Recognition: 2 theorem links
· Lean TheoremLure-and-Reveal: An Exposure Framework for Stealthy Deception Attack in Multi-sensor Uncertain Systems
Pith reviewed 2026-05-12 03:26 UTC · model grok-4.3
The pith
Injecting random shakes into control inputs creates detectable discrepancies that expose stealthy deception attacks in multi-sensor Kalman filter systems.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
By switching to a suspect mode and injecting random exposure shakes into the control inputs, the defender produces a mismatch between its own state estimates and those the attacker can maintain, so that the attack can no longer remain stealthy; an explicit exposure condition gives the smallest shake magnitude that forces detection in finite time, while a compensable condition guarantees the added signals do not degrade nominal performance.
What carries the argument
The suspect mode, in which random exposure shakes are added to nominal control inputs to generate an observable discrepancy between defender and attacker state estimates.
If this is right
- Stealthy attacks on multi-sensor fusion become detectable in finite time once shake magnitude satisfies the exposure condition.
- Nominal closed-loop performance is preserved when the shakes also meet the compensable condition.
- The framework requires no changes to existing sensor interfaces or fusion software.
- The same exposure mechanism applies to other uncertain cyber-physical systems that use error-state Kalman filtering.
Where Pith is reading between the lines
- The method could be combined with existing residual-based detectors to reduce the required shake magnitude.
- If an attacker gains partial knowledge of the shake statistics, the exposure condition may need to be strengthened or made adaptive.
- Real-time computation of the minimum shake magnitude could be tested on embedded hardware for UAV or autonomous vehicle platforms.
- The framework might extend to other state estimators such as particle filters or moving-horizon estimators in multi-sensor setups.
Load-bearing premise
The defender can add shakes to the control inputs that the attacker neither observes nor compensates for in real time, and the underlying system model remains sufficiently accurate for the derived exposure and compensable conditions to apply.
What would settle it
A closed-loop experiment in which shakes are applied at the calculated minimum magnitude yet the attacker's manipulated estimates remain statistically indistinguishable from the defender's over the full finite-time window, or in which performance metrics exceed the compensable bounds.
Figures



read the original abstract
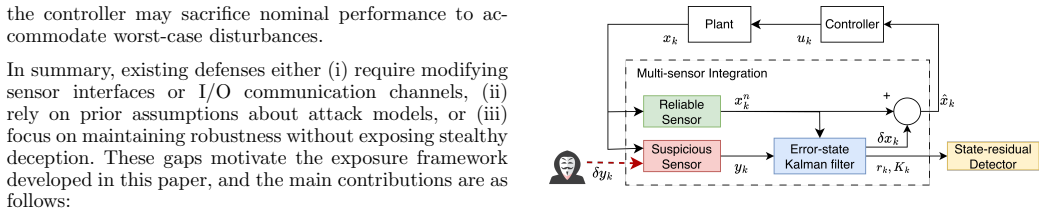
Multi-sensor integration via error-state Kalman filter (KF) is widely employed for precise state estimation in cyber-physical systems (CPSs). However, this integration exposes the system to stealthy deception attacks that render conventional detection mechanisms ineffective. We propose an exposure framework to actively reveal such stealthy attacks without modifying sensor interfaces. The framework introduces a suspect mode in which the defender injects random exposure shakes into the nominal control inputs, thus creating a discrepancy between the defender's true state estimates and the attacker's manipulated state estimates, preventing the attack from remaining stealthy. We further derive an explicit exposure condition that characterizes the minimum shake magnitude to guarantee the finite-time exposure and a compensable condition that ensures the shakes do not degrade closed-loop performance. Simulation results based on a GNSS/INS-integrated UAV system verify the effectiveness of the proposed framework.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The manuscript proposes a 'Lure-and-Reveal' exposure framework for detecting stealthy deception attacks in multi-sensor uncertain systems that employ error-state Kalman filters. In a suspect mode, the defender injects random exposure shakes into nominal control inputs to create discrepancies between the defender's true state estimates and the attacker's manipulated estimates. Explicit exposure and compensable conditions are derived to guarantee finite-time attack exposure while preserving closed-loop performance. The approach is verified through simulations on a GNSS/INS-integrated UAV system.
Significance. If the key assumptions hold, the work offers a proactive, sensor-interface-preserving defense against stealthy attacks in CPS, with explicit conditions that could inform implementation in uncertain multi-sensor setups. The simulation verification on a realistic UAV platform supports practical relevance in aerospace control and security applications.
major comments (2)
- [Exposure condition derivation] The exposure condition (characterizing minimum shake magnitude for finite-time residual growth) is derived under the assumption that the attacker crafts false data using only the nominal unshaken control input. No robustness margin or analysis is provided against partial observability of actuator commands or inference of shakes from observed state evolution, which directly undermines the discrepancy mechanism and the finite-time exposure guarantee.
- [Theoretical conditions and simulation verification] The compensable condition and overall finite-time exposure claim lack explicit error bounds, full step-by-step derivation details, and validation of the unobservability assumption for the uncertain system model. This leaves the central claim only partially supported, as the simulation results do not address adaptive attacker scenarios.
minor comments (2)
- [Abstract and Introduction] The abstract and introduction could more explicitly contrast the proposed framework with prior stealthy attack detection methods to clarify novelty.
- [Notation and model section] Notation for the uncertain system dynamics and shake injection could be standardized and cross-referenced more clearly in the conditions.
Simulated Author's Rebuttal
We thank the referee for the constructive and detailed review of our manuscript. The comments on the threat model assumptions and the need for additional theoretical rigor and simulation coverage are well taken. We provide point-by-point responses below and will incorporate clarifications and extensions in the revised version.
read point-by-point responses
-
Referee: [Exposure condition derivation] The exposure condition (characterizing minimum shake magnitude for finite-time residual growth) is derived under the assumption that the attacker crafts false data using only the nominal unshaken control input. No robustness margin or analysis is provided against partial observability of actuator commands or inference of shakes from observed state evolution, which directly undermines the discrepancy mechanism and the finite-time exposure guarantee.
Authors: The exposure condition is derived under our stated threat model, in which the attacker generates false measurements using only the nominal (unshaken) control input because the random shakes are generated internally by the defender and are not part of any transmitted signal. This matches standard assumptions in active defense literature for deception attacks on CPS. In the GNSS/INS UAV setting, actuator commands are typically not directly observable to an external attacker, supporting the partial-observability premise. Inference of shakes from observed state evolution is hindered by the combination of process noise, model uncertainty, and the small random magnitude of the shakes, which prevents precise real-time compensation. Nevertheless, we agree that an explicit robustness margin would strengthen the finite-time guarantee. In the revision we will add a dedicated subsection that derives a conservative shake-magnitude bound accounting for bounded inference error and partial actuator observability. revision: partial
-
Referee: [Theoretical conditions and simulation verification] The compensable condition and overall finite-time exposure claim lack explicit error bounds, full step-by-step derivation details, and validation of the unobservability assumption for the uncertain system model. This leaves the central claim only partially supported, as the simulation results do not address adaptive attacker scenarios.
Authors: We acknowledge that the manuscript would benefit from expanded derivation details. In the revised manuscript we will supply the complete step-by-step derivations of both the exposure and compensable conditions, including explicit error bounds obtained from the Kalman-filter residual dynamics under shaken inputs. The unobservability of the shakes follows from the rank deficiency of the augmented observability matrix when the random input is treated as an unknown disturbance within the existing uncertainty set; we will include this rank-condition validation. The UAV simulations confirm finite-time exposure for the non-adaptive stealthy deception attacks considered in the threat model. We will augment the simulation section with additional runs that incorporate bounded adaptive behavior (e.g., attackers that attempt to estimate shake statistics) and will explicitly state the limitation that fully arbitrary adaptive strategies lie outside the current scope and may require complementary defenses. revision: yes
Circularity Check
No circularity: exposure and compensable conditions derived from KF dynamics
full rationale
The paper's central derivations start from the standard error-state Kalman filter equations for multi-sensor integration, the deception attack model, and the injected random shakes in the suspect mode. The exposure condition (minimum shake magnitude for finite-time residual growth) and compensable condition (performance bound) are obtained by analyzing the resulting discrepancy between defender and attacker state estimates under the given uncertainty bounds. These steps use explicit system matrices and residual propagation rules without fitting parameters to the target exposure outcome, without self-referential definitions of the quantities being proved, and without load-bearing self-citations that presuppose the result. The framework remains self-contained against external benchmarks such as standard KF innovation statistics and closed-loop stability margins.
Axiom & Free-Parameter Ledger
axioms (2)
- domain assumption Multi-sensor integration via error-state Kalman filter is widely employed for precise state estimation in CPSs and exposes the system to stealthy deception attacks.
- domain assumption The defender can inject random exposure shakes into nominal control inputs without modifying sensor interfaces.
Lean theorems connected to this paper
-
IndisputableMonolith/Cost/FunctionalEquation.leanwashburn_uniqueness_aczel unclearexposure shake sequence ... min ¯u ≥ 1/∥B∥ (2¯T(1−ρ)/c(1−ρ^kexp) + 2¯w + ¯T) (Thm 1); compensability ¯u ≤ (1−ρ)ε − c¯w / (c∥B∥) (Thm 2)
Reference graph
Works this paper leans on
-
[1]
C.M. Ahmed, V.R. Palleti, and V.K. Mishra. A practical physical watermarking approach to detect replay attacks in a CPS. Journal of Process Control, 116: 0 136--146, 2022
work page 2022
-
[2]
S. Athalye, F. Fotiadis, K.G. Vamvoudakis, and J. Hugues. An output feedback game-theoretic approach for defense against stealthy GNSS spoofing attacks. In 2024 American Control Conference (ACC), pages 3704--3709. IEEE, 2024
work page 2024
-
[3]
A. Bachrach, S. Prentice, R. He, and N. Roy. RANGE--robust autonomous navigation in GPS-denied environments. Journal of Field Robotics, 28(5): 0 644--666, 2011
work page 2011
-
[4]
C. Chen, H. Modares, K. Xie, F.L. Lewis, Y. Wan, and S. Xie. Reinforcement learning-based adaptive optimal exponential tracking control of linear systems with unknown dynamics. IEEE Transactions on Automatic Control, 64(11): 0 4423--4438, 2019
work page 2019
-
[5]
X. Geng, Y. Guo, K. Tang, W. Wu, Y. Ren, and G. Duan. A covert spoofing algorithm for SINS/GNSS tightly integrated navigation system. IEEE Transactions on Automation Science and Engineering, 2024
work page 2024
-
[6]
S. Kim, Y. Eun, and K.J. Park. Stealthy sensor attack detection and real-time performance recovery for resilient CPS. IEEE Transactions on Industrial Informatics, 17(11): 0 7412--7422, 2021
work page 2021
-
[7]
D.E. Miller and M.T. Shahab. Adaptive tracking with exponential stability and convolution bounds using vigilant estimation. Mathematics of Control, Signals, and Systems, 32(3): 0 241--291, 2020
work page 2020
-
[8]
Y. Mo, S. Weerakkody, and B. Sinopoli. Physical authentication of control systems: Designing watermarked control inputs to detect counterfeit sensor outputs. IEEE Control Systems Magazine, 35(1): 0 93--109, 2015
work page 2015
- [9]
-
[10]
D. Prashar, M. Rashid, S.T. Siddiqui, D. Kumar, A. Nagpal, A.S. AlGhamdi, and S.S. Alshamrani. SDSWSN---a secure approach for a hop-based localization algorithm using a digital signature in the wireless sensor network. Electronics, 10(24): 0 3074, 2021
work page 2021
-
[11]
D. Rangwani, D. Sadhukhan, S. Ray, M.K. Khan, and M. Dasgupta. An improved privacy preserving remote user authentication scheme for agricultural wireless sensor network. Transactions on Emerging Telecommunications Technologies, 32(3): 0 e4218, 2021
work page 2021
-
[12]
X.X. Ren and G.H. Yang. Kullback--Leibler divergence-based optimal stealthy sensor attack against networked linear quadratic Gaussian systems. IEEE Transactions on Cybernetics, 52(11): 0 11539--11548, 2021
work page 2021
-
[13]
W. Wan, H. Kim, N. Hovakimyan, L. Sha, and P.G. Voulgaris. A safety constrained control framework for UAVs in GPS denied environment. In 2020 59th IEEE Conference on Decision and Control (CDC), pages 214--219. IEEE, 2020
work page 2020
-
[14]
C. Wang, J. Huang, D. Wang, and F. Li. A secure strategy for a cyber physical system with multi-sensor under linear deception attack. Journal of the Franklin Institute, 358(13): 0 6666--6683, 2021
work page 2021
-
[15]
J. Wang, B. Ding, and J. Hu. Security control for LPV system with deception attacks via model predictive control: A dynamic output feedback approach. IEEE Transactions on Automatic Control, 66(2): 0 760--767, 2020
work page 2020
-
[16]
C. Wu, W. Yao, W. Luo, W. Pan, G. Sun, H. Xie, and L. Wu. A secure robot learning framework for cyber attack scheduling and countermeasure. IEEE Transactions on Robotics, 39(5): 0 3722--3738, 2023
work page 2023
-
[17]
B. Xiao, Q. Dong, D. Ye, L. Liu, and X. Huo. A general tracking control framework for uncertain systems with exponential convergence performance. IEEE/ASME Transactions on Mechatronics, 23(1): 0 111--120, 2017
work page 2017
-
[18]
D.Y. Zhang and X.J. Li. Stealthy attacks against distributed state estimation of stochastic multi-agent systems under composite attack detection mechanisms. Information Sciences, 672: 0 120584, 2024
work page 2024
- [19]
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.