Recognition: no theorem link
Experimental Examination of Secure Two-Party Controller Computation
Pith reviewed 2026-05-13 02:24 UTC · model grok-4.3
The pith
A secure two-party computation protocol stabilizes an inverted pendulum in real time on a commercial cloud platform despite added communication overhead.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
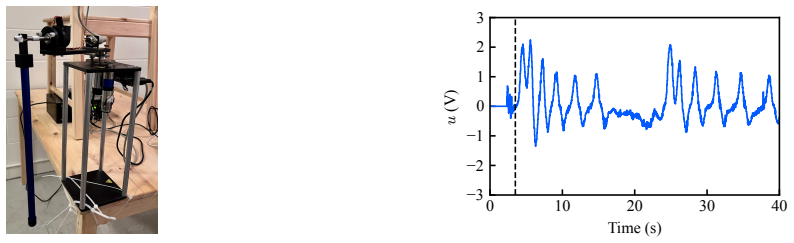
Experimental implementation of the secure two-party computation protocol for dynamic controllers on a commercial cloud platform with an inverted pendulum testbed demonstrates successful stabilization of the pendulum, establishing that the online communication overhead remains compatible with real-time operation.
What carries the argument
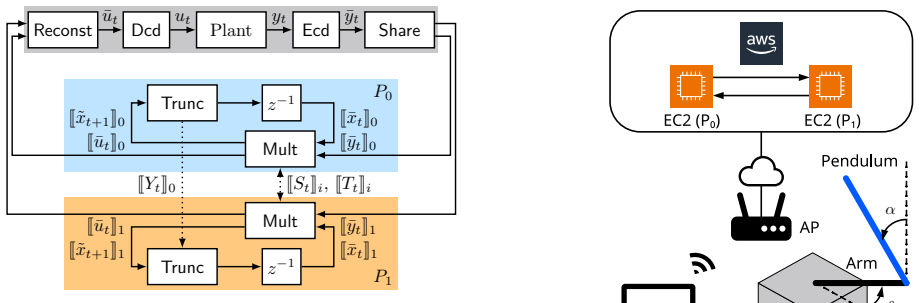
Two-party secure computation protocol over secret sharing for dynamic controllers, which maintains shared encrypted states and eliminates the need for decryption, state reset, or re-encryption during ongoing control.
If this is right
- The protocol supports infinite-horizon control without periodic decryption or controller-state resets.
- Commercial cloud platforms can host the two computing parties for real-time applications when overhead stays within system margins.
- Secret-sharing methods offer an alternative to homomorphic encryption for securing dynamic controllers.
Where Pith is reading between the lines
- The same protocol could be evaluated on other unstable plants such as quadrotors or vehicle dynamics to check broader real-time viability.
- Industrial control networks with moderate latency might adopt the approach for cybersecurity without redesigning timing margins.
- Further tests under variable network conditions would clarify how close the protocol operates to its stability boundary.
Load-bearing premise
The extra communication delays introduced by the two-party protocol remain small enough to stay inside the stability limits of the inverted pendulum system.
What would settle it
A test in which the inverted pendulum loses stability specifically when the two-party protocol runs, but remains stable under an otherwise identical non-secure controller on the same cloud platform.
Figures

read the original abstract
A secure two-party computation protocol for running dynamic controllers over secret sharing has recently been proposed. Unlike encrypted control schemes based on homomorphic encryption, this protocol enables operating dynamic controllers for an infinite time horizon without controller-state decryption, controller-state reset, or input re-encryption. However, the two-party setting introduces additional online communication between the computing parties, which may hinder real-time feasibility. In this study, we demonstrate the feasibility of the protocol through implementation on a commercial cloud platform with an inverted pendulum testbed. Experimental results show that the proposed protocol successfully stabilized the pendulum despite the online communication overhead.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The paper experimentally demonstrates the feasibility of a recently proposed secure two-party computation protocol (based on secret sharing) for running dynamic controllers over an infinite horizon without decryption or state resets. Using an inverted pendulum testbed on a commercial cloud platform, it reports that the protocol successfully stabilized the pendulum despite the additional online communication overhead between the two computing parties.
Significance. If quantitatively substantiated, the result would provide concrete evidence that two-party secure controller computation can meet real-time constraints for unstable plants, supporting privacy-preserving cloud-based control without the limitations of homomorphic encryption schemes. This strengthens the case for the underlying protocol in practical systems and control applications.
major comments (2)
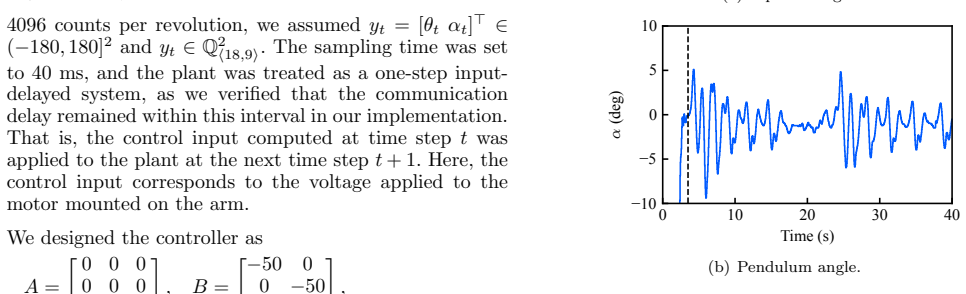
- [Abstract and results section] Abstract and results section: the central claim that stabilization succeeded 'despite the online communication overhead' lacks supporting quantitative data. No measured round-trip latencies, sampling frequency of the controller, closed-loop metrics (settling time, state variance, or failure rates), or direct comparison between the secure protocol and a non-secure baseline are reported, making it impossible to verify that the overhead remained inside the stability margins set by the plant dynamics.
- [Testbed and implementation description] Testbed and implementation description: the manuscript provides no explicit numbers for observed cloud latencies, no statement of the sampling period used on the inverted pendulum, and no analysis of how the two-party communication rounds fit within the real-time requirements. This is load-bearing for the feasibility conclusion, as the weakest assumption is that delays did not violate stability margins.
minor comments (2)
- The abstract would be strengthened by briefly stating the sampling rate and a key performance metric (e.g., maximum observed latency) to allow readers to immediately assess the 'despite' claim.
- Figure captions and result plots (if present) should include error bars or multiple runs to convey variability in the cloud testbed.
Simulated Author's Rebuttal
We thank the referee for the constructive comments on our manuscript. We agree that the experimental results section would be strengthened by including more quantitative data on latencies and performance metrics. We address the major comments point-by-point below and plan to incorporate the suggested revisions.
read point-by-point responses
-
Referee: [Abstract and results section] Abstract and results section: the central claim that stabilization succeeded 'despite the online communication overhead' lacks supporting quantitative data. No measured round-trip latencies, sampling frequency of the controller, closed-loop metrics (settling time, state variance, or failure rates), or direct comparison between the secure protocol and a non-secure baseline are reported, making it impossible to verify that the overhead remained inside the stability margins set by the plant dynamics.
Authors: We agree that these quantitative details are important for verifying the claim. The original manuscript emphasizes the successful stabilization but omits specific numbers. In the revised manuscript, we will add the measured round-trip latencies, the sampling frequency, closed-loop metrics such as settling time and state variance, failure rates, and a direct comparison to the non-secure baseline. This will demonstrate that the overhead was within the stability margins. revision: yes
-
Referee: [Testbed and implementation description] Testbed and implementation description: the manuscript provides no explicit numbers for observed cloud latencies, no statement of the sampling period used on the inverted pendulum, and no analysis of how the two-party communication rounds fit within the real-time requirements. This is load-bearing for the feasibility conclusion, as the weakest assumption is that delays did not violate stability margins.
Authors: We acknowledge the need for more detailed implementation information. The revised manuscript will include explicit numbers for the observed cloud latencies, state the sampling period used, and provide an analysis of how the two-party communication rounds fit within the real-time requirements of the inverted pendulum. This will support the feasibility conclusion by showing that delays did not violate stability margins. revision: yes
Circularity Check
No circularity: purely experimental demonstration
full rationale
The manuscript reports an experimental implementation of a secure two-party controller protocol on a commercial cloud testbed with an inverted pendulum. The central claim is that the system stabilized the pendulum despite communication overhead. No derivation chain, mathematical predictions, fitted parameters, or self-referential equations are present. The result is an empirical observation, not a reduction of any claimed prediction to its own inputs. Self-citations, if any, are not load-bearing for any derivation. This is a standard non-circular experimental paper.
Axiom & Free-Parameter Ledger
Reference graph
Works this paper leans on
-
[1]
Cyber-security enhancement of networked control systems using homomorphic encryption
Kogiso, Kiminao and Fujita, Takahiro. Cyber-security enhancement of networked control systems using homomorphic encryption. IEEE Conference on Decision and Control
-
[2]
Encrypted Control for Networked Systems: An Illustrative Introduction and Current Challenges
Darup, Moritz Schulze and Alexandru, Andreea B and Quevedo, Daniel E and Pappas, George J. Encrypted Control for Networked Systems: An Illustrative Introduction and Current Challenges. IEEE Control Systems Magazine
-
[3]
Encrypting Controller using Fully Homomorphic Encryption for Security of Cyber-Physical Systems
Kim, Junsoo and Lee, Chanhwa and Shim, Hyungbo and Cheon, Jung Hee and Kim, Andrey and Kim, Miran and Song, Yongsoo. Encrypting Controller using Fully Homomorphic Encryption for Security of Cyber-Physical Systems. IFAC-PapersOnLine
-
[4]
Secure and private implementation of dynamic controllers using semi-homomorphic encryption
Murguia, Carlos and Farokhi, Farhad and Shames, Iman. Secure and private implementation of dynamic controllers using semi-homomorphic encryption. IEEE Transactions on Automatic Control
-
[5]
Encrypted dynamic control with unlimited operating time via FIR filters
Schl \" u ter, Nils and Neuhaus, Matthias and Darup, Moritz Schulze. Encrypted dynamic control with unlimited operating time via FIR filters. European Control Conference
-
[6]
Dynamic controller that operates over homomorphically encrypted data for infinite time horizon
Kim, Junsoo and Shim, Hyungbo and Han, Kyoohyung. Dynamic controller that operates over homomorphically encrypted data for infinite time horizon. IEEE Transactions on Automatic Control
-
[7]
Teranishi, Kaoru and Sadamoto, Tomonori and Kogiso, Kiminao. Input-output history feedback controller for encrypted control with leveled fully homomorphic encryption. IEEE Transactions on Control of Network Systems
-
[8]
Lee, Joowon and Lee, Donggil and Kim, Junsoo and Shim, Hyungbo. Encrypted dynamic control exploiting limited number of multiplications and a method using RLWE -based cryptosystem. IEEE Transactions on Systems, Man, and Cybernetics: Systems
-
[9]
Client-aided secure two-party computation of dynamic controllers
Teranishi, Kaoru and Tanaka, Takashi. Client-aided secure two-party computation of dynamic controllers. IEEE Transactions on Control of Network Systems
-
[10]
Efficient multiparty protocols using circuit randomization
Beaver, Donald. Efficient multiparty protocols using circuit randomization. Advances in Cryptology -- CRYPTO '91
-
[11]
SecureML : A system for scalable privacy-preserving machine learning
Mohassel, Payman and Zhang, Yupeng. SecureML : A system for scalable privacy-preserving machine learning. 2017 IEEE Symposium on Security and Privacy
work page 2017
-
[12]
Need for controllers having integer coefficients in homomorphically encrypted dynamic system
Cheon, Jung Hee and Han, Kyoohyung and Kim, Hyuntae and Kim, Junsoo and Shim, Hyungbo. Need for controllers having integer coefficients in homomorphically encrypted dynamic system. IEEE Conference on Decision and Control
-
[13]
Improved primitives for MPC over mixed arithmetic-binary circuits
Escudero, Daniel and Ghosh, Satrajit and Keller, Marcel and Rachuri, Rahul and Scholl, Peter. Improved primitives for MPC over mixed arithmetic-binary circuits. Advances in Cryptology -- CRYPTO 2020
work page 2020
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.