Recognition: no theorem link
Chasing Small Sets Optimally Against Adaptive Adversaries
Pith reviewed 2026-05-12 03:39 UTC · model grok-4.3
The pith
A generalized doubling strategy yields an O(2^k)-competitive deterministic algorithm for chasing sets of size at most k in metric spaces.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
We give an O(2^k)-competitive deterministic algorithm for chasing sets of cardinality at most k in arbitrary metric spaces against adaptive adversaries. This bound is optimal even among randomized algorithms. The algorithm generalizes the classical doubling strategy and is strictly better than the generalized work function algorithm.
What carries the argument
The generalized doubling strategy, which extends the k=2 doubling approach to maintain and double coverage over potential sets of size k while ensuring the O(2^k) bound holds in arbitrary metrics.
If this is right
- The generalized work function algorithm is sub-optimal for chasing small sets.
- Slightly improved upper bounds hold for distributed asynchronous collective tree exploration.
- Slightly improved lower bounds hold for the k-taxi problem.
- The new recursive lower bound D_k is matched exactly by the algorithm for k=3.
Where Pith is reading between the lines
- Doubling generalizations may close similar competitive gaps in other online problems on metric spaces or layered graphs.
- The exact D_k values for small k could enable practical tuning of service systems or routing protocols where k is constant.
- Robustness against adaptive adversaries suggests the bound applies directly to dynamic request models in distributed computing.
Load-bearing premise
The generalized doubling strategy admits an O(2^k) competitive analysis that holds for arbitrary metric spaces and against adaptive adversaries.
What would settle it
A concrete metric space and adaptive sequence of k-sets for which the algorithm's total movement cost exceeds C times 2^k times the optimal offline cost for arbitrarily large C.
Figures







read the original abstract
We study deterministic online algorithms for the problem of chasing sets of cardinality at most $k$ in a metric space, also known as metrical service systems and equivalent to width-$k$ layered graph traversal. We resolve the 30-year-old gap of $\Omega(2^k)\cap O(k2^k)$ on the competitive ratio of this problem by giving an $O(2^k)$-competitive deterministic algorithm. This bound is optimal even among randomized algorithms against adaptive adversaries. We also (slightly) improve the deterministic lower bound to $D_k$, defined recursively by $D_1=1$ and $D_{k+1}=2D_k+\sqrt{8+8D_k}+3$, which we conjecture to be exactly tight. For $k=3$, we provide a matching upper bound of $D_3$. Our results imply slightly improved upper and lower bounds for distributed asynchronous collective tree exploration and for the $k$-taxi problem, respectively. Our algorithm generalizes the classical doubling strategy, previously known to be optimal for $k=2$. The previous best bound for general $k$ was achieved by the generalized work function algorithm (WFA), and was known to be tight for WFA. Our improved bound therefore implies that WFA is sub-optimal for chasing small sets.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The manuscript presents a deterministic online algorithm for chasing sets of cardinality at most k in arbitrary metric spaces (equivalent to width-k layered graph traversal). It claims an O(2^k)-competitive ratio against adaptive adversaries by generalizing the classical doubling strategy via recursive doubling phases and a potential-function charging argument; this closes the 30-year gap between the known Ω(2^k) lower bound and the prior O(k 2^k) upper bound from the generalized work-function algorithm. The paper also gives a new deterministic lower bound D_k (defined recursively) that is conjectured to be tight, proves a matching upper bound of D_3 for k=3, and notes improved bounds for distributed asynchronous collective tree exploration and the k-taxi problem.
Significance. If the analysis is correct, the result is a significant contribution to online algorithms: it resolves an open question on the competitive ratio of metrical service systems, demonstrates that the generalized WFA is suboptimal for this problem, and establishes optimality even against randomized algorithms and adaptive adversaries. The explicit potential-function argument that charges movement cost to the offline optimum while bounding phase transitions by O(2^k) in arbitrary metrics is a strength, as is the handling of adaptivity without hidden restrictions on the metric.
minor comments (3)
- [Abstract] Abstract: the statement that the new lower bound D_k is only a 'slight' improvement should be quantified by recalling the previous best lower bound and the precise asymptotic growth of D_k.
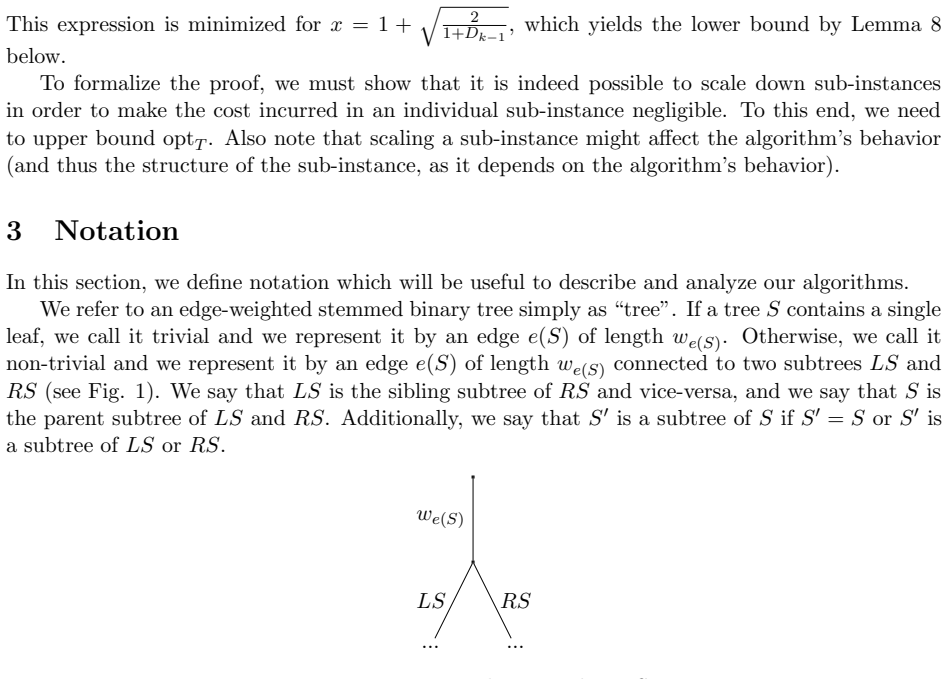
- [§3] The recursive definition of the algorithm (likely §3) would benefit from explicit pseudocode or a clear inductive description of how the doubling phases are instantiated for general k, including the base case and the rule for selecting the next phase center after an adversary move.
- [§4] The potential-function analysis (likely §4) should include a short remark confirming that the charging scheme remains valid when the adversary chooses the next k-set adaptively after observing the algorithm's position; while the text asserts this, a one-sentence pointer to the relevant induction step would help.
Simulated Author's Rebuttal
We thank the referee for their positive and insightful review of our manuscript. We are pleased that the referee acknowledges the significance of our results in closing the long-standing gap for the competitive ratio of chasing k-sets against adaptive adversaries. As no specific major comments were provided in the report, we have no points to address individually. We will make any necessary minor revisions as directed by the editor.
Circularity Check
No significant circularity detected in derivation chain
full rationale
The paper's central result is an explicit O(2^k)-competitive deterministic algorithm obtained by generalizing the classical doubling strategy, together with a self-contained potential-function analysis that charges movement costs to the offline optimum and bounds phase transitions by O(2^k). This analysis is stated to hold in arbitrary metric spaces against adaptive adversaries and does not rely on fitted parameters, self-citations, or reductions to prior results by the same authors. The improved lower bound D_k is defined recursively from first principles and is matched only for the special case k=3; neither step reduces by construction to the algorithm's inputs. The derivation is therefore independent and self-contained.
Axiom & Free-Parameter Ledger
axioms (2)
- domain assumption Inputs are sequences of sets of size at most k in an arbitrary metric space.
- domain assumption Competitive ratio is measured against an adaptive adversary.
Reference graph
Works this paper leans on
-
[1]
Marek Chrobak and Lawrence L. Larmore , title =. On-Line Algorithms, Proceedings of a. 1991 , url =
work page 1991
- [2]
-
[3]
ACM Transactions on Algorithms , volume=
Online metric algorithms with untrusted predictions , author=. ACM Transactions on Algorithms , volume=
-
[4]
Shortest Paths without a Map, but with an Entropic Regularizer , booktitle =
S. Shortest Paths without a Map, but with an Entropic Regularizer , booktitle =. 2022 , url =
work page 2022
-
[5]
Shortest paths without a map , journal =. 1991 , issn =. doi:https://doi.org/10.1016/0304-3975(91)90263-2 , url =
-
[6]
Searching in the Plane , journal =. 1993 , issn =. doi:https://doi.org/10.1006/inco.1993.1054 , url =
-
[7]
Asynchronous Collective Tree Exploration: a Distributed Algorithm, and a new Lower Bound , journal=
Romain Cosson and Laurent Massouli. Asynchronous Collective Tree Exploration: a Distributed Algorithm, and a new Lower Bound , journal=
-
[8]
Borodin, Allan and Linial, Nathan and Saks, Michael E. , title =. 1992 , issue_date =. doi:10.1145/146585.146588 , journal =
-
[9]
Amos Fiat and Dean P. Foster and Howard J. Karloff and Yuval Rabani and Yiftach Ravid and Sundar Vishwanathan , title =. 1998 , url =. doi:10.1137/S0097539795279943 , timestamp =
-
[10]
William R. Burley , title =. J. Algorithms , volume =. 1996 , url =. doi:10.1006/JAGM.1996.0024 , timestamp =
-
[11]
Elias Koutsoupias and Christos H. Papadimitriou , title =. J. 1995 , url =
work page 1995
-
[12]
Proceedings of the 51st Annual
Christian Coester and Elias Koutsoupias , title =. Proceedings of the 51st Annual. 2019 , url =
work page 2019
-
[13]
Mixing Predictions for Online Metric Algorithms , booktitle =
Antonios Antoniadis and Christian Coester and Marek Eli. Mixing Predictions for Online Metric Algorithms , booktitle =. 2023 , url =
work page 2023
-
[14]
The Randomized k-Server Conjecture Is False! , booktitle =
S. The Randomized k-Server Conjecture Is False! , booktitle =. 2023 , url =
work page 2023
-
[15]
A Regression Approach to Learning-Augmented Online Algorithms , url =
Anand, Keerti and Ge, Rong and Kumar, Amit and Panigrahi, Debmalya , booktitle =. A Regression Approach to Learning-Augmented Online Algorithms , url =
-
[16]
On the Power of Randomization in On-Line Algorithms , journal =
Shai Ben. On the Power of Randomization in On-Line Algorithms , journal =
- [17]
-
[18]
Competitively Chasing Convex Bodies , journal =
S. Competitively Chasing Convex Bodies , journal =. 2023 , url =
work page 2023
-
[19]
C. J. Argue and Anupam Gupta and Ziye Tang and Guru Guruganesh , title =. J. 2021 , url =
work page 2021
- [20]
-
[21]
Ricardo A. Baeza. Searching in the Plane , journal =. 1993 , url =
work page 1993
-
[22]
Beck, Anatole and Newman, D. J. , doi =. Yet more on the linear search problem , url =. Israel Journal of Mathematics , number =
-
[23]
Proceedings of the 2025 Annual
Xingjian Bai and Christian Coester and Romain Cosson , title =. Proceedings of the 2025 Annual. 2025 , url =
work page 2025
-
[24]
Online 3-Taxi on General Metrics , booktitle =
Christian Coester and Tze. Online 3-Taxi on General Metrics , booktitle =. 2026 , url =
work page 2026
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.