Recognition: no theorem link
PoisonCap: Efficient Hierarchical Temporal Safety for CHERI
Pith reviewed 2026-05-14 02:04 UTC · model grok-4.3
The pith
PoisonCap introduces a poison capability format that enforces strict use-after-free and initialisation safety in CHERI systems without performance overhead.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
PoisonCap uses a new poison capability format to enforce strict use-after-free and initialisation safety for CHERI, replacing the Cornucopia shadow bitmap while automatically zeroing memory on reallocation or optionally trapping on read-before-write, with no fundamental overhead relative to a zeroing baseline.
What carries the argument
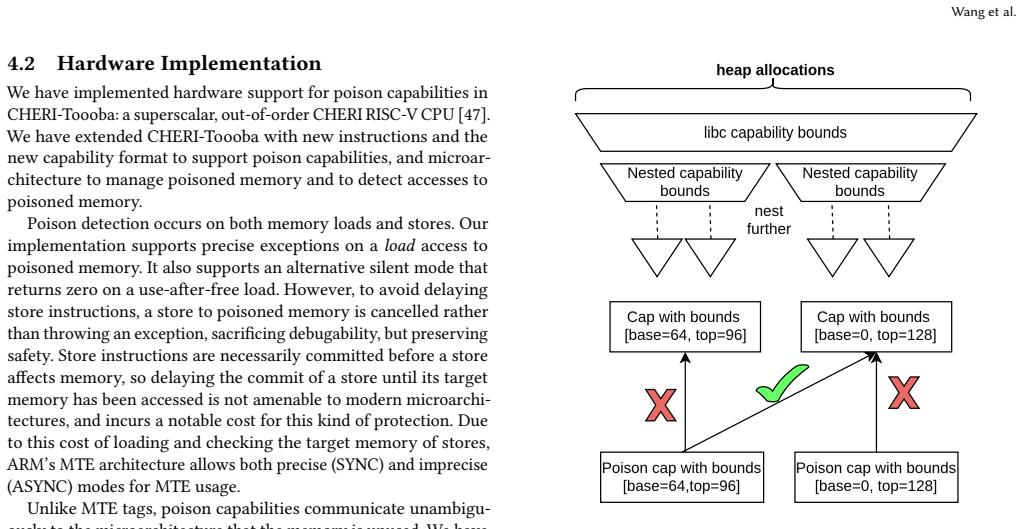
The poison capability format, which marks quarantined memory, communicates state to the microarchitecture for cache management, and enables privilege delegation through capability bounds for nested allocators.
If this is right
- It can fully replace the Cornucopia shadow bitmap for temporal safety enforcement.
- Memory is automatically zeroed on reallocation as a side effect of the poison mechanism.
- An optional trap on read-before-write can be used to enforce initialisation safety.
- Nested allocators can delegate poisoning privilege using capability bounds without affecting upstream allocators.
- Overall CHERI temporal safety is strengthened while matching the performance of a zeroing baseline.
Where Pith is reading between the lines
- The hierarchical delegation feature could reduce the complexity of building safe allocators in CHERI-based operating systems by removing the need for separate tracking structures.
- This design may make it easier to port languages that require strict initialisation guarantees onto CHERI hardware without custom runtime checks.
- If the microarchitectural changes prove cheap, similar poisoning mechanisms could be explored for other capability-based architectures beyond CHERI.
Load-bearing premise
The poison capability format and its microarchitectural state communication can be added with negligible hardware cost and without changing existing CHERI capability semantics or cache behavior.
What would settle it
A hardware prototype or cycle-accurate simulation that measures cache miss rates or logic overhead when poison capabilities are active and finds any increase beyond the baseline zeroing cost would falsify the no-fundamental-overhead claim.
Figures





read the original abstract
In this paper, we present PoisonCap: scalable temporal safety with strict use-after-free protection and initialisation safety for CHERI systems. Efficient memory safety is an increasing priority for programming languages, operating systems, and hardware designs, and CHERI is a leading hardware/software system that provides native spatial safety and a foundation for temporal memory safety. Cornucopia Reloaded, the current state-of-the-art CHERI temporal safety solution, provides use-after-reallocation safety instead of stronger use-after-free safety, and is not able to enforce initialisation safety. We show that a new 'poison' capability format can be used to enforce strict use-after-free and initialisation safety, and also to communicate memory state to the microarchitecture for efficient cache management of quarantined memory. We enable elegant delegation of memory poisoning privilege using capability bounds to allow nested allocators to enforce safety on their consumers without disturbing upstream allocators. PoisonCap can replace the Cornucopia shadow bitmap, and also automatically zeros memory on reallocation, or optionally traps on read-before-write to enforce initialisation safety. As a result, it incurs no fundamental overhead relative to a Cornucopia baseline that zeros before reallocation, strengthening CHERI temporal safety without performance overhead.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The manuscript presents PoisonCap, a mechanism for CHERI systems that introduces a new 'poison' capability format to enforce strict use-after-free protection and initialization safety. It replaces the Cornucopia shadow bitmap, enables automatic zeroing on reallocation (or optional trapping on read-before-write), and supports hierarchical delegation of poisoning privilege via capability bounds. The central claim is that this provides stronger temporal safety than Cornucopia Reloaded while incurring no fundamental overhead relative to a zero-on-reallocation baseline, by communicating memory state to the microarchitecture for efficient cache management of quarantined regions.
Significance. If the hardware feasibility of the poison capability format holds with negligible cost and no disruption to CHERI semantics or cache behavior, the work would meaningfully strengthen temporal memory safety in CHERI without performance penalties. This addresses a key limitation of prior approaches like Cornucopia by adding use-after-free and initialization guarantees, which is valuable for secure systems design in computer architecture.
major comments (2)
- [Abstract] Abstract: The claim that PoisonCap 'incurs no fundamental overhead' relative to a Cornucopia baseline that zeros before reallocation is load-bearing for the contribution but rests on an unelaborated assertion that the poison capability format and microarchitectural state communication add negligible cost; no encoding details, register/tag check modifications, or cache coherence extensions are described to support this.
- [Abstract] Abstract: The assertion that the poison format can be implemented 'without disrupting existing CHERI capability semantics or cache behavior' is central to the no-overhead claim but lacks any analysis of bit requirements in cache line metadata, pipeline stages for checks, or area/latency impact, leaving the hardware feasibility unverified.
minor comments (1)
- [Abstract] Abstract: The phrase 'elegant delegation of memory poisoning privilege using capability bounds' is imprecise; a concrete example of how bounds enable nested allocators without disturbing upstream ones would improve clarity.
Simulated Author's Rebuttal
We thank the referee for their constructive feedback on the abstract claims. We address each major comment below with clarifications drawn from the full manuscript and indicate the revisions made.
read point-by-point responses
-
Referee: [Abstract] Abstract: The claim that PoisonCap 'incurs no fundamental overhead' relative to a Cornucopia baseline that zeros before reallocation is load-bearing for the contribution but rests on an unelaborated assertion that the poison capability format and microarchitectural state communication add negligible cost; no encoding details, register/tag check modifications, or cache coherence extensions are described to support this.
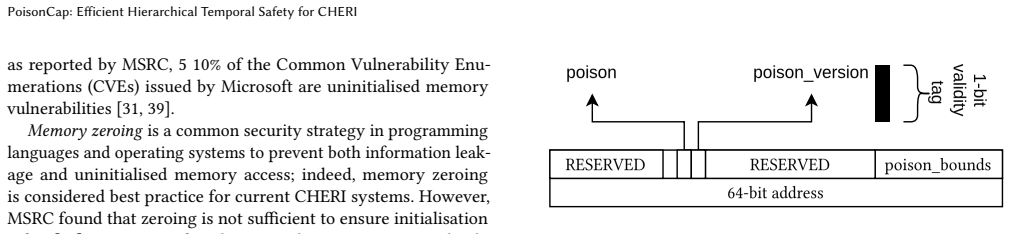
Authors: We agree the abstract is concise and have revised it to reference the supporting details. Section 3.1 describes the poison capability encoding, which reuses the existing CHERI 128-bit capability format by repurposing a single reserved tag bit for the poison state; this requires no new registers and integrates into the standard CHERI tag-check logic without modification. Section 4.2 explains that microarchitectural state for quarantined regions is communicated via existing cache-line metadata bits (no coherence protocol extensions), allowing the baseline zero-on-reallocation behavior to be preserved at the same cost as Cornucopia. The revised abstract now includes a one-sentence pointer to these sections. revision: yes
-
Referee: [Abstract] Abstract: The assertion that the poison format can be implemented 'without disrupting existing CHERI capability semantics or cache behavior' is central to the no-overhead claim but lacks any analysis of bit requirements in cache line metadata, pipeline stages for checks, or area/latency impact, leaving the hardware feasibility unverified.
Authors: Section 5.3 provides the requested qualitative analysis: the poison bit fits within the existing capability tag without increasing cache-line metadata width, and the checks are folded into the single existing CHERI capability-validation pipeline stage, adding zero stages. Because the design reuses CHERI's native tag and bound mechanisms, no semantic changes or cache-behavior alterations occur. We acknowledge that the manuscript does not include quantitative area/latency numbers from synthesis; we have therefore partially revised by expanding the qualitative discussion in Section 5.3 and adding a forward reference in the abstract. revision: partial
Circularity Check
No circularity in derivation chain
full rationale
The paper is a hardware design proposal for PoisonCap temporal safety in CHERI systems. It contains no equations, fitted parameters, or mathematical derivations that could reduce to their own inputs by construction. Claims about replacing Cornucopia's shadow bitmap, enforcing use-after-free and initialization safety, and incurring no fundamental overhead rest on architectural descriptions of a new 'poison' capability format and microarchitectural state, rather than self-definitional loops, fitted-input predictions, or load-bearing self-citations that collapse the result to prior unverified assertions by the same authors. Any concerns about unshown hardware feasibility or cost are issues of correctness or completeness, not circularity per the specified patterns.
Axiom & Free-Parameter Ledger
axioms (2)
- domain assumption CHERI hardware and microarchitecture can support a poison capability format and state communication with negligible cost and no disruption to existing semantics
- domain assumption Capability bounds suffice for safe delegation of poisoning privilege across nested allocators
invented entities (1)
-
Poison capability format
no independent evidence
Reference graph
Works this paper leans on
-
[1]
Sam Ainsworth and Timothy M. Jones. 2020. MarkUs: Drop-in Use-after-Free Prevention for Low-Level Languages. In2020 IEEE Symposium on Security and Privacy (SP). IEEE, San Francisco, CA, USA, 578–591. doi:10.1109/SP40000.2020.00058
-
[2]
Saar Amar, Tony Chen, David Chisnall, Felix Domke, Nathaniel Wesley Filardo, Kunyan Liu, Robert M Norton, Yucong Tao, Robert N M Watson, and Hongyan Xia. 2023. CHERIoT: Rethinking Security for Low-Cost Embedded Systems. (2023)
work page 2023
-
[3]
Apache Software Foundation. 2011. Apache Portable Runtime: Memory Pool Functions. https://apr.apache.org/docs/apr/trunk/group__apr__pools.html. PoisonCap: Efficient Hierarchical Temporal Safety for CHERI
work page 2011
-
[4]
Apache Software Foundation. 2024. NVD - Cve-2019-0196. https://nvd.nist.gov/vuln/detail/cve-2019-0196
work page 2024
-
[5]
Arm Limited. 2025. Arm CPU Security Update: Pointer Authentication. https://developer.arm.com/documentation/110389/latest/
work page 2025
-
[6]
Tim Boland and Paul E. Black. 2012. Juliet 1.1 C/C++ and Java Test Suite. Computer45, 10 (Oct. 2012), 88–90. doi:10.1109/MC.2012.345
-
[7]
Chris Rohlf. 2014. Root Cause by Struct. https://secure.dev/openssl.html
work page 2014
-
[8]
Codasip. 2024. X730 RISC-V Application Processor
work page 2024
-
[9]
CTSRD-CHERI Project. 2026. CTSRD-CHERI/Cheribsd
work page 2026
-
[10]
CTSRD-CHERI Project. 2026. CTSRD-CHERI/Llvm-Project
work page 2026
-
[11]
CTSRD-CHERI Project. 2026. CTSRD-CHERI/Qemu
work page 2026
-
[12]
Cython Development Team. 2025. Extension Types — Cython 3.3.0a0 Documentation. https://cython.readthedocs.io/en/latest/src/userguide/extension_types.html
work page 2025
-
[13]
D. Richard Hipp. 2025. Dynamic Memory Allocation In SQLite. https://sqlite.org/malloc.html
work page 2025
- [14]
-
[15]
Márton Erdős, Sam Ainsworth, and Timothy M. Jones. 2022. MineSweeper: A “Clean Sweep” for Drop-in Use-after-Free Prevention. InProceedings of the 27th ACM International Conference on Architectural Support for Programming Languages and Operating Systems. ACM, Lausanne Switzerland, 212–225. doi:10.1145/3503222.3507712
-
[16]
Jason Evans. 2026. A Scalable Concurrent Malloc(3) Implementation for FreeBSD. (2026)
work page 2026
-
[17]
F5 Networks. 2022. NVD - Cve-2022-41741. https://nvd.nist.gov/vuln/detail/cve-2022-41741
work page 2022
-
[18]
Nathaniel Wesley Filardo, Brett F. Gutstein, Jonathan Woodruff, Jessica Clarke, Peter Rugg, Brooks Davis, Mark Johnston, Robert Norton, David Chisnall, Simon W. Moore, Peter G. Neumann, and Robert N. M. Watson. 2024. Cornucopia Reloaded: Load Barriers for CHERI Heap Temporal Safety. In Proceedings of the 29th ACM International Conference on Architectural ...
- [19]
-
[20]
GitHub, Inc. 2025. NVD - CVE-2025-54874. https://nvd.nist.gov/vuln/detail/CVE-2025-54874
work page 2025
-
[21]
Google Inc. 2026. NVD - CVE-2025-12474. https://nvd.nist.gov/vuln/detail/CVE-2025-12474
work page 2026
-
[22]
Richard Grisenthwaite, Graeme Barnes, Robert N. M. Watson, Simon W. Moore, Peter Sewell, and Jonathan Woodruff. 2023. The Arm Morello Evaluation Platform—Validating CHERI-Based Security in a High-Performance System. IEEE Micro43, 3 (May 2023), 50–57. doi:10.1109/MM.2023.3264676
-
[23]
Merve Gülmez, Håkan Englund, Jan Tobias Mühlberg, and Thomas Nyman
-
[24]
In2025 IEEE Symposium on Security and Privacy (SP)
Mon CHERI: Mitigating Uninitialized Memory Access with Conditional Capabilities. In2025 IEEE Symposium on Security and Privacy (SP). IEEE, San Francisco, CA, USA, 829–847. doi:10.1109/SP61157.2025.00133
-
[25]
Merve Gülmez, Ruben Sturm, Hossam ElAtali, Håkan Englund, Jonathan Woodruff, N. Asokan, and Thomas Nyman. 2026. PICASSO: Scaling CHERI Use-After-Free Protection to Millions of Allocations Using Colored Capabilities. doi:10.48550/ARXIV.2602.09131
-
[26]
Dariy Guzairov, Alex Potanin, Stephen Kell, and Alwen Tiu. 2026. A Security Analysis of CheriBSD and Morello Linux. doi:10.48550/ARXIV.2601.19074
-
[27]
Hanno Böck. 2019. When Your Memory Allocator Hides Security Bugs | The Fuzzing Project. https://blog.fuzzing-project.org/65-When-your-Memory- Allocator-hides-Security-Bugs.html
work page 2019
-
[28]
John L. Henning. 2006. SPEC CPU2006 Benchmark Descriptions.SIGARCH Comput. Archit. News34, 4 (Sept. 2006), 1–17. doi:10.1145/1186736.1186737
-
[29]
Huzaifa S. Sidhpurwala. 2021. 1087195 – (CVE-2010-5298) CVE-2010-5298 Openssl: Freelist Misuse Causing a Possible Use-after-Free. https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2010-5298
work page 2021
-
[30]
Moore, Alex Bradbury, Hongyan Xia, Robert N.M
Alexandre Joannou, Jonathan Woodruff, Robert Kovacsics, Simon W. Moore, Alex Bradbury, Hongyan Xia, Robert N.M. Watson, David Chisnall, Michael Roe, Brooks Davis, Edward Napierala, John Baldwin, Khilan Gudka, Peter G. Neumann, Alfredo Mazzinghi, Alex Richardson, Stacey Son, and A. Theodore Markettos. 2017. Efficient Tagged Memory. In2017 IEEE Internationa...
-
[31]
Alexandre Jean-Michel Procopi Joannou. 2017. High-Performance Memory Safety - Optimizing the CHERI Capability Machine. (Sept. 2017). doi:10.17863/CAM.21472
-
[32]
Joe Bialek. 2020. Solving-Uninitialized-Stack-Memory-on-Windows. https://www.microsoft.com/en-us/msrc/blog/2020/05/solving-uninitialized- stack-memory-on-windows
work page 2020
-
[33]
Butler W. Lampson. 1974. Protection.ACM SIGOPS Operating Systems Review8, 1 (Jan. 1974), 18–24. doi:10.1145/775265.775268
-
[34]
Zhuo Ying Jiang Li. 2025. Exploitation of AIxCC Nginx Bugs: Part I. https://roundofthree.github.io/posts/nginx-aixcc-pwn/
work page 2025
-
[35]
Parkinson, Alex Shamis, Christoph M
Paul Liétar, Theodore Butler, Sylvan Clebsch, Sophia Drossopoulou, Juliana Franco, Matthew J. Parkinson, Alex Shamis, Christoph M. Wintersteiger, and David Chisnall. 2019. Snmalloc: A Message Passing Allocator. InProceedings of the 2019 ACM SIGPLAN International Symposium on Memory Management. ACM, Phoenix AZ USA, 122–135. doi:10.1145/3315573.3329980
-
[36]
Matthew Gretton-Dann. 2018. Arm Community. https://developer.arm.com/community/arm-community-blogs/b/architectures- and-processors-blog/posts/arm-a-profile-architecture-2018-developments- armv85a
work page 2018
-
[37]
MITRE. 2024. NVD - CVE-2020-9273. https://nvd.nist.gov/vuln/detail/CVE-2020-9273
work page 2024
-
[38]
MITRE. 2025. NVD - Cve-2010-5298. https://nvd.nist.gov/vuln/detail/cve-2010-5298
work page 2025
-
[39]
nginx. 2026. Development Guide. https://nginx.org/en/docs/dev/development_guide.html
work page 2026
-
[40]
Nicolas Joly, Saif ElSherei, Saar Amar. 2020. Security Analysis of CHERI ISA. https://www.microsoft.com/en-us/msrc/blog/2020/10/security-analysis-of- cheri-isa
work page 2020
-
[41]
NIST. 2026. Juliet Test Suite Doc. https://samate.nist.gov/SARD
work page 2026
-
[42]
Taehyun Noh, Yingchen Wang, Tal Garfinkel, Mahesh Madhav, Daniel Moghimi, Mattan Erez, and Shravan Narayan. 2026. ARM MTE Performance in Practice (Extended Version). doi:10.48550/ARXIV.2601.11786
-
[43]
Phil Eaton. 2024. Exploring Postgres’s Arena Allocator by Writing an HTTP Server from Scratch. https://enterprisedb.com/blog/exploring-postgress-arena- allocator-writing-http-server-scratch
work page 2024
-
[44]
PostgreSQL. 2026. NVD - CVE-2026-2007. https://nvd.nist.gov/vuln/detail/CVE-2026-2007
work page 2026
-
[45]
Python Software Foundation. 2026. Memory Management. https://docs.python.org/3/c-api/memory.html
work page 2026
-
[46]
Red Hat, Inc. 2014. NVD - Cve-2014-0160. https://nvd.nist.gov/vuln/detail/cve-2014-0160
work page 2014
- [47]
-
[48]
Peter Rugg, Jonathan Woodruff, Alexandre Joannou, and Simon W. Moore. 2024. A Suite of Processors to Explore CHERI-RISC-V Micro Architecture. In2024 27th Euromicro Conference on Digital System Design (DSD). IEEE, Paris, France, 351–360. doi:10.1109/DSD64264.2024.00054
-
[49]
Hiroshi Sasaki, Miguel A. Arroyo, M. Tarek Ibn Ziad, Koustubha Bhat, Kanad Sinha, and Simha Sethumadhavan. 2019. Practical Byte-Granular Memory Blacklisting Using Califorms. doi:10.48550/ARXIV.1906.01838
-
[50]
Konstantin Serebryany, Derek Bruening, Alexander Potapenko, and Dmitriy Vyukov. 2012. AddressSanitizer: A Fast Address Sanity Checker. In2012 USENIX Annual Technical Conference (USENIX ATC 12). 309–318
work page 2012
-
[51]
Shuo Chen. 2015. SSL - Shuo Chen’s Notes. https://www.chenshuo.com/notes/ssl/
work page 2015
-
[52]
SQLite Development Team. 2022. Sqlite/Src/Mem5.c at Master·Sqlite/Sqlite. https://github.com/sqlite/sqlite/blob/master/src/mem5.c
work page 2022
-
[53]
TJ Saunders. 2003. ProFTPD Developer’s Guide: Resource Pools. http://www.castaglia.org/proftpd/doc/devel-guide/internals/pools.html
work page 2003
-
[54]
Robert N. M. Watson, Peter G. Neumann, Jonathan Woodruff, Michael Roe, Hesham Almatary, Jonathan Anderson, John Baldwin, Graeme Barnes, David Chisnall, Jessica Clarke, Brooks Davis, Lee Eisen, Nathaniel Wesley Filardo, Franz A. Fuchs, Richard Grisenthwaite, Alexandre Joannou, Ben Laurie, A. Theodore Markettos, Simon W. Moore, Steven J. Murdoch, Kyndylan N...
-
[55]
Nathaniel Wesley Filardo, Brett F. Gutstein, Jonathan Woodruff, Sam Ainsworth, Lucian Paul-Trifu, Brooks Davis, Hongyan Xia, Edward Tomasz Napierala, Alexander Richardson, John Baldwin, David Chisnall, Jessica Clarke, Khilan Gudka, Alexandre Joannou, A. Theodore Markettos, Alfredo Mazzinghi, Robert M. Norton, Michael Roe, Peter Sewell, Stacey Son, Timothy...
-
[56]
Brian Wickman, Hong Hu, Insu Yun, Daehee Jang, JungWon Lim, Sanidhya Kashyap, and Taesoo Kim. 2021. Preventing Use-After-Free Attacks with Fast Forward Allocation. In30th USENIX Security Symposium (USENIX Security 21). 2453–2470
work page 2021
-
[57]
Norton, David Chisnall, Brooks Davis, Khilan Gudka, Nathaniel W
Jonathan Woodruff, Alexandre Joannou, Hongyan Xia, Anthony Fox, Robert M. Norton, David Chisnall, Brooks Davis, Khilan Gudka, Nathaniel W. Filardo, A. Theodore Markettos, Michael Roe, Peter G. Neumann, Robert N. M. Watson, Wang et al. and Simon W. Moore. 2019. CHERI Concentrate: Practical Compressed Capabilities.IEEE Trans. Comput.68, 10 (Oct. 2019), 1455...
-
[58]
Zhenquan Xu, Gongshen Liu, Tielei Wang, and Hao Xu. 2017. Exploitations of Uninitialized Uses on macOS Sierra. In11th USENIX Workshop on Offensive Technologies (WOOT 17). Received 29 April 2026
work page 2017
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.