Recognition: unknown
Toward Resilient 5G Networks: Comparative Analysis of Federated and Centralized Learning for RF Jamming Detection
Pith reviewed 2026-05-09 17:00 UTC · model grok-4.3
The pith
Federated learning on local IQ samples detects RF jamming in 5G networks at 97 percent accuracy while preserving user equipment privacy.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
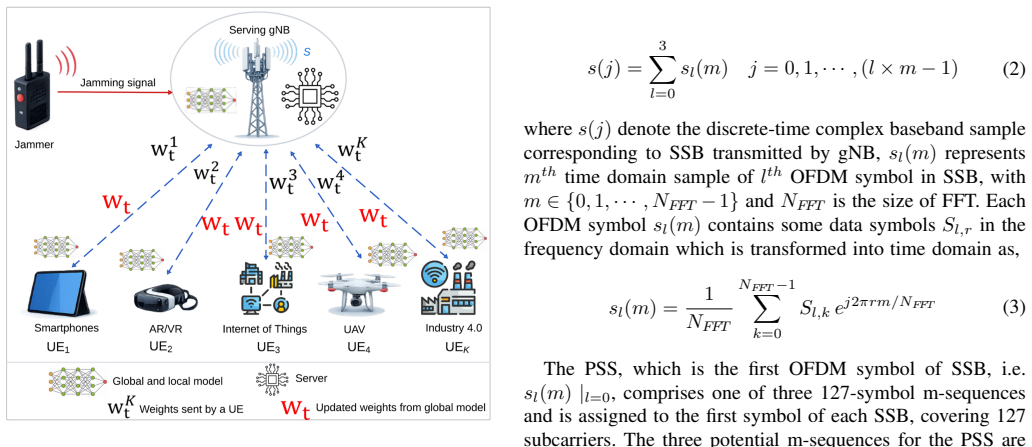
The paper claims that a federated learning system using Federated Averaging to train a 1D convolutional neural network on over-the-air IQ samples extracted from Synchronization Signal Blocks achieves 97 percent accuracy and 97 percent F1-score for RF jamming detection. This performance surpasses centralized models including multilayer perceptron, 1D CNN, support vector machine, and logistic regression while ensuring that raw signal data never leaves the participating user equipment.
What carries the argument
Federated Averaging algorithm applied to a 1D convolutional neural network that learns from distributed IQ samples taken from Synchronization Signal Blocks, aggregating only model parameters instead of raw data.
If this is right
- Jamming detection can be deployed across many user devices without creating a central database of raw RF signals.
- The federated model matches or exceeds the detection rates of models trained on pooled centralized data.
- The framework uses existing Synchronization Signal Blocks, so it requires no new signaling overhead for sample collection.
- Privacy is maintained because only model updates are shared, reducing exposure of user equipment data.
Where Pith is reading between the lines
- In a real network the smaller size of model updates compared with raw IQ samples could reduce uplink traffic during training.
- The same local-sample approach could be retrained on labeled data for other RF anomalies such as spoofing or interference without redesigning the collection pipeline.
- Non-identical data distributions across user equipment might slow convergence and would need testing in heterogeneous deployments.
Load-bearing premise
The collected or simulated over-the-air IQ samples from Synchronization Signal Blocks are representative of real jamming attacks and that the federated averaging process adds acceptable communication and convergence overhead in an actual 5G network.
What would settle it
Evaluating the trained federated model on fresh over-the-air IQ samples captured from a live 5G base station during a controlled jamming attack and observing whether accuracy remains above 90 percent.
Figures



read the original abstract
Jamming attacks are proliferating and pose a significant threat to the security of 5G and beyond networks. These attacks target 5G radio frequency (RF) domain and can disrupt the communication in wireless networks. While conventional machine learning and deep learning approaches demonstrate its potential for jamming detection, they typically require centralized data collection, compromising the privacy of user equipment (UEs). This work proposes a federated learning (FL)-based jamming detection framework that operates on over-the-air In-phase and Quadrature (IQ) samples extracted from Synchronization Signal Blocks (SSBs) in the RF domain. The framework enables collaborative model training across multiple UEs without sharing raw RF signal data. We adopt Federated Averaging (FedAvg) algorithm to train a 1D convolutional neural network (1DCNN) for effective detection of attacks. Numerical results demonstrate that the proposed FL framework achieves 97% accuracy and 97% F1-score, outperforming centralized baselines including MLP, 1DCNN, SVM, and logistic regression, while preserving the data privacy of all participating UEs
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The manuscript proposes a federated learning (FL) framework for RF jamming detection in 5G networks. It extracts over-the-air In-phase/Quadrature (IQ) samples from Synchronization Signal Blocks (SSBs) and applies the Federated Averaging (FedAvg) algorithm to train a 1D convolutional neural network (1DCNN) collaboratively across user equipments (UEs) without sharing raw data. The central empirical claim is that the FL 1DCNN achieves 97% accuracy and 97% F1-score, outperforming centralized baselines (MLP, 1DCNN, SVM, logistic regression) while preserving UE data privacy.
Significance. If the performance comparison is shown to be robust, the work would provide concrete evidence that privacy-preserving FL can match or exceed centralized detection for RF-domain threats in 5G, a practically relevant result for secure wireless systems. The choice of SSB IQ samples as features is a strength, as it ties the method directly to standard 5G signaling.
major comments (2)
- Numerical Results section: the headline claim that the proposed FL 1DCNN reaches 97% accuracy/F1 and outperforms the centralized 1DCNN baseline is load-bearing for the paper's contribution. The manuscript must explicitly state the total number of IQ samples used for the centralized 1DCNN, the number of epochs, optimizer settings, and learning-rate schedule, and confirm that these match the aggregate across all FL clients. If the centralized model was trained on a smaller subset or with mismatched hyperparameters, the reported outperformance is an artifact rather than evidence that FL is superior.
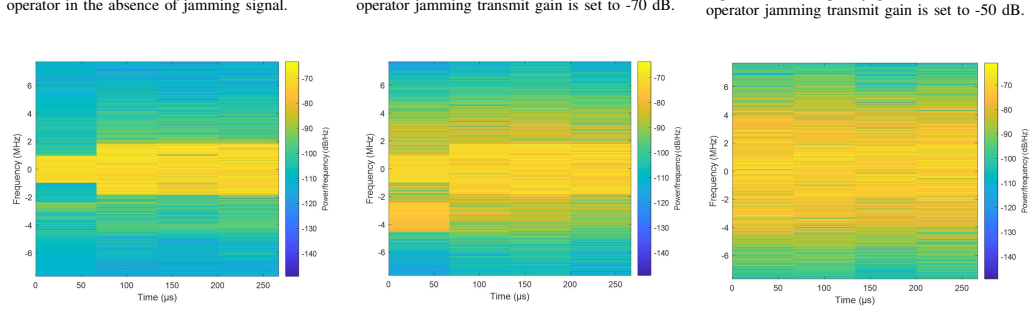
- Experimental Setup section: no information is provided on dataset size, train-test split ratios, jamming signal models (e.g., power, bandwidth, duty cycle), or statistical significance testing (e.g., multiple random seeds, confidence intervals). Without these details the 97% figures cannot be reproduced or compared to prior work on RF jamming detection.
minor comments (2)
- Abstract and Section 4: the phrase 'outperforming centralized baselines including MLP, 1DCNN, SVM, and logistic regression' should be accompanied by a table that reports all four metrics (accuracy, precision, recall, F1) for every method under identical conditions.
- Figure captions and Section 3: clarify whether the 1DCNN architecture (number of layers, kernel sizes, pooling) is identical between the FL and centralized versions; any difference must be justified.
Simulated Author's Rebuttal
We thank the referee for their constructive feedback on our manuscript. The comments have prompted us to enhance the transparency of our experimental methodology and ensure the robustness of our comparative analysis. We address each major comment below and have made corresponding revisions to the paper.
read point-by-point responses
-
Referee: Numerical Results section: the headline claim that the proposed FL 1DCNN reaches 97% accuracy/F1 and outperforms the centralized 1DCNN baseline is load-bearing for the paper's contribution. The manuscript must explicitly state the total number of IQ samples used for the centralized 1DCNN, the number of epochs, optimizer settings, and learning-rate schedule, and confirm that these match the aggregate across all FL clients. If the centralized model was trained on a smaller subset or with mismatched hyperparameters, the reported outperformance is an artifact rather than evidence that FL is superior.
Authors: We fully agree that the comparison between FL and centralized learning must be conducted under identical conditions to be meaningful. Our centralized 1DCNN baseline was indeed trained on the complete aggregated dataset comprising all IQ samples from the participating UEs, using the same total sample count as the union of all FL clients' data. The training hyperparameters, including the number of epochs, optimizer, and learning rate schedule, were set identically to those used in the federated setting. In the revised version of the manuscript, we will add explicit statements and possibly a dedicated paragraph in the Numerical Results section to document these details and confirm the matching conditions. This will substantiate that the observed performance advantage is not due to any discrepancy in training setup. revision: yes
-
Referee: Experimental Setup section: no information is provided on dataset size, train-test split ratios, jamming signal models (e.g., power, bandwidth, duty cycle), or statistical significance testing (e.g., multiple random seeds, confidence intervals). Without these details the 97% figures cannot be reproduced or compared to prior work on RF jamming detection.
Authors: We acknowledge the need for more comprehensive information in the Experimental Setup section to facilitate reproducibility. In the revised manuscript, we will include the total dataset size, the specific train-test split ratios employed, detailed descriptions of the jamming signal models (such as their power levels, bandwidth, and duty cycles), and the procedures for statistical significance testing, including the use of multiple random seeds and the reporting of confidence intervals. These additions will allow readers to reproduce our 97% accuracy and F1-score results and compare them effectively with prior work. revision: yes
Circularity Check
No circularity: empirical performance comparison is self-contained
full rationale
The paper presents an applied empirical study: it trains a 1DCNN via FedAvg on over-the-air IQ samples from SSBs, reports 97% accuracy/F1, and compares against centralized baselines (MLP, 1DCNN, SVM, logistic regression). No mathematical derivation, uniqueness theorem, or prediction is claimed that reduces by construction to fitted parameters, self-citations, or ansatz. The central claim is a direct experimental outcome on collected/simulated data; any concerns about training parity or data representativeness are validity issues, not circularity. The work contains no load-bearing self-referential steps.
Axiom & Free-Parameter Ledger
axioms (1)
- domain assumption Federated averaging converges to a useful global model when local datasets are drawn from similar distributions.
Reference graph
Works this paper leans on
-
[1]
Scalable cell-free massive mimo systems,
E. Bj ¨ornson and L. Sanguinetti, “Scalable cell-free massive mimo systems,”IEEE Transactions on Communications, vol. 68, no. 7, pp. 4247–4261, 2020
2020
-
[2]
A miniaturized microstrip antenna array at 5g millimeter-wave band,
X. Shen, Y . Liu, L. Zhao, G.-L. Huang, X. Shi, and Q. Huang, “A miniaturized microstrip antenna array at 5g millimeter-wave band,”IEEE Antennas and Wireless Propagation Letters, vol. 18, no. 8, pp. 1671– 1675, 2019
2019
-
[3]
Lte-advanced carrier aggregation for enhance- ment of bandwidth,
A. Goyal and K. Kumar, “Lte-advanced carrier aggregation for enhance- ment of bandwidth,” inAdvances in VLSI, Communication, and Signal Processing: Select Proceedings of VCAS 2018. Springer, 2019, pp. 341–351
2018
-
[4]
A compre- hensive survey on software-defined networking for smart communities,
R. Chaudhary, G. S. Aujla, N. Kumar, and P. K. Chouhan, “A compre- hensive survey on software-defined networking for smart communities,” Inl. J. of Communication Systems, vol. 38, no. 1, p. e5296, 2025
2025
-
[5]
A practical downlink noma scheme for wireless lans,
P. K. Sangdeh, H. Pirayesh, Q. Yan, K. Zeng, W. Lou, and H. Zeng, “A practical downlink noma scheme for wireless lans,”IEEE transactions on communications, vol. 68, no. 4, pp. 2236–2250, 2020
2020
-
[6]
A tutorial on beam management for 3gpp nr at mmwave frequencies,
M. Giordani, M. Polese, A. Roy, D. Castor, and M. Zorzi, “A tutorial on beam management for 3gpp nr at mmwave frequencies,”IEEE Communications Surveys & Tutorials, vol. 21, no. 1, pp. 173–196, 2018
2018
-
[7]
Jamming attacks and anti-jamming strategies in wireless networks: A comprehensive survey,
H. Pirayesh and H. Zeng, “Jamming attacks and anti-jamming strategies in wireless networks: A comprehensive survey,”IEEE communications surveys & tutorials, vol. 24, no. 2, pp. 767–809, 2022
2022
-
[8]
Federated learning- based jamming detection for distributed tactical wireless networks,
A. Meftah, G. Kaddoum, T. N. Do, and C. Talhi, “Federated learning- based jamming detection for distributed tactical wireless networks,” inMILCOM 2022-2022 IEEE Military Communications Conference (MILCOM). IEEE, 2022, pp. 629–634
2022
-
[9]
K. Tekbıyık, ¨O. Akbunar, A. R. Ekti, A. G ¨orc ¸in, and G. K. Kurt, “Real-world considerations for deep learning in wireless signal identification based on spectral correlation function,”arXiv preprint arXiv:2003.08359, 2020
-
[10]
End-to-end learning from spectrum data: A deep learning approach for wireless signal identification in spectrum monitoring applications,
M. Kulin, T. Kazaz, I. Moerman, and E. De Poorter, “End-to-end learning from spectrum data: A deep learning approach for wireless signal identification in spectrum monitoring applications,”IEEE access, vol. 6, pp. 18 484–18 501, 2018
2018
-
[11]
Federated learning for 5g and beyond, a blessing and a curse- an experimental study on intrusion detection systems,
T. E. T. Djaidja, B. Brik, A. Boualouache, S. M. Senouci, and Y . Ghamri- Doudane, “Federated learning for 5g and beyond, a blessing and a curse- an experimental study on intrusion detection systems,”Computers & Security, vol. 139, p. 103707, 2024
2024
-
[12]
A privacy-preserving collaborative jamming attacks detection framework using federated learning,
Z. Abou El Houda, D. Naboulsi, and G. Kaddoum, “A privacy-preserving collaborative jamming attacks detection framework using federated learning,”IEEE Internet of Things Journal, vol. 11, no. 7, pp. 12 153– 12 164, 2023
2023
-
[13]
Federated learning-enabled jamming detection and waveform classification for distributed tactical wireless networks,
A. Meftah, T. N. Do, G. Kaddoum, C. Talhi, and S. Singh, “Federated learning-enabled jamming detection and waveform classification for distributed tactical wireless networks,”IEEE Transactions on Network and Service Management, vol. 20, no. 4, pp. 5053–5072, 2023
2023
-
[14]
Evaluation of na ¨ıve bayesian algorithms for cyber-attacks detection in wireless sensor networks,
S. Ismail and H. Reza, “Evaluation of na ¨ıve bayesian algorithms for cyber-attacks detection in wireless sensor networks,” in2022 IEEE world AI IoT congress (AIIoT). IEEE, 2022, pp. 283–289
2022
-
[15]
Multi-stage jamming attacks detection using deep learning combined with kernelized support vector machine in 5g cloud radio access networks,
M. Hachimi, G. Kaddoum, G. Gagnon, and P. Illy, “Multi-stage jamming attacks detection using deep learning combined with kernelized support vector machine in 5g cloud radio access networks,” inIntl. Symp. on networks, computers and communications. IEEE, 2020, pp. 1–5
2020
-
[16]
Federated-learning-based anomaly detection for iot security attacks,
V . Mothukuri, P. Khare, R. M. Parizi, S. Pouriyeh, A. Dehghantanha, and G. Srivastava, “Federated-learning-based anomaly detection for iot security attacks,”IEEE Internet of Things Journal, vol. 9, no. 4, pp. 2545–2554, 2021
2021
-
[17]
Intrusion detection for wireless edge networks based on federated learning,
Z. Chen, N. Lv, P. Liu, Y . Fang, K. Chen, and W. Pan, “Intrusion detection for wireless edge networks based on federated learning,”IEEE Access, vol. 8, pp. 217 463–217 472, 2020
2020
-
[18]
Federated learning for internet of things,
T. Zhang, C. He, T. Ma, L. Gao, M. Ma, and S. Avestimehr, “Federated learning for internet of things,” inProceedings of the 19th ACM conference on embedded networked sensor systems, 2021, pp. 413–419
2021
-
[19]
Decoding 5g security: toward a hybrid threat ontology,
R. A. Paskauskas, “Decoding 5g security: toward a hybrid threat ontology,”Open Research Europe, vol. 4, p. 34, 2025
2025
-
[20]
Survey on 5g physical layer security threats and countermeasures,
M. Harvanek, J. Bolcek, J. Kufa, L. Polak, M. Simka, and R. Marsalek, “Survey on 5g physical layer security threats and countermeasures,” Sensors, vol. 24, no. 17, p. 5523, 2024
2024
-
[21]
A formal analysis of 5g eap-tls protocol,
M. Shi, J. Chen, Z. Ma, K. He, M. Jia, and R. Du, “A formal analysis of 5g eap-tls protocol,”IEEE Transactions on Networking, 2025
2025
-
[22]
Toward an era of secure 5g convergence applications: Formal security verification of 3gpp akma with tls 1.3 psk option,
Y . Ko, I. W. A. J. Pawana, T. Won, P. V . Astillo, and I. You, “Toward an era of secure 5g convergence applications: Formal security verification of 3gpp akma with tls 1.3 psk option,”Applied Sciences, vol. 14, no. 23, p. 11152, 2024
2024
-
[23]
Synchronization procedure in 5G NR systems,
A. Omri, M. Shaqfeh, A. Ali, and H. Alnuweiri, “Synchronization procedure in 5G NR systems,”IEEE Access, vol. 7, pp. 41 286–41 295, 2019
2019
-
[24]
5G; NR; Physical channels and modulation,
3GPP, “5G; NR; Physical channels and modulation,” 3rd Generation Partnership Project (3GPP), Technical Specification (TS) 38.211, 10 2023, version 17.6.0. [Online]. Available: https://portal.3gpp.org/desktopmodules/Specifications/SpecificationDet- ails.aspx?specificationId=3213
2023
-
[25]
Communication-efficient learning of deep networks from decentralized data,
B. McMahan, E. Moore, D. Ramage, S. Hampson, and B. A. y Arcas, “Communication-efficient learning of deep networks from decentralized data,” inArtificial intelligence and statistics. Pmlr, 2017, pp. 1273– 1282
2017
-
[26]
Wsn-ds: a dataset for intrusion detection systems in wireless sensor networks,
I. Almomani, B. Al-Kasasbeh, and M. Al-Akhras, “Wsn-ds: a dataset for intrusion detection systems in wireless sensor networks,”Journal of Sensors, vol. 2016, no. 1, p. 4731953, 2016
2016
-
[27]
Deep learning and recognition of radar jamming based on cnn,
Q. Liu and W. Zhang, “Deep learning and recognition of radar jamming based on cnn,” in2019 12th international symposium on computational intelligence and design (ISCID), vol. 1. IEEE, 2019, pp. 208–212
2019
-
[28]
Iot-based smart farming architecture using federated learning: a nitrous oxide emission prediction use case,
P. Killeen, C. Lin, F. Li, I. Kiringa, and T. Yeap, “Iot-based smart farming architecture using federated learning: a nitrous oxide emission prediction use case,”ACM Journal on Computing and Sustainable Societies, vol. 3, no. 2, pp. 1–38, 2025
2025
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.