Recognition: unknown
Your Loss is My Gain: Low Stake Attacks on Liquid Staking Pools
Pith reviewed 2026-05-09 17:53 UTC · model grok-4.3
The pith
A low-stake adversary can degrade a liquid staking pool's performance to profit from drops in its token price.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
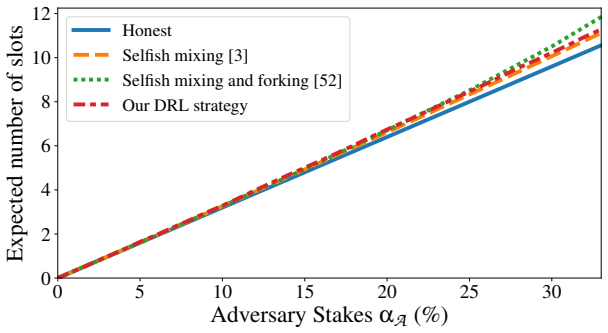
Empirical analysis of Ethereum data shows that liquid staking pool performance is positively associated with later normalized liquid staking token returns. This association supports a cross-layer attack in which a low-stake adversary manipulates the consensus protocol to degrade a chosen pool and then takes positions that profit if the token is repriced accordingly. Deep reinforcement learning identifies strategies that recover near-optimal theoretical attacks and discover additional behaviors that degrade performance; Monte Carlo simulations confirm that leveraged shorting on major pools can be profitable with over one-half probability.
What carries the argument
The cross-layer attack that combines consensus-layer manipulation to degrade pool performance with application-layer financial positions that exploit the observed performance-to-LST-return association.
If this is right
- Standard economic security arguments for Proof-of-Stake do not account for risks introduced by liquid staking.
- Low-stake adversaries can use reinforcement learning to find and execute performance-degrading strategies beyond manually derived theoretical attacks.
- Leveraged shorting of liquid staking tokens can yield positive expected returns when a target pool is degraded.
- New manipulation behaviors that significantly reduce target pool performance can be uncovered automatically.
Where Pith is reading between the lines
- Market pricing of liquid staking tokens may begin to incorporate the risk of targeted degradation attacks.
- Similar performance-return associations could be examined in other Proof-of-Stake networks that support liquid staking.
- Protocol changes that make pool performance harder to manipulate in isolation might reduce the attack surface.
- Empirical tests after public awareness of these strategies could reveal whether the historical association persists.
Load-bearing premise
The positive association between pool performance and subsequent LST returns will continue to shape market prices even when performance is deliberately reduced by an attacker.
What would settle it
Real market data showing that deliberate degradation of a pool's performance fails to produce the expected downward repricing of its liquid staking token.
Figures














read the original abstract
Permissionless Proof-of-Stake (PoS) economic security is predicated on the high cost of violating consensus safety or liveness. We show that liquid staking introduces additional risks that are not captured by standard PoS economic security arguments. Through an empirical study of Ethereum data, we find that the operational performance of liquid staking pools is positively associated with subsequent normalized liquid staking token (LST) returns. Motivated by this, we present a cross-layer attack: a low-stake adversary can manipulate the consensus protocol to degrade a target pool's performance and take application-layer positions that profit if the market reprices the corresponding \gls{LST} in-line with the historically observed association. To make the consensus layer manipulation concrete, we develop a deep reinforcement learning (DRL) framework to automatically discover attack strategies. Our evaluation shows that the learned strategies can recover near-optimal theoretical attacks and uncover new manipulation behaviors that significantly degrade target pool performance. We further characterize feasible application-layer monetization channels and analyze leveraged shorting in detail using Monte Carlo simulations, showing that such attacks can be profitable with over one-half probability for LSTs of major staking pools. Our findings reveal a previously overlooked attack surface in PoS systems with liquid staking and expose a gap between consensus and economic security.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The paper claims that liquid staking in PoS systems creates a cross-layer attack surface: an empirical study of Ethereum data shows a positive association between liquid staking pool operational performance and subsequent normalized LST returns; a low-stake adversary can exploit this by using DRL-discovered consensus manipulations to degrade a target pool's performance and then profit via application-layer positions (e.g., leveraged shorting of the LST) if the market reprices the token in line with the historical association. Monte Carlo simulations indicate such attacks are profitable with probability exceeding one-half for major pools.
Significance. If the central claims hold, the work identifies a novel interaction between consensus-layer manipulation and application-layer pricing in liquid-staking PoS systems, exposing a gap in standard economic-security arguments. The DRL framework for automatically discovering near-optimal and novel attack strategies, together with the explicit Monte Carlo characterization of monetization channels, provides concrete, reproducible tools that strengthen the contribution beyond purely theoretical analysis.
major comments (2)
- [Monte Carlo simulations section] The profitability analysis (Monte Carlo simulations of leveraged shorting) applies the historically observed positive association between pool performance and normalized LST returns directly to attack-induced degradation. No out-of-sample validation, causal identification, or robustness check is reported for whether market participants would reprice LSTs identically when degradation is attributable to an identifiable low-stake consensus attack rather than organic factors.
- [Empirical study section] The empirical study reports an observational correlation from Ethereum data but provides no test of whether the performance-return relationship survives when performance degradation is deliberately engineered by a low-stake adversary (as opposed to natural variation). This assumption is load-bearing for the cross-layer attack claim.
minor comments (2)
- [Empirical study section] Clarify the precise definition of 'normalized LST returns' and the exact performance metrics used in the empirical association (e.g., attestation rate, inclusion delay) to allow independent replication.
- [DRL framework section] The DRL training setup (state space, reward function, and convergence criteria) should be described with sufficient detail for reproducibility, including any hyperparameter sensitivity analysis.
Simulated Author's Rebuttal
We thank the referee for the constructive comments, which correctly highlight the observational character of our empirical analysis and the assumptions in our Monte Carlo simulations. We address each point below and will revise the manuscript to add explicit discussion of these limitations and additional robustness checks.
read point-by-point responses
-
Referee: [Monte Carlo simulations section] The profitability analysis (Monte Carlo simulations of leveraged shorting) applies the historically observed positive association between pool performance and normalized LST returns directly to attack-induced degradation. No out-of-sample validation, causal identification, or robustness check is reported for whether market participants would reprice LSTs identically when degradation is attributable to an identifiable low-stake consensus attack rather than organic factors.
Authors: We agree that the Monte Carlo analysis applies the historical association to attack-induced degradation without direct validation of market repricing under adversarial conditions. This is a genuine limitation, as out-of-sample tests would require observing or inducing identifiable low-stake consensus attacks on the live Ethereum network, which is neither feasible nor ethical. In revision we will add a dedicated limitations paragraph to the Monte Carlo section that states this assumption explicitly, discusses possible differences in market response (e.g., attribution or reputation effects), and reports additional robustness checks on the underlying empirical correlation using alternative specifications and controls for market-wide factors. revision: partial
-
Referee: [Empirical study section] The empirical study reports an observational correlation from Ethereum data but provides no test of whether the performance-return relationship survives when performance degradation is deliberately engineered by a low-stake adversary (as opposed to natural variation). This assumption is load-bearing for the cross-layer attack claim.
Authors: The referee is correct: the empirical study uses observational data on natural performance variation and contains no test of deliberately engineered degradation by a low-stake adversary. Such data do not exist in the Ethereum record, and inducing attacks for identification purposes is impossible within ethical and practical constraints. Our contribution identifies a potential cross-layer risk surface motivated by the observed association rather than asserting causal proof. In revision we will strengthen the language in the empirical study section and introduction to emphasize the correlational nature of the evidence and the modeling assumption required for the attack claim, thereby clarifying the scope of the results. revision: partial
- Direct out-of-sample validation or causal identification of market repricing under low-stake adversarial degradation, because this would require inducing or observing such attacks on the Ethereum mainnet.
Circularity Check
No significant circularity detected
full rationale
The paper's derivation begins with an empirical observational study on Ethereum data establishing a positive association between pool performance and LST returns, then motivates a hypothetical attack that could profit if markets reprice consistently with that association under deliberate degradation. This structure does not reduce any core claim to its inputs by construction: the association is treated as an external historical pattern used to bound potential profits in Monte Carlo simulations, rather than the simulations or attack profitability being a direct renaming or re-application of the fitted values themselves. The DRL framework for discovering consensus manipulations is developed independently as a new contribution. No self-citations, uniqueness theorems, or ansatzes from prior author work are invoked as load-bearing elements in the provided text, and the central claims introduce new attack surfaces and monetization channels without definitional loops or forced statistical equivalence to the input correlation.
Axiom & Free-Parameter Ledger
axioms (1)
- domain assumption Operational performance of liquid staking pools is positively associated with subsequent normalized LST returns and this association will be reflected in market pricing
Reference graph
Works this paper leans on
-
[1]
Accessed: 2026-01-24
Aave.Aave Protocol.https://aave.com/. Accessed: 2026-01-24. 2026
2026
-
[2]
Optuna: A Next-generation Hyperparameter Optimization Framework
Takuya Akiba, Shotaro Sano, Toshihiko Yanase, Takeru Ohta, and Masanori Koyama. “Optuna: A Next-generation Hyperparameter Optimization Framework”. In:Proceed- ings of the 25th ACM SIGKDD International Conference on Knowledge Discovery & Data Mining. KDD ’19. Anchorage, AK, USA: Association for Computing Machinery, 2019, pp. 2623–2631.isbn: 9781450362016.d...
-
[3]
OptimalRANDAOManipulationinEthereum
KayaAlpturerandS.MatthewWeinberg.“OptimalRANDAOManipulationinEthereum”. en. In:6th Conference on Advances in Financial Technologies (AFT 2024). Dagstuhl, Germany: Schloss Dagstuhl – Leibniz-Zentrum für Informatik, 2024, 10:1–10:21.doi: 10 . 4230 / LIPIcs . AFT . 2024 . 10.url:https : / / drops . dagstuhl . de / entities / document/10.4230/LIPIcs.AFT.2024.10
-
[4]
Heteroskedasticity and autocorrelation consistent covariance matrix estimation
Donald WK Andrews. “Heteroskedasticity and autocorrelation consistent covariance matrix estimation”. In:Econometrica: Journal of the Econometric Society(1991), pp. 817–858. 25
1991
-
[5]
In: 44th IEEE Symposium on Security and Privacy, SP 2023, San Francisco, CA, USA, May 21-25, 2023
Roi Bar-Zur, Ameer Abu-Hanna, Ittay Eyal, and Aviv Tamar. “ WeRLman: To Tackle Whale (Transactions), Go Deep (RL) ”. In:2023 IEEE Symposium on Security and Privacy (SP). Los Alamitos, CA, USA: IEEE Computer Society, 2023, pp. 93–110. doi:10.1109/SP46215.2023.10179444.url:https://doi.ieeecomputersociety. org/10.1109/SP46215.2023.10179444
work page doi:10.1109/sp46215.2023.10179444.url:https://doi.ieeecomputersociety 2023
-
[6]
Deep Bribe: Predicting the Rise of Bribery in Blockchain Mining with Deep RL
Roi Bar-Zur, Danielle Dori, Sharon Vardi, Ittay Eyal, and Aviv Tamar. “Deep Bribe: Predicting the Rise of Bribery in Blockchain Mining with Deep RL”. In:2023 IEEE Security and Privacy Workshops (SPW). 2023, pp. 29–37.doi:10.1109/SPW59333. 2023.00008.url:https://ieeexplore.ieee.org/abstract/document/10188634
-
[7]
MAD-DAG: Protecting Blockchain Con- sensus from MEV
Roi Bar-Zur, Aviv Tamar, and Ittay Eyal. “MAD-DAG: Protecting Blockchain Con- sensus from MEV”. In:arXiv preprint arXiv:2511.21552(2025)
-
[8]
Binance.Ethereum Staking on Binance.https : / / www . binance . com / en / earn / ethereum-staking. Accessed: 2026-02-03. Binance, 2026
2026
-
[9]
Verifiable Delay Func- tions
Dan Boneh, Joseph Bonneau, Benedikt Bünz, and Ben Fisch. “Verifiable Delay Func- tions”. In:Annual International Cryptology Conference. Springer. 2018, pp. 757–788
2018
-
[10]
org/web/20160521011553/https://vitalik.ca/files/randomness.html
Vitalik Buterin.Validator Ordering and Randomness in PoS.https://web.archive. org/web/20160521011553/https://vitalik.ca/files/randomness.html. 2016
-
[11]
ch/t/randao-beacon-exploitability-analysis-round-2/1980
VitalikButerin.RANDAO beacon exploitability analysis, round 2.https://ethresear. ch/t/randao-beacon-exploitability-analysis-round-2/1980. 2018
1980
- [12]
- [13]
-
[14]
Vitalik Buterin, Diego Hernandez, Thor Kamphefner, Khiem Pham, Zhi Qiao, Danny Ryan, Juhyeok Sin, Ying Wang, and Yan X Zhang. “Combining ghost and casper”. In: arXiv preprint arXiv:2003.03052(2020)
-
[15]
Profitable Manip- ulations of Cryptographic Self-Selection Are Statistically Detectable
Linda Cai, Jingyi Liu, S. Matthew Weinberg, and Chenghan Zhou. “Profitable Manip- ulations of Cryptographic Self-Selection Are Statistically Detectable”. In:6th Confer- ence on Advances in Financial Technologies (AFT 2024). Ed. by Rainer Böhme and Lucianna Kiffer. Vol. 316. Leibniz International Proceedings in Informatics (LIPIcs). Dagstuhl, Germany: Schl...
-
[16]
Confidence in Assurance 2.0 Cases
Tong Cao, Jérémie Decouchant, and Jiangshan Yu. “Leveraging the verifier’s dilemma to double spend in Bitcoin”. In:Financial Cryptography and Data Security: 27th In- ternational Conference, FC 2023, Bol, Brač, Croatia, May 1–5, 2023, Revised Selected Papers, Part II. Bol, Brač, Croatia: Springer-Verlag, 2023, pp. 149–165.isbn: 978-3- 031-47750-8.doi:10.10...
-
[17]
Algorand: A secure and efficient distributed ledger
Jing Chen and Silvio Micali. “Algorand: A secure and efficient distributed ledger”. In:Theoretical Computer Science. In memory of Maurice Nivat, a founding father of Theoretical Computer Science - Part I 777 (2019), pp. 155–183.issn: 0304-3975.doi: 10.1016/j.tcs.2019.02.001.url:https://www.sciencedirect.com/science/ article/pii/S030439751930091X
work page doi:10.1016/j.tcs.2019.02.001.url:https://www.sciencedirect.com/science/ 2019
-
[18]
In: 44th IEEE Symposium on Security and Privacy, SP 2023, San Francisco, CA, USA, May 21-25, 2023
Kevin Choi, Aathira Manoj, and Joseph Bonneau. “ SoK: Distributed Randomness Beacons ”. In:2023 IEEE Symposium on Security and Privacy (SP). Los Alamitos, CA, USA: IEEE Computer Society, 2023, pp. 75–92.doi:10.1109/SP46215.2023. 10179419.url:https://doi.ieeecomputersociety.org/10.1109/SP46215.2023. 10179419
-
[19]
com/ddos/
Cloudflare, Inc.DDoS Protection & Mitigation Solutions.https://www.cloudflare. com/ddos/. Accessed: 2026-02-04. 2026
2026
-
[20]
routledge, 2013
Jacob Cohen.Statistical power analysis for the behavioral sciences. routledge, 2013
2013
-
[21]
coingecko
CoinGecko.CoinGecko Crypto Data API.https : / / www . coingecko . com / en / api. Accessed: 2025-12-11. 2025
2025
-
[22]
Snow White: Robustly Reconfigurable Con- sensus and Applications to Provably Secure Proof of Stake
Phil Daian, Rafael Pass, and Elaine Shi. “Snow White: Robustly Reconfigurable Con- sensus and Applications to Provably Secure Proof of Stake”. In:Financial Cryptography and Data Security. Ed. by Ian Goldberg and Tyler Moore. Cham: Springer Interna- tional Publishing, 2019, pp. 23–41.isbn: 978-3-030-32101-7
2019
-
[23]
Philip Daian, Steven Goldfeder, Tyler Kell, Yunqi Li, Xueyuan Zhao, Iddo Bentov, Lorenz Breidenbach, and Ari Juels. “Flash Boys 2.0: Frontrunning in Decentralized Exchanges, Miner Extractable Value, and Consensus Instability”. In:2020 IEEE Sym- posium on Security and Privacy (SP). San Francisco, CA, USA: IEEE, 2020, pp. 910– 927.doi:10.1109/SP40000.2020.00040
-
[24]
In2025 IEEE Symposium on Security and Privacy (SP)
Wanning Ding, Yuzhe Tang, and Yibo Wang. “Asymmetric Mempool DoS Security: Formal Definitions and Provable Secure Designs”. English. In:2025 IEEE Symposium on Security and Privacy (SP). IEEE Computer Society, 2025, pp. 1584–1602.isbn: 9798331522360.doi:10.1109/SP61157.2025.00061.url:https://www.computer. org/csdl/proceedings-article/sp/2025/223600a061/21B7R6HnWWk
work page doi:10.1109/sp61157.2025.00061.url:https://www.computer 2025
-
[25]
Paul Dworzanski.A note on committee random number generation, commit-reveal, and last-revealer attacks. 2018.url:https://web.archive.org/web/20210224073927/ http://paul.oemm.org/commit_reveal_subcommittees.pdf
-
[26]
Accessed: 2026-01-24
dYdX.dYdX Protocol.https://www.dydx.xyz/. Accessed: 2026-01-24. 2026. 27
2026
-
[27]
2023.url:https://web
Ben Edgington.Upgrading Ethereum | 2.9.2 Randomness. 2023.url:https://web. archive . org / web / 20240204094612 / https : / / eth2book . info / capella / part2 / building_blocks/randomness/
2023
- [28]
-
[29]
org / developers / docs / consensus - mechanisms / pos / attack - and - defense
EthereumFoundation.Ethereum Proof-of-Stake Attack and Defense.https://ethereum. org / developers / docs / consensus - mechanisms / pos / attack - and - defense. Ac- cessed: 2026-01-27. 2025
2026
-
[30]
Accessed: 2026-04-22
Ethereum Foundation.Beacon-API.https://ethereum.github.io/beacon-APIs/. Accessed: 2026-04-22. 2026
2026
-
[31]
Accessed January 30, 2026
Etherscan.Ethereum Gas Tracker.https://etherscan.io/gastracker. Accessed January 30, 2026. 2026
2026
-
[32]
Majority is not enough: Bitcoin mining is vulnerable
Ittay Eyal and Emin Gün Sirer. “Majority is not enough: Bitcoin mining is vulnerable”. In:International conference on financial cryptography and data security. Vol. 61. Asso- ciation for Computing Machinery (ACM), 2014, pp. 436–454.doi:10.1145/3212998
-
[33]
Optimal Strategic Mining Against Cryptographic Self-Selection in Proof-of-Stake
Matheus V.X. Ferreira, Ye Lin Sally Hahn, S. Matthew Weinberg, and Catherine Yu. “Optimal Strategic Mining Against Cryptographic Self-Selection in Proof-of-Stake”. In:Proceedings of the 23rd ACM Conference on Economics and Computation. EC ’22. Boulder, CO, USA: Association for Computing Machinery, 2022, pp. 89–114.isbn: 9781450391504.doi:10.1145/3490486.3538337
-
[34]
flashbots
Flashbots.MEV-Boost in a Nutshell.https : / / boost . flashbots . net/. Accessed: 2026-04-22. 2026
2026
-
[35]
Accessed: 2026-04-22
Flashbots.MEV-Boost Relay API.https://flashbots.github.io/relay-specs/. Accessed: 2026-04-22. 2026
2026
-
[36]
Bryan Ford and Rainer Böhme.Rationality is Self-Defeating in Permissionless Sys- tems. Oct. 2019.doi:10.48550/arXiv.1910.08820.url:http://arxiv.org/abs/ 1910.08820
work page doi:10.48550/arxiv.1910.08820.url:http://arxiv.org/abs/ 2019
-
[37]
Accessed: 2026-01-24
Gearbox.Gearbox Protocol.https://gearbox.finance/. Accessed: 2026-01-24. 2026
2026
-
[38]
2022.doi:10.48550/arXiv.2203.05838
HansGersbach,AkakiMamageishvili,andManvirSchneider.Staking Pools on Blockchains. 2022.doi:10.48550/arXiv.2203.05838. arXiv:2203.05838 [cs.GT].url:https: //arxiv.org/abs/2203.05838
-
[39]
ArthurGervais,GhassanO.Karame,KarlWüst,VasileiosGlykantzis,HubertRitzdorf, and Srdjan Capkun. “On the Security and Performance of Proof of Work Blockchains”. In:Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communica- tions Security. CCS ’16. Vienna, Austria: Association for Computing Machinery, 2016, pp. 3–16.isbn: 9781450341394.doi:10.11...
-
[40]
Eclipse Attacks on Bitcoin’s Peer-to-Peer Network
Ethan Heilman, Alison Kendler, Aviv Zohar, and Sharon Goldberg. “Eclipse Attacks on Bitcoin’s Peer-to-Peer Network”. In:24th USENIX Security Symposium (USENIX Security 15). Washington, D.C.: USENIX Association, Aug. 2015, pp. 129–144.isbn: 978-1-939133-11-3.url:https://www.usenix.org/conference/usenixsecurity15/ technical-sessions/presentation/heilman. 28
2015
-
[41]
Exploring the orthogonality and linearity of backdoor attacks,
Lioba Heimbach, Vabuk Pahari, and Eric Schertenleib. “Non-Atomic Arbitrage in De- centralized Finance”. In:2024 IEEE Symposium on Security and Privacy (SP). IEEE. 2024, pp. 3866–3884.doi:10.1109/SP54263.2024.00256
-
[42]
2024.doi:10.48550/arXiv.2409.04366
Lioba Heimbach, Yann Vonlanthen, Juan Villacis, Lucianna Kiffer, and Roger Watten- hofer.Deanonymizing Ethereum Validators: The P2P Network Has a Privacy Issue. 2024.doi:10.48550/arXiv.2409.04366. arXiv:2409.04366 [cs.CR].url:https: //arxiv.org/abs/2409.04366
-
[43]
Accessed: 2026-01-27
hildobby.Ethereum Staking Overview.https://dune.com/hildobby/eth2-staking. Accessed: 2026-01-27. 2026
2026
-
[44]
SquirRL: Automating Attack Analysis on Blockchain Incentive Mechanisms with Deep Reinforcement Learning
Charlie Hou, Mingxun Zhou, Yan Ji, Phil Daian, Florian Tramer, Giulia Fanti, and Ari Juels. “SquirRL: Automating Attack Analysis on Blockchain Incentive Mechanisms with Deep Reinforcement Learning”. In:28th Annual Network and Distributed System Security Symposium, NDSS 2021, virtually, February 21-25, 2021. Reston, VA: The Internet Society, 2021.doi:10 . ...
2021
-
[45]
A closer look at invalid action masking in policy gradient algorithms
Shengyi Huang and Santiago Ontañón. “A closer look at invalid action masking in policy gradient algorithms”. In:arXiv preprint arXiv:2006.14171(2020)
-
[46]
Ouroboros: A Provably Secure Proof-of-Stake Blockchain Protocol
AggelosKiayias,AlexanderRussell,BernardoDavid,andRomanOliynykov.“Ouroboros: A Provably Secure Proof-of-Stake Blockchain Protocol”. In:Advances in Cryptology – CRYPTO 2017. Ed. by Jonathan Katz and Hovav Shacham. Cham: Springer Interna- tional Publishing, 2017, pp. 357–388.isbn: 978-3-319-63688-7
2017
-
[47]
Arad Kotzer, Tom Azoulay, Yoad Abels, Aviv Yaish, and Ori Rottenstreich. “SoK: DeFi Lending and Yield Aggregation Protocol Taxonomy, Empirical Measurements, and Security Challenges”. In:IEEE Transactions on Network and Service Management (2026), pp. 1–1.issn: 1932-4537.doi:10.1109/TNSM.2026.3682174
-
[48]
Jois, Matthew Green, and Aviel D
Kai Li, Yibo Wang, and Yuzhe Tang. “DETER: Denial of Ethereum Txpool SERvices”. In:Proceedings of the 2021 ACM SIGSAC Conference on Computer and Communica- tions Security. CCS ’21. Virtual Event, Republic of Korea: Association for Comput- ing Machinery, 2021, pp. 1645–1667.isbn: 9781450384544.doi:10.1145/3460120. 3485369
-
[49]
Bun- nyFinder: Finding Incentive Flaws for Ethereum Consensus
Rujia Li, Mingfei Zhang, Xueqian Lu, Wenbo Xu, Ying Yan, and Sisi Duan. “Bun- nyFinder: Finding Incentive Flaws for Ethereum Consensus”. In:Cryptology ePrint Archive(2025)
2025
-
[50]
William Meng. “Analysis of Factors that Drive Ethereum Staking Deposit and With- drawal Trends across Various Staking Participant Groups”. In:Available at SSRN 4949780(2024).doi:10.2139/ssrn.4949780
-
[51]
Asynchronous methods for deep reinforcement learning
Volodymyr Mnih, Adria Puigdomenech Badia, Mehdi Mirza, Alex Graves, Timothy Lillicrap, Tim Harley, David Silver, and Koray Kavukcuoglu. “Asynchronous methods for deep reinforcement learning”. In:International conference on machine learning. PmLR. 2016, pp. 1928–1937. 29
2016
-
[52]
Forking the RANDAO: Manipulating Ethereum’s Distributed Randomness Beacon
Ábel Nagy, János Tapolcai, István András Seres, and Bence Ladóczki. “Forking the RANDAO: Manipulating Ethereum’s Distributed Randomness Beacon”. In:Proceed- ings of the 2025 ACM SIGSAC Conference on Computer and Communications Secu- rity. CCS ’25. Taipei, Taiwan: Association for Computing Machinery, 2025, pp. 873– 887.isbn: 9798400715259.doi:10.1145/37190...
work page doi:10.1145/3719027.3744852.url:https://doi.org/ 2025
-
[53]
SelfishMiningRe-Examined
KevinAlarcónNegy,PeterR.Rizun,andEminGünSirer.“SelfishMiningRe-Examined”. In:Financial Cryptography and Data Security. Ed. by Joseph Bonneau and Nadia Heninger. Cham: Springer International Publishing, 2020, pp. 61–78.isbn: 978-3-030- 51280-4
2020
-
[54]
One Engine to Fuzz 'em All: Generic Language Processor Testing with Semantic Validation,
Joachim Neu, Ertem Nusret Tas, and David Tse. “Ebb-and-Flow Protocols: A Resolu- tion of the Availability-Finality Dilemma”. In:2021 IEEE Symposium on Security and Privacy (SP). 2021, pp. 446–465.doi:10.1109/SP40001.2021.00045
-
[55]
Two More Attacks on Proof-of-Stake GHOST/Ethereum
Joachim Neu, Ertem Nusret Tas, and David Tse. “Two More Attacks on Proof-of-Stake GHOST/Ethereum”. In:Proceedings of the 2022 ACM Workshop on Developments in Consensus. ConsensusDay ’22. Los Angeles, CA, USA: Association for Computing Machinery, 2022, pp. 43–52.isbn: 9781450398794.doi:10.1145/3560829.3563560. url:https://doi.org/10.1145/3560829.3563560
-
[56]
Low-cost attacks on Ethereum 2.0 by sub-1/3 stakeholders
Michael Neuder, Daniel J Moroz, Rithvik Rao, and David C Parkes. “Low-cost attacks on Ethereum 2.0 by sub-1/3 stakeholders”. In:arXiv preprint arXiv:2102.02247(2021)
-
[57]
Who Wins Ethereum Block Building Auctions and Why?
Burak Öz, Danning Sui, Thomas Thiery, and Florian Matthes. “Who Wins Ethereum Block Building Auctions and Why?” In:6th Conference on Advances in Financial Technologies (AFT 2024). Ed. by Rainer Böhme and Lucianna Kiffer. Vol. 316. Leib- niz International Proceedings in Informatics (LIPIcs). Dagstuhl, Germany: Schloss Dagstuhl – Leibniz-Zentrum für Informa...
work page doi:10.4230/lipics.aft.2024.22.url:https://drops.dagstuhl.de/entities/ 2024
-
[58]
Cross-Chain Arbitrage: The Next Frontier of MEV in Decentralized Finance
Burak Öz, Christof Ferreira Torres, Christoph Schlegel, Bruno Mazorra, Jonas Gebele, Filip Rezabek, and Florian Matthes. “Cross-Chain Arbitrage: The Next Frontier of MEV in Decentralized Finance”. In:Proc. ACM Meas. Anal. Comput. Syst.9.3 (Dec. 2025).doi:10.1145/3771566.url:https://doi.org/10.1145/3771566
work page doi:10.1145/3771566.url:https://doi.org/10.1145/3771566 2025
-
[59]
Ethereum Proof-of-Stake under Scrutiny
Ulysse Pavloff, Yackolley Amoussou-Guenou, and Sara Tucci-Piergiovanni. “Ethereum Proof-of-Stake under Scrutiny”. In:Proceedings of the 38th ACM/SIGAPP Symposium on Applied Computing. SAC ’23. Tallinn, Estonia: Association for Computing Machin- ery, 2023, pp. 212–221.isbn: 9781450395175.doi:10.1145/3555776.3577655.url: https://doi.org/10.1145/3555776.3577655
-
[60]
Polymarket.Polymarket: The World’s Largest Prediction Market.https://polymarket. com/. Accessed: 2026-01-24. 2026
2026
-
[61]
Online HackMD note
Potuz.Justification withholding attacks. Online HackMD note. Accessed: 2026-01-24. 2024.url:https://hackmd.io/o9tGPQL2Q4iH3Mg7Mma9wQ
2026
-
[62]
John Wiley & Sons, 2014
Martin L Puterman.Markov decision processes: discrete stochastic dynamic program- ming. John Wiley & Sons, 2014. 30
2014
-
[63]
TopoShot: uncovering Ethereum's network topology leveraging replacement transactions , booktitle =
Kaihua Qin, Liyi Zhou, Pablo Gamito, Philipp Jovanovic, and Arthur Gervais. “An empirical study of DeFi liquidations: incentives, risks, and instabilities”. In:Proceed- ings of the 21st ACM Internet Measurement Conference. IMC ’21. Virtual Event: As- sociation for Computing Machinery, 2021, pp. 336–350.isbn: 9781450391290.doi: 10.1145/3487552.3487811.url:...
work page doi:10.1145/3487552.3487811.url:https://doi.org/10.1145/3487552.3487811 2021
-
[64]
Attacking the defi ecosystem with flash loans for fun and profit
Kaihua Qin, Liyi Zhou, Benjamin Livshits, and Arthur Gervais. “Attacking the defi ecosystem with flash loans for fun and profit”. In:International conference on financial cryptography and data security. Springer. 2021, pp. 3–32
2021
-
[65]
Stable-Baselines3: Reliable Reinforcement Learning Implemen- tations
Antonin Raffin, Ashley Hill, Adam Gleave, Anssi Kanervisto, Maximilian Ernestus, and Noah Dormann. “Stable-Baselines3: Reliable Reinforcement Learning Implemen- tations”. In:Journal of Machine Learning Research22.268 (2021), pp. 1–8.url:http: //jmlr.org/papers/v22/20-1364.html
2021
-
[66]
arXiv , author =:1905.13457 , journal =
F. Ritz and A. Zugenmaier. “The Impact of Uncle Rewards on Selfish Mining in Ethereum”. In:2018 IEEE European Symposium on Security and Privacy Workshops (EuroS&PW). Los Alamitos, CA, USA: IEEE Computer Society, Apr. 2018, pp. 50–57. doi:10.1109/eurospw.2018.00013
-
[67]
rocketpool.net/legacy/atlas/lebs#rpl-collateral
Rocket Pool.8-ETH Bonded Minipools | RPL Collateral Requirements.https://docs. rocketpool.net/legacy/atlas/lebs#rpl-collateral. Accessed: 2026-02-04. 2023
2026
-
[68]
Rosenfeld.Analysis of Bitcoin Pooled Mining Reward Systems
M. Rosenfeld.Analysis of Bitcoin Pooled Mining Reward Systems. Dec. 2011.doi: 10.48550/arxiv.1112.4980. arXiv:1112.4980 [cs.DC]
-
[69]
Un- ravelling the Probabilistic Forest: Arbitrage in Prediction Markets
Oriol Saguillo, Vahid Ghafouri, Lucianna Kiffer, and Guillermo Suarez-Tangil. “Un- ravelling the Probabilistic Forest: Arbitrage in Prediction Markets”. In:7th Confer- ence on Advances in Financial Technologies (AFT 2025). Ed. by Zeta Avarikioti and Nicolas Christin. Vol. 354. Leibniz International Proceedings in Informatics (LIPIcs). Dagstuhl, Germany: S...
-
[70]
Optimal Selfish Mining Strategies in Bitcoin
Ayelet Sapirshtein, Yonatan Sompolinsky, and Aviv Zohar. “Optimal Selfish Mining Strategies in Bitcoin”. In:Financial Cryptography and Data Security. Ed. by Jens Grossklags and Bart Preneel. Berlin, Heidelberg: Springer, 2017, pp. 515–532.isbn: 978-3-662-54970-4
2017
-
[71]
Bitcoin Under Volatile Block Rewards: How Mempool Statistics Can Influence Bitcoin Min- ing
Roozbeh Sarenche, Alireza Aghabagherloo, Svetla Nikova, and Bart Preneel. “Bitcoin Under Volatile Block Rewards: How Mempool Statistics Can Influence Bitcoin Min- ing”. In: CCS ’25. New York, NY, USA: Association for Computing Machinery, 2025, pp. 903–917.isbn: 9798400715259.doi:10 . 1145 / 3719027 . 3744875.url:https : //doi.org/10.1145/3719027.3744875
-
[72]
Commitment Attacks on Ethereum’s Reward Mechanism
Roozbeh Sarenche, Ertem Nusret Tas, Barnabe Monnot, Caspar Schwarz-Schilling, and Bart Preneel. “ Commitment Attacks on Ethereum’s Reward Mechanism ”. In:2025 IEEE 10th European Symposium on Security and Privacy (EuroS&P). Los Alami- tos, CA, USA: IEEE Computer Society, July 2025, pp. 504–526.doi:10 . 1109 / EuroSP63326 . 2025 . 00036.url:https : / / doi ...
-
[73]
The Economics of Liquid Staking Derivatives: Basis Determinants and Price Discovery
Stefan Scharnowski and Hossein Jahanshahloo. “The Economics of Liquid Staking Derivatives: Basis Determinants and Price Discovery”. In:Journal of Futures Markets 45.2 (2025), pp. 91–117.doi:https://doi.org/10.1002/fut.22556.url:https: //onlinelibrary.wiley.com/doi/abs/10.1002/fut.22556
-
[74]
Proximal Policy Optimization Algorithms
John Schulman, Filip Wolski, Prafulla Dhariwal, Alec Radford, and Oleg Klimov. “Proximalpolicyoptimizationalgorithms”.In:arXiv preprint arXiv:1707.06347(2017)
work page internal anchor Pith review Pith/arXiv arXiv 2017
-
[75]
Three Attacks on Proof-of-Stake Ethereum
Caspar Schwarz-Schilling, Joachim Neu, Barnabé Monnot, Aditya Asgaonkar, Ertem Nusret Tas, and David Tse. “Three Attacks on Proof-of-Stake Ethereum”. In:Financial Cryptography and Data Security: 26th International Conference, FC 2022, Grenada, May 2–6, 2022, Revised Selected Papers. Grenada, Grenada: Springer-Verlag, 2022, pp. 560–576.isbn: 978-3-031-1828...
-
[76]
Gymnasium: A Standard Interface for Reinforcement Learning Environments
Mark Towers, Ariel Kwiatkowski, Jordan Terry, John U Balis, Gianluca De Cola, Tristan Deleu, Manuel Goulão, Andreas Kallinteris, Markus Krimmel, Arjun KG, et al. “Gymnasium: A Standard Interface for Reinforcement Learning Environments”. In: arXiv preprint arXiv:2407.17032(2024)
work page internal anchor Pith review arXiv 2024
-
[77]
The Principal–Agent Problem in Liquid Stak- ing
Apostolos Tzinas and Dionysis Zindros. “The Principal–Agent Problem in Liquid Stak- ing”. en. In:Financial Cryptography and Data Security. FC 2023 International Work- shops. Ed. by Aleksander Essex, Shin’ichiro Matsuo, Oksana Kulyk, Lewis Gudgeon, Ariah Klages-Mundt, Daniel Perez, Sam Werner, Andrea Bracciali, and Geoff Goodell. Cham: Springer Nature Swit...
-
[78]
Accessed: 2026-04-23
Uniswap Labs.API Integration Guide.https://api- docs.uniswap.org/guides/ integration_guide. Accessed: 2026-04-23. 2026
2026
-
[79]
When Blockchain Meets AI: Optimal Mining Strategy Achieved by Machine Learning
Taotao Wang, Soung Chang Liew, and Shengli Zhang. “When Blockchain Meets AI: Optimal Mining Strategy Achieved by Machine Learning”. In:International Journal of Intelligent Systems36.5 (2021), pp. 2183–2207.issn: 1098-111X.doi:10.1002/int. 22375
work page doi:10.1002/int 2021
-
[80]
Cyclic Arbitrage in Decentralized Exchanges
Ye Wang, Yan Chen, Haotian Wu, Liyi Zhou, Shuiguang Deng, and Roger Wattenhofer. “Cyclic Arbitrage in Decentralized Exchanges”. In:Companion Proceedings of the Web Conference 2022. WWW ’22. Virtual Event, Lyon, France: Association for Computing Machinery, 2022, pp. 12–19.isbn: 9781450391306.doi:10.1145/3487553.3524201. url:https://doi.org/10.1145/3487553.3524201
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.