ledger
axioms (1)
- domain assumption Single-crossing preferences
Lean theorems connected to this paper
-
IndisputableMonolith/Cost/FunctionalEquation.leanwashburn_uniqueness_aczel unclearWe show that plausible deniability restricts communication exactly when the baseline message is directional—meaning its likelihood is monotone in the state. ... for directional messages, frontier communication reveals at most whether the state lies above or below a cutoff.
-
IndisputableMonolith/Foundation/AbsoluteFloorClosure.leanabsolute_floor_iff_bare_distinguishability unclearLemma 2. ... If ϕ(z|ω) is decreasing and non-constant in ω, R_ϕ(z) = {a : a ≤ a0}.
Reference graph
Works this paper leans on
-
[1]
Antic, Nemanja, Archishman Chakraborty, and Rick Harbaugh (2025) “Subversive Con- versations,”Journal of Political Economy, 133 (5), 1621–1660, 10.1086/734130. Athey, Susan and Jonathan Levin (2018) “The value of information in monotone decision problems,”Research in Economics, 72 (1), 101–116. B¨orgers, Tilman, Angel Hernando-Veciana, and Daniel Kr¨ahmer...
-
[2]
Milgrom, Paul and Chris Shannon (1994) “Monotone Comparative Statics,”Econometrica, 62 (1), 157–180,http://www.jstor.org/stable/2951479. Shannon, C. E. (1949) “Communication Theory of Secrecy Systems,”The Bell System Technical Journal, 28 (4), 656–715, 10.1002/j.1538-7305.1949.tb00928.x. Strack, Philipp and Kai Hao Yang (2024) “Privacy-Preserving Signals,...
-
[3]
Inferentially-Private Private Information,
46 Wang, Shuaiqi, Shuran Zheng, Zinan Lin, Giulia Fanti, and Zhiwei Steven Wu (2024) “Inferentially-Private Private Information,”arXiv preprint arXiv:2410.17095. Xu, Zhang and Wei Zhao (2025a) “Privacy-Constrained Signals,”arXiv preprint arXiv:2511.21196. (2025b) “Privacy Structure and Blackwell Frontier,”arXiv preprint arXiv:2511.10226. Zhu, Shuguang (20...
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.