Recognition: unknown
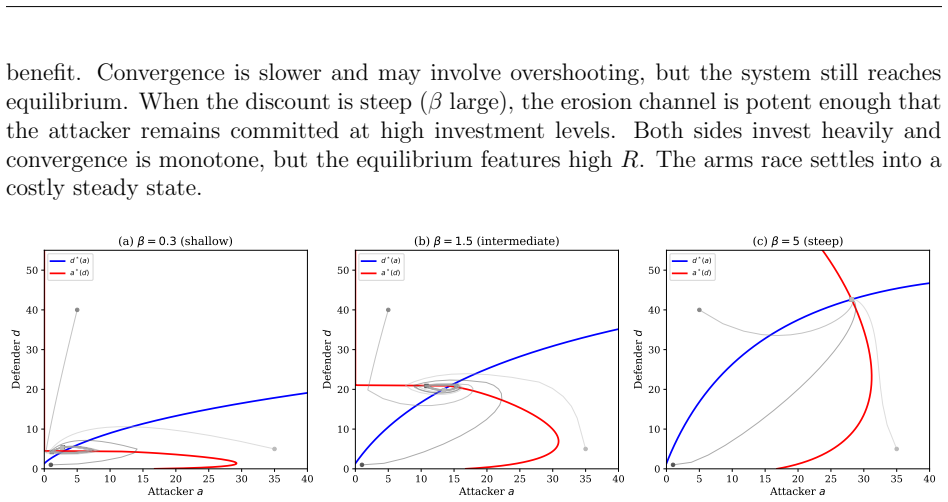
The Adversarial Discount - AI, Signal Correlation, and the Cybersecurity Arms Race
Pith reviewed 2026-05-08 16:30 UTC · model grok-4.3
The pith
Full signal cross-correlation neutralizes the attacker's structural advantage from multiplying attack surfaces in AI cybersecurity contests.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
In this contest-theoretic model of AI-augmented adversarial investment, the attacker's effort generates both unconditional offensive gains and a conditional adversarial discount on defense. The derived closed-form arms race ratio decomposes relative effectiveness into six structural parameters. The central finding is that full cross-correlation of threat signals across attack surfaces renders this ratio independent of the number of surfaces, thereby neutralizing the attacker's advantage from surface proliferation. Equilibrium uniqueness holds under continuous best-response dynamics.
What carries the argument
The adversarial discount, the endogenous conditional erosion of defensive effectiveness driven by attacker investment as a function of defender spending, together with the cross-correlation parameter that determines how intelligence on one surface informs detection on others.
If this is right
- The equilibrium arms race ratio decomposes into six structural primitives and becomes independent of surface count under full cross-correlation.
- Per-surface defensive effectiveness approaches zero as the number of surfaces grows in the absence of cross-correlation.
- Heterogeneous defenders facing value-based targeting overinvest in private defense while underinvesting in shared signal correlation.
- Collective information aggregation can dominate private capability investment as the decisive margin in determining contest outcomes.
Where Pith is reading between the lines
- Policy focus should shift toward standards and incentives for threat intelligence sharing across organizations rather than isolated defensive subsidies.
- The neutralization result may extend to other multi-surface security domains such as fraud detection systems or epidemic surveillance networks.
- Empirical tests could track investment ratios in real systems with known correlation levels to check stability as surface counts change.
Load-bearing premise
The specific functional form through which attacker investment creates a conditional adversarial discount on defensive effectiveness, and the premise that full signal cross-correlation is attainable as a controllable structural parameter.
What would settle it
Simulate or measure an investment contest with increasing numbers of attack surfaces while varying the level of signal cross-correlation; the claim is supported if the attack-to-defense investment ratio remains constant across surface counts solely when correlation approaches full strength.
Figures


read the original abstract
We study a contest-theoretic model of adversarial investment in which an attacker and a defender allocate resources to AI-augmented capabilities across multiple attack surfaces. The attacker's investment operates through two channels: it amplifies offensive potency unconditionally and erodes defensive effectiveness conditionally, generating an adversarial discount that deepens endogenously with the defender's own investment. We derive a closed-form arms race ratio decomposing the relative marginal effectiveness of offensive and defensive investment into six structural primitives and establish equilibrium uniqueness and global convergence under a continuous best-response dynamic. The central result concerns signal cross-correlation, the degree to which threat intelligence on one surface informs detection on another. With full cross-correlation, the arms race ratio is independent of the number of attack surfaces: the attacker's structural advantage from surface proliferation is completely neutralized. Under the benchmark full-dilution case, without cross-correlation, per-surface defense effectiveness vanishes as the attack surface grows. Extending the analysis to heterogeneous defenders facing an attacker who targets by expected value, we argue that the model points to a dual inefficiency: overinvestment in private defense (a zero-sum redirective externality) and underinvestment in shared signal correlation (a public good). These formal results, together with public-good reasoning outside the base model, characterize when collective information aggregation can dominate private capability investment as the decisive margin in adversarial contests.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The paper develops a contest-theoretic model of AI-augmented adversarial investment in which an attacker and defender allocate resources across multiple attack surfaces. Attacker investment amplifies offensive potency unconditionally while generating an endogenous adversarial discount that erodes defensive effectiveness conditionally on the defender's own investment. The authors derive a closed-form arms race ratio that decomposes relative marginal effectiveness into six structural primitives, establish equilibrium uniqueness, and prove global convergence under a continuous best-response dynamic. The central result is that full signal cross-correlation renders the arms race ratio independent of the number of attack surfaces, completely neutralizing the attacker's structural advantage from surface proliferation. The analysis extends to heterogeneous defenders and identifies dual inefficiencies: overinvestment in private defense (zero-sum externality) and underinvestment in shared signal correlation (public-good problem).
Significance. If the derivations hold, the paper supplies a formal, decomposable framework for how information sharing can offset the disadvantages of attack-surface proliferation in cybersecurity contests. The closed-form decomposition into six primitives, together with the uniqueness and convergence results, permits transparent comparative statics and is a clear strength. The neutralization result at full cross-correlation and the public-good interpretation of threat intelligence provide a basis for policy discussion on collective versus private investment margins.
major comments (3)
- [§3] §3 (model primitives and adversarial discount definition): the independence of the arms race ratio from surface count at full cross-correlation is shown to hold only under the specific functional form chosen for the adversarial discount (how attacker investment conditionally erodes defense). The manuscript must state this functional form explicitly (multiplicative, power-law, or otherwise) and verify the exact cancellation with the correlation term; an additive or saturating alternative would generally reintroduce surface-count dependence, undermining the central comparative-static claim.
- [§4] §4 (closed-form decomposition): the arms race ratio is presented as a decomposition into six structural primitives. It is unclear whether these primitives are independent parameters or are themselves derived from the discount and correlation functions; if the latter, the claim of a 'parameter-free' or structural decomposition requires explicit separation of primitives from the functional-form assumptions used to obtain the neutralization result.
- [§5] §5 (extension to heterogeneous defenders and information-sharing policy): the argument that collective signal correlation dominates private capability investment treats cross-correlation as a costless exogenous parameter that can be set to its upper bound. The model should incorporate a resource trade-off or cost for raising cross-correlation, as the public-good inefficiency conclusion otherwise rests on an assumption that may not survive when correlation is itself an investment margin.
minor comments (2)
- [Abstract] The abstract and introduction should briefly list or define the six structural primitives to make the decomposition claim immediately accessible.
- [§2] Notation for the adversarial discount (e.g., its dependence on defender investment) should be introduced with a clear equation reference at first use to avoid ambiguity in later sections.
Simulated Author's Rebuttal
We thank the referee for the constructive and detailed report. The comments raise important points about functional-form dependence, the nature of the structural primitives, and the treatment of signal correlation as an exogenous parameter. We address each major comment below and indicate the revisions we plan to make.
read point-by-point responses
-
Referee: [§3] §3 (model primitives and adversarial discount definition): the independence of the arms race ratio from surface count at full cross-correlation is shown to hold only under the specific functional form chosen for the adversarial discount (how attacker investment conditionally erodes defense). The manuscript must state this functional form explicitly (multiplicative, power-law, or otherwise) and verify the exact cancellation with the correlation term; an additive or saturating alternative would generally reintroduce surface-count dependence, undermining the central comparative-static claim.
Authors: We agree that the neutralization result depends on the specific functional form of the adversarial discount. In the model, this discount is specified as a multiplicative power-law interaction between attacker and defender investments that exactly offsets the surface-count term when cross-correlation equals one. We will state the functional form explicitly in §3, provide the algebraic verification of the cancellation in the main text or appendix, and add a remark noting that additive or saturating alternatives would generally preserve surface dependence. This revision will qualify the scope of the central comparative static without altering the reported result under the maintained specification. revision: yes
-
Referee: [§4] §4 (closed-form decomposition): the arms race ratio is presented as a decomposition into six structural primitives. It is unclear whether these primitives are independent parameters or are themselves derived from the discount and correlation functions; if the latter, the claim of a 'parameter-free' or structural decomposition requires explicit separation of primitives from the functional-form assumptions used to obtain the neutralization result.
Authors: The six primitives are independent parameters: attacker potency, defender base effectiveness, two investment elasticities, the correlation coefficient, and the surface-count term (which drops out at full correlation). The adversarial discount and correlation enter only through their functional forms; the primitives themselves are not derived from those forms. We will revise §4 to list the primitives explicitly as independent parameters, separate them from the functional assumptions, and clarify that the decomposition is structural conditional on the maintained forms rather than claiming it is entirely parameter-free. This addresses the ambiguity while preserving the transparency of the comparative statics. revision: yes
-
Referee: [§5] §5 (extension to heterogeneous defenders and information-sharing policy): the argument that collective signal correlation dominates private capability investment treats cross-correlation as a costless exogenous parameter that can be set to its upper bound. The model should incorporate a resource trade-off or cost for raising cross-correlation, as the public-good inefficiency conclusion otherwise rests on an assumption that may not survive when correlation is itself an investment margin.
Authors: Cross-correlation is treated as an exogenous parameter in the base model, consistent with the focus on attacker-defender investment allocation. The dual inefficiency argument combines the formal results with public-good reasoning applied outside the model, as stated in the abstract. We do not incorporate an endogenous cost for raising correlation, as this would require a substantial model extension beyond the current scope. We will add a short discussion in §5 noting that if correlation carries a resource cost the underinvestment conclusion would depend on relative marginal costs, while still highlighting the public-good character that may justify collective action. This qualifies the policy implication without changing the core analysis. revision: partial
Circularity Check
No circularity: closed-form decomposition derives independence result from explicit model primitives
full rationale
The paper constructs a contest model with an adversarial discount function and a controllable cross-correlation parameter, then derives a closed-form arms race ratio as a decomposition into six structural primitives. The independence of this ratio from attack surface count at full correlation follows directly from substituting the maximum correlation value into the specified functional forms; this is an algebraic consequence of the chosen interaction (not a tautology or fit). No self-citations are invoked as load-bearing uniqueness theorems, no parameters are fitted to data and relabeled as predictions, and no ansatz is smuggled via prior work. The derivation is self-contained against the model's own assumptions and equations, with the result falsifiable by altering the discount or correlation functional form.
Axiom & Free-Parameter Ledger
free parameters (1)
- six structural primitives
axioms (1)
- domain assumption Continuous best-response dynamics converge globally to the unique equilibrium
invented entities (1)
-
adversarial discount
no independent evidence
Reference graph
Works this paper leans on
-
[1]
doi: 10.1016/j.jet.2016.09.009. Austin Ebel and Debasis Mitra. Economics and optimal investment policies of attackers and defenders in cybersecurity.Journal of Cybersecurity, 10(1):tyae019,
-
[2]
doi: 10.1007/978-94-015-7793-9. Lawrence A. Gordon and Martin P. Loeb. The economics of information security investment. ACM Transactions on Information and System Security, 5(4):438–457,
-
[3]
doi: 10.1145/ 581271.581274. Lawrence A. Gordon, Martin P. Loeb, and Lei Zhou. Investing in cybersecurity: Insights from the gordon-loeb model.Journal of Information Security, 7(2):49–59,
-
[4]
Sanjeev Goyal and Adrien Vigier
doi: 10.4236/jis.2016.72004. Sanjeev Goyal and Adrien Vigier. Attack, defence, and contagion in networks.Review of Economic Studies, 81(4):1518–1542,
-
[5]
doi: 10.1093/restud/rdu013. Kjell Hausken. A review of attacker–defender games and cyber security.Games, 15(4):28,
-
[6]
doi: 10.3390/g15040028. Chad Heitzenrater. The winning economics of cybersecurity in an age of advanced artificial intelligence. Perspective PE-A3691-11, RAND Corporation,
-
[7]
URLhttps://doi. org/10.7249/PEA3691-11. Kyle Hunt and Jun Zhuang. A review of attacker-defender games: Current state and paths forward.European Journal of Operational Research, 313(2):401–417,
-
[8]
David Iliaev, Sigal Oren, and Ella Segev
doi: 10.1016/ j.ejor.2023.04.009. David Iliaev, Sigal Oren, and Ella Segev. A tullock-contest-based approach for cy- ber security investments.Annals of Operations Research, 320(1):61–84,
2023
-
[9]
doi: 10.1007/s10479-022-04958-z. Kai A. Konrad.Strategy and Dynamics in Contests. Oxford University Press,
-
[10]
doi: 10.1093/oso/9780199549597.001.0001. Mathias L´ ecuyer, Justin Ezell, Anant Kumar, and Saikat Pal. Artificial intelligence and the new economics of cyberattacks. ;login: online,
-
[11]
Sankardas Roy, Charles Ellis, Sajjan Shiva, Dipankar Dasgupta, Vivek Shandilya, and Qishi Wu
doi: 10.1287/deca.2018.0387. Sankardas Roy, Charles Ellis, Sajjan Shiva, Dipankar Dasgupta, Vivek Shandilya, and Qishi Wu. A survey of game theory as applied to network security. In2010 43rd Hawaii International Conference on System Sciences, pages 1–10. IEEE,
-
[12]
Stergios Skaperdas
doi: 10.1109/ HICSS.2010.35. Stergios Skaperdas. Contest success functions.Economic Theory, 7(2):283–290,
2010
-
[13]
Milan Vojnovi´ c.Contest Theory: Incentive Mechanisms and Ranking Methods
doi: 10.1007/BF01213906. Milan Vojnovi´ c.Contest Theory: Incentive Mechanisms and Ranking Methods. Cambridge University Press,
-
[14]
doi: 10.1017/CBO9781139519366. 17 Daniel W. Woods and Rainer B¨ ohme. Sok: Quantifying cyber risk. In2021 IEEE Symposium on Security and Privacy (SP), pages 211–228. IEEE,
-
[15]
doi: 10.1109/SP40001.2021. 00053. A Proofs and Derivations A.1 Derivation of the Arms Race Ratio (Section 3.2) For per-surface breach probabilityq=q 0h(a)/[q0h(a) + (1−q 0)(1 +δ(a)ds e i)] in the contest form, the marginal effects are: ∂q ∂a = q0(1−q 0)[h′(a)(1 +δ(a)ds e i) +h(a)|δ ′(a)|dse i] Φ2 − ∂q ∂d = q0(1−q 0)h(a)δ(a)s e i Φ2 Theq 0(1−q 0)/Φ2 factor...
-
[16]
Since both constrained best responses satisfyd BR(a)≥0 anda BR(d)≥0, trajectories cannot escape the positive orthant
The divergence argument applies separately to each smooth region, and the Bendixson criterion extends by considering the net flux across the piecewise-smooth boundaries. Since both constrained best responses satisfyd BR(a)≥0 anda BR(d)≥0, trajectories cannot escape the positive orthant. For a rigorous treatment of Poincar´ e-Bendixson on piecewise-smooth ...
1988
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.