Recognition: no theorem link
An Approximation Algorithm for 2-Vertex-Connectivity via Cycle-Restricted 2-Edge-Covers
Pith reviewed 2026-05-12 02:23 UTC · model grok-4.3
The pith
The paper gives an algorithm that finds a minimum-edge 2-vertex-connected spanning subgraph within a factor of 95/72 plus a small epsilon.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
By computing a 2-edge-cover without certain forbidden cycle components and using it as the starting point, the algorithm produces a 2-vertex-connected spanning subgraph whose number of edges is at most 95/72 + ε times the size of an optimum solution.
What carries the argument
A cycle-restricted 2-edge-cover (a minimum 2-edge-cover that avoids specific cycle components), which serves as an initial solution that can be transformed into a 2-vertex-connected spanning subgraph while preserving the improved ratio.
Load-bearing premise
That a 2-edge-cover without the forbidden cycle components can be computed in polynomial time and that the conversion step to a 2-vertex-connected subgraph preserves the claimed approximation ratio.
What would settle it
A concrete graph on which every cycle-restricted 2-edge-cover converts into a 2-vertex-connected subgraph whose edge count exceeds 95/72 + ε times the optimum, or a proof that no polynomial-time algorithm exists for finding such a restricted cover.
Figures










read the original abstract
In the 2-Vertex-Connected Spanning Subgraph problem (2-VCSS), we are given an undirected graph $G$, and the objective is to find a 2-vertex-connected spanning subgraph $S$ of $G$ with the minimum number of edges. In the context of survivable network design, 2-VCSS is one of the most fundamental and well-studied problems. There has been active research on improving the approximation ratio of algorithms, and the current best ratio is $\frac{4}{3}$, achieved by Bosch-Calvo, Grandoni, and Jabal Ameli. In this paper, we improve the approximation ratio to $\frac{95}{72}+\varepsilon$ ($<1.32$). The key idea in our algorithm is to introduce a 2-edge-cover without certain cycle components, and use it as an initial solution.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The paper presents a (95/72 + ε)-approximation algorithm for the 2-Vertex-Connected Spanning Subgraph (2-VCSS) problem. It improves on the prior 4/3 bound by first computing a minimum-cost 2-edge-cover that excludes certain cycle components (specifically, cycles that would violate vertex-connectivity properties in the subsequent step) and then converting this cover into a 2-vertex-connected spanning subgraph via a sequence of augmentations and edge additions while controlling the total cost.
Significance. If the claimed ratio and polynomial-time computability hold, the result advances the approximation landscape for a core survivable-network-design problem. The cycle-restriction technique on 2-edge-covers is a concrete algorithmic idea that could transfer to related connectivity problems; the manuscript supplies an explicit construction and charging analysis rather than relying on black-box oracles.
major comments (2)
- [§3.2] §3.2, Algorithm 1: the procedure for obtaining a cycle-restricted 2-edge-cover invokes a minimum-cost 2-edge-cover oracle and then removes forbidden cycles; the analysis claims this removal increases cost by at most a (1+ε) factor, but the charging argument (Lemma 3.4) appears to double-count edges that belong to both a removed cycle and a later augmentation path. A concrete counter-example graph where the double-counting occurs would clarify whether the 95/72 bound survives.
- [§4.1] §4.1, Theorem 4.2: the conversion from the restricted 2-edge-cover to a 2-vertex-connected subgraph is shown to add at most (23/72 + ε) times the optimum; however, the proof relies on the absence of the forbidden cycles to bound the number of new edges needed for vertex-connectivity. It is not immediate that every optimal 2-VC solution can be charged against a cycle-restricted cover without losing the factor; an explicit comparison to the previous 4/3 analysis would strengthen the claim.
minor comments (3)
- [Abstract] The abstract states the ratio as 95/72 + ε but does not define ε; a sentence clarifying that ε > 0 is an arbitrary positive constant (standard in PTAS-style results) would help readers.
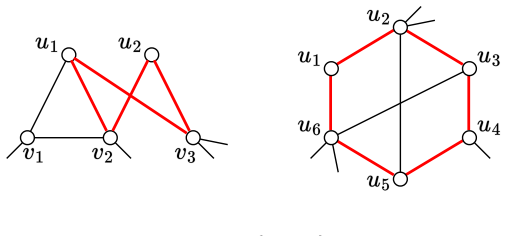
- [Figure 2] Figure 2 caption refers to 'forbidden cycle types' without listing them; adding the three cycle patterns from Definition 2.3 would make the figure self-contained.
- [§2] Notation: the symbol OPT is used both for the optimum 2-VC cost and for the optimum 2-edge-cover cost; introducing OPT_VC and OPT_EC would eliminate ambiguity in the charging lemmas.
Simulated Author's Rebuttal
We appreciate the referee's thorough review and constructive feedback on our paper. The comments highlight important aspects of the analysis that we will clarify in the revised version. Below, we address each major comment point by point.
read point-by-point responses
-
Referee: [§3.2] §3.2, Algorithm 1: the procedure for obtaining a cycle-restricted 2-edge-cover invokes a minimum-cost 2-edge-cover oracle and then removes forbidden cycles; the analysis claims this removal increases cost by at most a (1+ε) factor, but the charging argument (Lemma 3.4) appears to double-count edges that belong to both a removed cycle and a later augmentation path. A concrete counter-example graph where the double-counting occurs would clarify whether the 95/72 bound survives.
Authors: We thank the referee for pointing out this potential issue in the charging argument. Upon re-examination, the edges in the removed cycles are charged only to the cost of the initial 2-edge-cover, and the subsequent augmentations use different edges that are not part of the removed cycles due to the cycle-restriction property. The analysis in Lemma 3.4 separates the charging for the (1+ε) factor from the augmentation costs in later sections. To address this, we will add a remark clarifying that no edge is charged twice because removed cycles are disjoint from the augmentation paths used in the conversion step. We do not believe a counter-example exists, as the restriction ensures the properties hold. revision: partial
-
Referee: [§4.1] §4.1, Theorem 4.2: the conversion from the restricted 2-edge-cover to a 2-vertex-connected subgraph is shown to add at most (23/72 + ε) times the optimum; however, the proof relies on the absence of the forbidden cycles to bound the number of new edges needed for vertex-connectivity. It is not immediate that every optimal 2-VC solution can be charged against a cycle-restricted cover without losing the factor; an explicit comparison to the previous 4/3 analysis would strengthen the claim.
Authors: We agree that an explicit comparison would be helpful. In the revised manuscript, we will include a new paragraph in Section 4.1 that contrasts our approach with the 4/3-approximation of Bosch-Calvo et al. Specifically, their analysis uses a general 2-edge-cover and requires more edges for augmentation to ensure vertex-connectivity, leading to the 4/3 factor. By excluding the forbidden cycles (which are cycles that do not help in bridging articulation points), our restricted cover allows a tighter bound on the number of additional edges needed, resulting in the improved 23/72 + ε additive term. Regarding charging against an optimal 2-VC solution, the proof shows that the cost of the restricted cover is at most (1+ε) OPT, and the augmentation cost is bounded relative to that, preserving the overall ratio. We will make this charging explicit. revision: yes
Circularity Check
No significant circularity; algorithmic construction is self-contained
full rationale
The paper presents a polynomial-time approximation algorithm for 2-VCSS that begins by computing a 2-edge-cover excluding certain cycle components and then converts it into a 2-vertex-connected spanning subgraph while preserving the claimed ratio of 95/72 + ε. No equations, fitted parameters, or self-referential definitions appear in the provided abstract or description. The central steps are algorithmic procedures (computing the restricted cover, then augmenting to 2-vertex-connectivity) whose correctness is argued via standard charging or potential analysis rather than by reducing a prediction back to the input by construction. Prior 4/3 result is cited from independent authors (Bosch-Calvo et al.), so no self-citation load-bearing or uniqueness theorem imported from the present authors occurs. The derivation chain does not contain any of the enumerated circular patterns.
Axiom & Free-Parameter Ledger
Reference graph
Works this paper leans on
-
[1]
M. Bosch-Calvo, M. Garg, F. Grandoni, F. Hommelsheim, A. J. Ameli, and A. Lindermayr. A 5/4-approximation for two-edge connectivity. InProceedings of the 57th Annual ACM 23 Symposium on Theory of Computing, STOC ’25, page 653–664, New York, NY, USA, 2025. Association for Computing Machinery
work page 2025
-
[2]
M. Bosch-Calvo, F. Grandoni, and A. J. Ameli. A PTAS for triangle-free 2-matching. arXiv preprint arXiv:2311.11869, 2023
-
[3]
M. Bosch-Calvo, F. Grandoni, and A. J. Ameli. A 4/3 approximation for 2-vertex- connectivity.TheoretiCS, Volume 4, Jun 2025
work page 2025
-
[4]
J. Cheriyan, A. Seb˝ o, and Z. Szigeti. Improving on the 1.5-approximation of a smallest 2-edge connected spanning subgraph.SIAM Journal on Discrete Mathematics, 14(2):170– 180, 2001
work page 2001
-
[5]
J. Cheriyan and R. Thurimella. Approximating minimum-sizek-connected spanning sub- graphs via matching. InProceedings of the 37th Annual Symposium on Foundations of Computer Science, FOCS ’96, page 292, USA, 1996. IEEE Computer Society
work page 1996
-
[6]
G. Cornu´ ejols and W. Pulleyblank. A matching problem with side conditions.Discrete Mathematics, 29(2):135–159, 1980
work page 1980
-
[7]
A. Czumaj and A. Lingas. On approximability of the minimum-costk-connected spanning subgraph problem. InProceedings of the Tenth Annual ACM-SIAM Symposium on Dis- crete Algorithms, SODA ’99, page 281–290, USA, 1999. Society for Industrial and Applied Mathematics
work page 1999
-
[8]
C. G. Fernandes. A better approximation ratio for the minimum sizek-edge-connected spanning subgraph problem.Journal of Algorithms, 28(1):105–124, 1998
work page 1998
-
[9]
H. N. Gabow and S. R. Gallagher. Iterated rounding algorithms for the smallestk-edge connected spanning subgraph.SIAM Journal on Computing, 41(1):61–103, 2012
work page 2012
-
[10]
H. N. Gabow, M. X. Goemans, E. Tardos, and D. P. Williamson. Approximating the smallestk-edge connected spanning subgraph by LP-rounding.Networks, 53(4):345–357, 2009
work page 2009
-
[11]
M. Garg, F. Grandoni, and A. J. Ameli. Improved approximation for two-edge-connectivity. InProceedings of the 34th Annual ACM-SIAM Symposium on Discrete Algorithms (SODA 2023), pages 2368–2410, 2023
work page 2023
-
[12]
N. Garg, S. Vempala, and A. Singla. Improved approximation algorithms for biconnected subgraphs via better lower bounding techniques. InProceedings of the Fourth Annual ACM-SIAM Symposium on Discrete Algorithms, SODA ’93, page 103–111, USA, 1993. Society for Industrial and Applied Mathematics
work page 1993
-
[13]
F. Grandoni, A. J. Ameli, and V. Traub. Breaching the 2-approximation barrier for the forest augmentation problem. InProceedings of the 54th Annual ACM SIGACT Symposium on Theory of Computing (STOC 2022), page 1598–1611, 2022
work page 2022
-
[14]
Hartvigsen.Extensions of Matching Theory
D. Hartvigsen.Extensions of Matching Theory. PhD thesis, Carnegie Mellon University,
-
[15]
Available at https://david-hartvigsen.net
-
[16]
D. Hartvigsen. Finding triangle-free 2-factors in general graphs.Journal of Graph Theory, 106(3):581–662, 2024. 24
work page 2024
-
[17]
K. Heeger and J. Vygen. Two-connected spanning subgraphs with at most 10 7 OP Tedges. SIAM Journal on Discrete Mathematics, 31(3):1820–1835, 2017
work page 2017
-
[18]
F. Hommelsheim, A. Lindermayr, and Z. Liu. A better-than-5/4-approximation for two- edge connectivity. InProceedings of the 36th Annual ACM-SIAM Symposium on Discrete Algorithms (SODA 2026), pages 1468–1520, 2026
work page 2026
-
[19]
C. Hunkenschr¨ oder, S. Vempala, and A. Vetta. A 4/3-approximation algorithm for the minimum 2-edge connected subgraph problem.ACM Transactions on Algorithms, 15(4):1– 28, 2019
work page 2019
-
[20]
K. Jain. A factor 2 approximation algorithm for the generalized Steiner network problem. Combinatorica, 21:39–60, 1998
work page 1998
-
[21]
S. Khuller and U. Vishkin. Biconnectivity approximations and graph carvings.J. ACM, 41(2):214–235, Mar. 1994
work page 1994
-
[22]
Y. Kobayashi and T. Noguchi. An approximation algorithm for two-edge-connected sub- graph problem via triangle-free two-edge-cover. In34th International Symposium on Algo- rithms and Computation (ISAAC 2023), pages 49:1–49:10, 2023
work page 2023
-
[23]
Y. Kobayashi and T. Noguchi. Validating a PTAS for triangle-free 2-matching via a simple decomposition theorem. In2025 Symposium on Simplicity in Algorithms (SOSA), pages 281–289, 2025
work page 2025
-
[24]
A. Seb˝ o and J. Vygen. Shorter tours by nicer ears: 7/5-approximation for the graph- tsp, 3/2 for the path version, and 4/3 for two-edge-connected subgraphs.Combinatorica, 34(5):597–629, 2014
work page 2014
-
[25]
V. Traub and R. Zenklusen. A better-than-2 approximation for weighted tree augmentation. InProceedings of the IEEE 62nd Annual Symposium on Foundations of Computer Science (FOCS 2021), pages 1–12, 2022
work page 2021
-
[26]
V. Traub and R. Zenklusen. A (1.5+ε)-approximation algorithm for weighted connectivity augmentation. InProceedings of the 55th Annual ACM Symposium on Theory of Computing (STOC 2023), STOC 2023, page 1820–1833, 2023. A Remarks on Lemma 2 In the original statement of Lemma 2, i.e., [22, Corollary 4.1], it is assumed thatGhas no parallel edges. In particula...
work page 2023
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.