Recognition: 2 theorem links
· Lean TheoremScalable Design of Attack-Resilient Controllers for Positive Systems
Pith reviewed 2026-05-12 03:33 UTC · model grok-4.3
The pith
For positive systems under actuator attacks, the optimal policy is linear and can cause unbounded performance degradation when measured output zeros are unstable.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
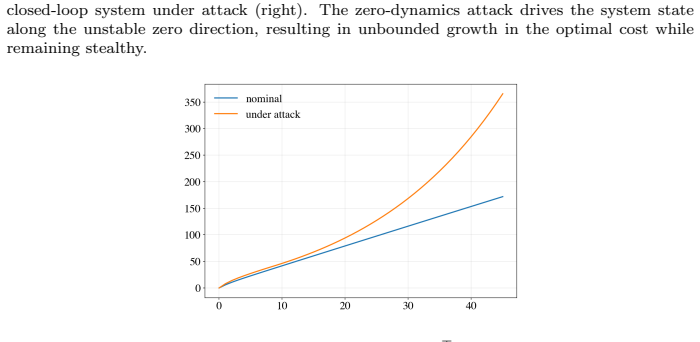
The optimal attack policy is linear; the worst-case performance loss equals the solution of a difference equation (or algebraic equation at infinite horizon); and unbounded degradation occurs whenever the measured output possesses an unstable zero that is not an unstable zero of the performance measure.
What carries the argument
The minimax formulation that solves for the worst-case performance loss under state-dependent attack constraints, yielding a linear attack policy.
If this is right
- The performance loss under attack is obtained by solving a single difference equation or algebraic Riccati-type equation.
- Resilient controllers for the nominal and uncertain cases can be synthesized with linear-regulator methods that exploit positivity.
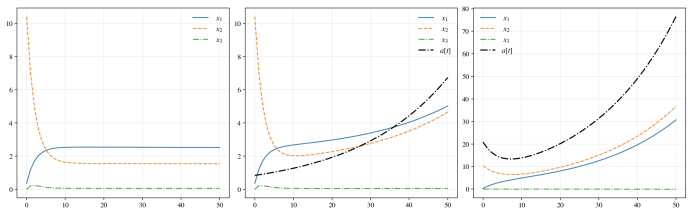
- Numerical examples confirm that these designs limit attack impact at low computational cost.
- Unbounded degradation is possible even without stealthiness requirements once the zero condition holds.
Where Pith is reading between the lines
- Placing the unstable zeros of the measured output to match those of the performance measure could eliminate the unbounded-degradation channel.
- The linearity result simplifies real-time attack detection or compensation because defenders need only guard against linear injections.
- The same positivity-based machinery may reduce the complexity of resilient design for other monotone or cooperative systems.
Load-bearing premise
The adversary can apply arbitrary false-data injections to the actuators and the closed-loop system remains positive for any such attack.
What would settle it
Finding a nonlinear attack policy that produces strictly higher performance loss than the derived linear policy, or measuring bounded degradation in a positive system whose measured output has an unstable zero absent from the performance output.
Figures

read the original abstract
This paper proposes a framework for secure and resilient controller design for positive systems against cyber-attacks. In particular, we consider a network-controlled system where an adversary injects false data into the actuator channels to increase the control cost (performance measure) while penalizing the attack effort and subject to state-dependent constraints. Using a minimax formulation, we analyze the worst-case performance loss caused by such adversaries, which is given by the solution of a difference equation, and an algebraic equation when the time horizon is infinite. We show that the optimal attack policy, among possible nonlinear policies, is linear. Despite the lack of explicit stealthiness constraints, we also show that when the measured output has an unstable zero which is not an unstable zero of the performance measure, the attacks can induce unbounded performance degradation. The proposed framework is also extended to systems with model uncertainty. Numerical examples illustrate the results and demonstrate how tools from positive systems and linear regulator theory can be used to mitigate cyber-attacks with low computational effort.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The manuscript proposes a minimax framework to analyze worst-case performance loss in positive linear systems under actuator false-data injection attacks without explicit stealthiness constraints. It shows that the loss is characterized by the solution of a difference equation (finite horizon) or algebraic equation (infinite horizon), that the optimal attack policy is linear even among nonlinear policies, and that unbounded degradation occurs when the measured output has an unstable zero not shared by the performance measure. The framework is extended to systems with model uncertainty, and numerical examples demonstrate resilient controller design using positive-system tools.
Significance. If the derivations hold, the work provides a scalable, structure-exploiting approach to attack-resilient control for positive systems, with explicit vulnerability conditions based on unstable zeros. The linearity result for optimal attacks and the difference-equation characterization of loss are technically notable strengths, offering falsifiable predictions and low-computational-effort mitigation strategies relevant to networked control applications.
major comments (2)
- [§IV] §IV (Unbounded Degradation Result): The argument that attacks induce unbounded performance degradation when the measured output has an unstable zero not shared by the performance measure relies on positivity and monotonicity of the closed-loop trajectories under attack. However, arbitrary additive injections into the actuator channels (as modeled) can drive state components negative for general nonnegative (A,B) pairs, violating the positivity invariant used to derive the bounds and zero-condition implications. This needs explicit additional assumptions or a restricted attack set to preserve nonnegativity.
- [§III] §III (Optimal Attack Policy): The claim that the optimal attack is linear among all (possibly nonlinear) policies is central to the minimax analysis, but the derivation via the difference equation appears to assume the cost remains convex and the constraints state-dependent without showing how the dynamic programming or algebraic Riccati-like solution enforces linearity under those constraints. The full proof details are required to confirm no post-hoc restrictions are introduced.
minor comments (2)
- [Introduction] The abstract and introduction use 'performance measure' and 'control cost' interchangeably without a precise early definition or reference to the quadratic form in Eq. (1) or equivalent.
- [§V] Numerical examples in §V would benefit from explicit reporting of the condition numbers or eigenvalue locations confirming the unstable-zero hypothesis in the unbounded-degradation case.
Simulated Author's Rebuttal
We thank the referee for the thorough review and valuable comments on our manuscript. The points raised highlight important aspects of the positivity assumption and the optimality proof, which we address below with clarifications and commitments to strengthen the presentation.
read point-by-point responses
-
Referee: [§IV] §IV (Unbounded Degradation Result): The argument that attacks induce unbounded performance degradation when the measured output has an unstable zero not shared by the performance measure relies on positivity and monotonicity of the closed-loop trajectories under attack. However, arbitrary additive injections into the actuator channels (as modeled) can drive state components negative for general nonnegative (A,B) pairs, violating the positivity invariant used to derive the bounds and zero-condition implications. This needs explicit additional assumptions or a restricted attack set to preserve nonnegativity.
Authors: We agree that the unbounded degradation result in Section IV relies on the closed-loop trajectories remaining nonnegative under attack, which is central to invoking positivity and monotonicity properties. The manuscript models positive systems with nonnegative state and input matrices, and the attack is formulated as an additive injection subject to state-dependent constraints that are intended to keep trajectories in the nonnegative orthant. However, the referee correctly notes that this preservation is not stated explicitly for arbitrary attack signals. We will revise Section IV to add an explicit assumption that the admissible attack set is restricted to those injections that preserve nonnegativity of the state (e.g., via bounds derived from the system matrices or an additional constraint in the minimax formulation). This clarification will be incorporated without altering the core result, and we will also note that the result holds under the standard positivity invariance of the closed-loop system. revision: yes
-
Referee: [§III] §III (Optimal Attack Policy): The claim that the optimal attack is linear among all (possibly nonlinear) policies is central to the minimax analysis, but the derivation via the difference equation appears to assume the cost remains convex and the constraints state-dependent without showing how the dynamic programming or algebraic Riccati-like solution enforces linearity under those constraints. The full proof details are required to confirm no post-hoc restrictions are introduced.
Authors: The linearity of the optimal attack policy among nonlinear policies is established in Section III by solving the minimax problem via a difference equation whose solution yields a linear feedback form. The positive-system structure ensures that the value function remains linear (or quadratic in the infinite-horizon case) in the state, preserving convexity of the cost and allowing the dynamic programming recursion to select a linear policy without introducing nonlinearity from the state-dependent constraints. We acknowledge that the manuscript presents the result concisely and that additional steps in the proof would benefit readers. We will expand the derivation in Section III to include the full dynamic programming argument, explicitly showing how the recursion enforces linearity while respecting the constraints, without any post-hoc restrictions. The algebraic Riccati-like equation for the infinite horizon will be similarly detailed. revision: yes
Circularity Check
No significant circularity; derivation follows from standard minimax and positive-system properties
full rationale
The paper's core results—the worst-case performance loss as the solution to a difference/algebraic equation, the linearity of the optimal attack among nonlinear policies, and the unbounded-degradation condition tied to unstable zeros—are obtained directly from the minimax formulation and established positivity/monotonicity properties. No step reduces by construction to a fitted parameter, self-referential definition, or load-bearing self-citation chain. The framework invokes standard tools from positive systems and linear regulator theory as independent inputs rather than smuggling ansatzes or renaming known results. The positivity invariant under attack is an explicit modeling assumption whose violation would falsify the corollary, but this is a limitation of scope, not a circular reduction in the derivation itself.
Axiom & Free-Parameter Ledger
axioms (2)
- domain assumption The plant is a positive linear system.
- domain assumption The adversary solves a minimax problem without stealthiness constraints.
Lean theorems connected to this paper
-
IndisputableMonolith/Cost/FunctionalEquation.leanwashburn_uniqueness_aczel unclearthe optimal value of (6) is pᵀx₀ … pt = s + Aᵀpt+1 − Eᵀ|r + Bᵀpt+1| + Gᵀ|−α + Fᵀpt+1| (eq. 7, 10)
-
IndisputableMonolith/Foundation/DimensionForcing.leanalexander_duality_circle_linking unclearwhen the measured output has an unstable zero … attacks can induce unbounded performance degradation (Theorem 4)
Reference graph
Works this paper leans on
-
[1]
A. Ahl´ en, J. Akerberg, M. Eriksson, A. J. Isaksson, T. Iwaki, K. H. Jo- hansson, S. Knorn, T. Lindh, and H. Sandberg. Toward wireless control in industrial process automation: A case study at a paper mill.IEEE Control Systems Magazine, 39(5):36–57, 2019. 10
work page 2019
-
[2]
S. Amin, X. Litrico, S. S. Sastry, and A. M. Bayen. Cyber security of water scada systems—Part II: Attack detection using enhanced hydrodynamic models.IEEE Transactions on Control Systems Technology, 21(5):1679– 1693, 2012
work page 2012
- [3]
-
[4]
A. Berman and R. Plemmons.Nonnegative matrices in the mathematical sciences.Academic Press, 1979
work page 1979
-
[5]
K. H. Degue, J. Le Ny, and D. Efimov. Stealthy attacks and attack-resilient interval observers.Automatica, 146:110558, 2022
work page 2022
-
[6]
Z. Guo, D. Shi, K. H. Johansson, and L. Shi. Optimal linear cyber-attack on remote state estimation.IEEE Transactions on Control of Network Systems, 4(1):4–13, 2016
work page 2016
-
[7]
Z. Guo, D. Shi, K. H. Johansson, and L. Shi. Worst-case stealthy innovation-based linear attack on remote state estimation.Automatica, 89:117–124, 2018
work page 2018
-
[8]
A. Gurpegui, M. Jeeninga, E. Tegling, and A. Rantzer. Minimax linear regulator problems for positive systems.IEEE Transactions on Automatic Control, pages 1–14, 2026. In press
work page 2026
-
[9]
A. Gurpegui, E. Tegling, and A. Rantzer. Minimax linear optimal control of positive systems.IEEE Control Systems Letters, 7:3920–3925, 2023
work page 2023
-
[10]
N. Hashemi and J. Ruths. Codesign for resilience and performance.IEEE Transactions on Control of Network Systems, 10(3):1387–1399, 2022
work page 2022
-
[11]
K. Hemsley and R. Fisher. A history of cyber incidents and threats in- volving industrial control systems. InInternational Conference on Critical Infrastructure Protection, pages 215–242. Springer, 2018
work page 2018
-
[12]
Kaczorek.Positive 1D and 2D Systems
T. Kaczorek.Positive 1D and 2D Systems. Springer London, 2012
work page 2012
-
[13]
Luenberger.Introduction to dynamical systems.John Wiley & Sons Inc., 1979
D. Luenberger.Introduction to dynamical systems.John Wiley & Sons Inc., 1979
work page 1979
-
[14]
J. Miloˇ sevi´ c, T. Tanaka, H. Sandberg, and K. H. Johansson. Exploiting submodularity in security measure allocation for industrial control systems. InProceedings of the 1st ACM Workshop on the Internet of Safe Things, pages 64–69, 2017
work page 2017
-
[15]
A. T. Nguyen, S. C. Anand, and A. M. H. Teixeira. Scalable and optimal security allocation in networks against stealthy injection attacks.IEEE Transactions on Automatic Control, pages 1–8, 2025
work page 2025
-
[16]
A. Rantzer. Scalable control of positive systems.European Journal of Control, 24:72–80, 2015. 11
work page 2015
-
[17]
H. Sandberg, V. Gupta, and K. H. Johansson. Secure networked control systems.Annual Review of Control, Robotics, and Autonomous Systems, 5(1):445–464, 2022
work page 2022
-
[18]
A. Teixeira, I. Shames, H. Sandberg, and K. H. Johansson. Revealing stealthy attacks in control systems. In2012 50th Annual Allerton Confer- ence on Communication, Control, and Computing (Allerton), pages 1806–
-
[19]
S. Wang, X. Meng, and T. Chen. Wide-area control of power systems through delayed network communication.IEEE Transactions on Control Systems Technology, 20(2):495–503, 2011
work page 2011
-
[20]
G. Wu, J. Sun, and J. Chen. Optimal data injection attacks in cyber- physical systems.IEEE Transactions on cybernetics, 48(12):3302–3312, 2018. Proof of Theorem 2 As it is shown in [9], for the minimax optimal control problem class (6) with linear dynamics, linear stage costs, and homogeneous state-dependent constraints admit linear value functions. Conse...
work page 2018
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.