Recognition: unknown
Adversarial procurement in blockchains
Pith reviewed 2026-05-08 04:36 UTC · model grok-4.3
The pith
The optimal protocol for procuring expensive tasks in adversarial blockchains incurs loss that scales logarithmically with liveness fault cost times the adversarial network fraction.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
We formalize adversarial procurement as a mechanism design problem balancing liveness fault costs with incentive payments. We show that the loss of the optimal protocol scales logarithmically in the cost of a liveness fault, scaled up by the adversarial fraction of the network. Further, the optimal equilibria designate a single random node as the primary worker and a committee as a fallback. We also characterize the asymptotic regimes where having negative payments is especially helpful.
What carries the argument
A mechanism design model that selects payments and task assignments to rational but possibly adversarial nodes, trading off procurement costs against the risk-weighted cost of liveness failures.
Load-bearing premise
The analysis assumes a fixed and known fraction of adversarial nodes who act as rational economic agents responding to the designed payments and possible slashing.
What would settle it
A simulation or real-world deployment where the observed total loss deviates from the predicted logarithmic scaling when the liveness fault cost is increased while keeping the adversarial fraction fixed.
Figures









read the original abstract
An emerging blockchain protocol design pattern leverages the asymmetry between the computational effort in performing versus verifying tasks. For example, cryptographic validity proofs (e.g., SNARKS) require the prover to expend significant effort demonstrating the correctness of their claim, while the verifiers benefit from extremely easy validation. The operationalization of this paradigm requires efficiently soliciting the performance of expensive tasks in pseudonymous, adversarial environments. We formalize this as a mechanism design question. The protocol balances the economic cost of a liveness fault, where the work is not completed, with the payments required to incentivize specific behavior from candidate suppliers. We show that the loss of the optimal protocol scales logarithmically in the cost of a liveness fault, scaled up by the adversarial fraction of the network. Further, we find that the optimal equilibria have an intuitive structure, allowing us to provide concrete advice to practitioners. Specifically, in many regimes, the optimum designates a single, random node as the primary worker and a committee as a fallback, which is reminiscent of leader-based consensus mechanisms. We also characterize the asymptotic regimes where having negative payments (i.e., slashing in blockchain parlance) is especially helpful.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The paper formalizes the procurement of computationally expensive tasks (e.g., generating SNARK proofs) in pseudonymous, adversarial blockchain environments as a mechanism-design problem. The protocol must trade off the economic cost C of a liveness fault against the payments needed to elicit correct behavior from rational suppliers, a fraction α of whom are adversarial. The central claims are that the minimax loss of the optimal procurement mechanism scales as O(α log C) and that the optimal equilibria have a simple structure: a single randomly chosen primary worker with a committee fallback. The paper further characterizes the regimes in which negative payments (slashing) are beneficial.
Significance. If the derivations are correct, the logarithmic scaling result supplies a clean, falsifiable prediction for the loss incurred by any procurement protocol and supplies concrete design guidance (leader-plus-committee structure, selective use of slashing). The model is parameter-light once α is fixed, and the equilibrium characterization is intuitive and reminiscent of existing leader-based consensus protocols. These features would make the work a useful reference for both theorists and protocol designers.
major comments (2)
- [Theorem 1 / §4] The O(α log C) scaling is the load-bearing claim. The manuscript should state explicitly in the main theorem (presumably §4 or §5) the precise assumptions on the distribution of costs, the information structure, and the solution concept (e.g., dominant-strategy vs. Bayesian Nash) under which the bound is proved; without that list it is impossible to judge whether the log dependence survives modest relaxations of the model.
- [§5] The equilibrium characterization (single random primary + committee fallback) is presented as “optimal in many regimes.” The paper should identify the precise regime boundaries (e.g., ranges of C/α) in which this structure is exactly optimal versus approximately optimal, and should supply the corresponding welfare gap.
minor comments (3)
- [§2] Notation for the loss function L(·) and the payment vector p is introduced late; a compact table of symbols in §2 would improve readability.
- [Introduction] The abstract states the scaling result without a proof sketch; the introduction should contain a one-paragraph high-level derivation outline so that readers can follow the logic before the technical sections.
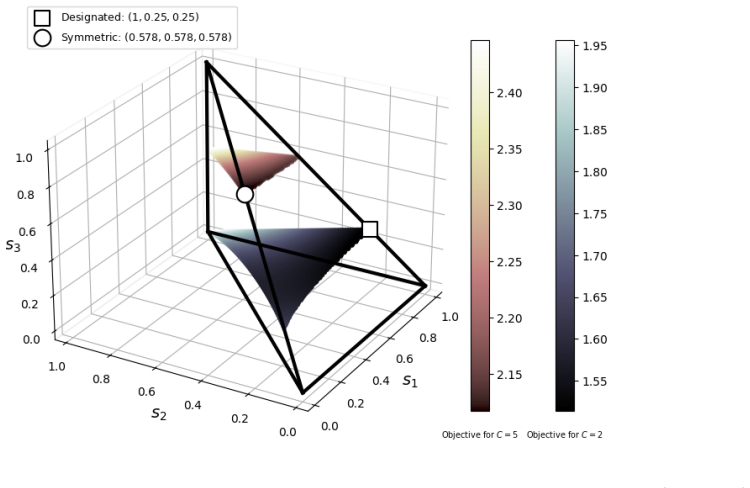
- [Figures 3–5] Several figures compare the optimal mechanism to simple baselines; axis labels and legend entries should be enlarged for print readability.
Simulated Author's Rebuttal
We thank the referee for the careful reading, the positive evaluation, and the recommendation for minor revision. The comments identify useful opportunities to strengthen the clarity of our main results. We address each major comment below.
read point-by-point responses
-
Referee: [Theorem 1 / §4] The O(α log C) scaling is the load-bearing claim. The manuscript should state explicitly in the main theorem (presumably §4 or §5) the precise assumptions on the distribution of costs, the information structure, and the solution concept (e.g., dominant-strategy vs. Bayesian Nash) under which the bound is proved; without that list it is impossible to judge whether the log dependence survives modest relaxations of the model.
Authors: We agree that the assumptions should be stated explicitly within the theorem statement itself. Theorem 1 is proved under i.i.d. costs drawn from a known distribution with bounded support, private information about individual costs, and Bayesian Nash equilibrium as the solution concept. The O(α log C) bound is derived via a minimax argument that relies on these conditions. We will revise the statement of Theorem 1 to include an explicit enumerated list of these assumptions (and any auxiliary technical conditions) immediately preceding the bound. This change will also facilitate discussion of robustness. revision: yes
-
Referee: [§5] The equilibrium characterization (single random primary + committee fallback) is presented as “optimal in many regimes.” The paper should identify the precise regime boundaries (e.g., ranges of C/α) in which this structure is exactly optimal versus approximately optimal, and should supply the corresponding welfare gap.
Authors: The single-random-primary-plus-committee structure is exactly optimal when C/α exceeds a threshold determined by the upper bound on individual costs and the adversarial fraction α; below this threshold the structure remains approximately optimal with a welfare gap bounded by a constant multiple of α. We will expand §5 to state the exact boundary condition in closed form, distinguish the exact-optimality regime from the approximate-optimality regime, and report the associated welfare-gap bounds (which remain O(α log C) in the approximate case). The required calculations follow directly from the existing equilibrium analysis and will be added to the main text. revision: yes
Circularity Check
No significant circularity; derivation self-contained in mechanism-design model
full rationale
The paper formalizes adversarial procurement as a mechanism-design problem balancing liveness-fault cost C against payments to rational suppliers under fixed adversarial fraction α. The claimed O(α log C) loss scaling for the optimal protocol is obtained by minimizing the worst-case loss over feasible mechanisms (including the single-primary-plus-committee structure), without any reduction to fitted data, self-definitional parameters, or load-bearing self-citations. The equilibrium characterization follows directly from the incentive-compatibility constraints stated in the model; no step equates the target result to its own inputs by construction. External validity concerns (pseudonymity) are separate from internal soundness.
Axiom & Free-Parameter Ledger
free parameters (1)
- adversarial fraction
axioms (1)
- domain assumption Participants are rational and respond to economic incentives including payments and slashing
Reference graph
Works this paper leans on
- [1]
- [2]
-
[3]
Axiom. 2023.We are announcing Axiom, the ZK coprocessor for Ethereum.https://x.com/ axiom_xyz/status/1620104714322051073
-
[4]
Moshe Babaioff, Robert Kleinberg, and Christos H Papadimitriou. 2007. Congestion games with malicious players. InProceedings of the 8th ACM conference on Electronic commerce. 103–112
2007
- [5]
-
[6]
2026.High Proposer Payment Alert!https://x.com/mevproposerbot/ status/2024852422460321829
MEV-Boost Bot. 2026.High Proposer Payment Alert!https://x.com/mevproposerbot/ status/2024852422460321829
-
[7]
Brevis. 2025.Announcing Pico Prism, the state-of-the-art zkVM for Ethereum real-time prov- ing.https://x.com/brevis_zk/status/1978430670390133237
-
[8]
2025.Brevis ProverNet Whitepaper.https://brevis.network/whitepaper/ provernet.pdf
Brevis. 2025.Brevis ProverNet Whitepaper.https://brevis.network/whitepaper/ provernet.pdf
2025
- [9]
-
[10]
2021.Endgame.https://vitalik.eth.limo/general/2021/12/06/ endgame.html
Vitalik Buterin. 2021.Endgame.https://vitalik.eth.limo/general/2021/12/06/ endgame.html
2021
-
[11]
2026.Potential ZK-EVM Rollout Tweet.https://x.com/VitalikButerin/ status/2007559523528233041
Vitalik Buterin. 2026.Potential ZK-EVM Rollout Tweet.https://x.com/VitalikButerin/ status/2007559523528233041
- [12]
- [13]
-
[14]
Vincent Conitzer and Makoto Yokoo. 2010. Using mechanism design to prevent false-name manipulations.AI magazine31, 4 (2010), 65–78
2010
-
[15]
Philip Daian, Steven Goldfeder, Tyler Kell, Yunqi Li, Xueyuan Zhao, Iddo Bentov, Lorenz Breidenbach, and Ari Juels. 2020. Flash boys 2.0: Frontrunning in decentralized exchanges, miner extractable value, and consensus instability. In2020 IEEE Symposium on Security and Privacy (SP). IEEE, 910–927
2020
- [16]
-
[17]
2006.Handbook of procurement
Nicola Dimitri, Gustavo Piga, and Giancarlo Spagnolo. 2006.Handbook of procurement. Cam- bridge University Press
2006
-
[18]
2026.Spin up your own Ethereum node.https://ethereum.org/developers/ docs/nodes-and-clients/run-a-node/
Ethereum.org. 2026.Spin up your own Ethereum node.https://ethereum.org/developers/ docs/nodes-and-clients/run-a-node/
2026
-
[19]
2026.Provers – Ethproofs.https://ethproofs.org/provers
Ethproofs. 2026.Provers – Ethproofs.https://ethproofs.org/provers
2026
-
[20]
2024.Introducing BuilderNet.https://collective.flashbots.net/t/ introducing-buildernet/4173
Flashbots. 2024.Introducing BuilderNet.https://collective.flashbots.net/t/ introducing-buildernet/4173
2024
-
[21]
2026.Phase 0 – The Beacon Chain.https://github.com/ethereum/ consensus-specs/blob/master/specs/phase0/beacon-chain.md
Ethereum Foundation. 2026.Phase 0 – The Beacon Chain.https://github.com/ethereum/ consensus-specs/blob/master/specs/phase0/beacon-chain.md
2026
-
[22]
Pranav Garimidi, Michael Neuder, and Tim Roughgarden. 2025. Tullock Contests in the Wild: Applications in Blockchains.ACM SIGecom Exchanges23, 1 (July 2025), 24–34
2025
- [23]
-
[24]
2025.Shipping an L1 zkEVM #1: Realtime Proving.https://blog.ethereum
Sophia Gold. 2025.Shipping an L1 zkEVM #1: Realtime Proving.https://blog.ethereum. org/2025/07/10/realtime-proving
2025
-
[25]
Jens Groth. 2016. On the size of pairing-based non-interactive arguments. InAnnual in- ternational conference on the theory and applications of cryptographic techniques. Springer, 305–326
2016
-
[26]
Lioba Heimbach, Lucianna Kiffer, Christof Ferreira Torres, and Roger Wattenhofer. 2023. Ethereum’s proposer-builder separation: Promises and realities. InProceedings of the 2023 ACM on Internet Measurement Conference. 406–420
2023
-
[27]
2026.Infura – Web3 Development Platform.https://www.infura.io/
Infura. 2026.Infura – Web3 Development Platform.https://www.infura.io/
2026
-
[28]
George Karakostas and Anastasios Viglas. 2003. Equilibria for networks with malicious users. InInternational Symposium on Algorithms and Computation. Springer, 696–704
2003
-
[29]
2023.=nil; Proof Market.https://nil.foundation/blog/post/ proof-market
Mikhail Komarov. 2023.=nil; Proof Market.https://nil.foundation/blog/post/ proof-market
2023
-
[30]
2025.EigenCloud Whitepaper.https://docs.eigencloud.xyz/assets/files/ EigenCloud_Whitepaper-127a6743029d2c4858e7633196c47ea4.pdf 24
Eigen Labs. 2025.EigenCloud Whitepaper.https://docs.eigencloud.xyz/assets/files/ EigenCloud_Whitepaper-127a6743029d2c4858e7633196c47ea4.pdf 24
2025
-
[31]
2025.SP1 Hypercube announcement thread.https://x.com/SuccinctLabs/ status/1925306484281553262
Succinct Labs. 2025.SP1 Hypercube announcement thread.https://x.com/SuccinctLabs/ status/1925306484281553262
-
[32]
Andrew Lewis-Pye, Joachim Neu, Tim Roughgarden, and Luca Zanolini. 2025. Accountable liveness. InProceedings of the 2025 ACM SIGSAC Conference on Computer and Communi- cations Security. 3431–3445
2025
- [33]
-
[34]
2024.Unbundling staking: Towards rainbow staking.https://ethresear
Barnab´ e Monnot. 2024.Unbundling staking: Towards rainbow staking.https://ethresear. ch/t/unbundling-staking-towards-rainbow-staking/18683
2024
-
[35]
Thomas Moscibroda, Stefan Schmid, and Roger Wattenhofer. 2006. When Selfish Meets Evil: Byzantine Players in a Virus Inoculation Game. In25th Annual Symposium on Principles of Distributed Computing (PODC). Denver, Colorado, USA
2006
- [36]
-
[37]
2025.Web3 Pi: Your Ethereum Node on Raspberry Pi.https://www.web3pi.io/
Web3 Pi. 2025.Web3 Pi: Your Ethereum Node on Raspberry Pi.https://www.web3pi.io/
2025
-
[38]
Aaron Roth. 2008. The price of malice in linear congestion games. InInternational Workshop on Internet and Network Economics. Springer, 118–125
2008
-
[39]
2024.Succinct network: Prove the world’s software.https://resources.cryptocompare.com/asset-management/20420/ 1754473565450.pdf
Uma Roy, John Guibas, M Pai, K Kulkarni, and Dan Robinson. 2024.Succinct network: Prove the world’s software.https://resources.cryptocompare.com/asset-management/20420/ 1754473565450.pdf
2024
-
[40]
2026.Blocks Are Dead
Toni Wahrst¨ atter. 2026.Blocks Are Dead. Long Live Blobs.https://ethresear.ch/t/ blocks-are-dead-long-live-blobs/24611
2026
-
[41]
2026.MEV-Boost Dashboard.https://mevboost.pics/
Toni Wahrst¨ atter. 2026.MEV-Boost Dashboard.https://mevboost.pics/
2026
-
[42]
Wenhao Wang, Lulu Zhou, Aviv Yaish, Fan Zhang, Ben Fisch, and Benjamin Livshits. 2025. Prooφ: A ZKP Market Mechanism. InInternational Conference on Financial Cryptography and Data Security. Springer, 180–196
2025
-
[43]
Makoto Yokoo, Yuko Sakurai, and Shigeo Matsubara. 2004. The effect of false-name bids in combinatorial auctions: New fraud in Internet auctions.Games and Economic Behavior46, 1 (2004), 174–188
2004
-
[44]
2025.Boundless Whitepaper.https://read.boundless.network/
RISC Zero. 2025.Boundless Whitepaper.https://read.boundless.network/
2025
-
[45]
ZKsync. 2025.Airbender enters the Ethproofs leaderboard as the fastest zkVM.https: //x.com/zksync/status/1983243385147146291 25 A Section 3 Appendices A.1 Expanded form of(PROG1) It is helpful to consider the protocol objective (PROG1) as a two-layer optimization. Once the equilibrium vectorsis set, then the minimal protocol loss (encoded as payments made...
-
[46]
+ε ′a−1 ≥ C+a 1 +ε ′ = C+a 1 + 1+a C+a = (C+a) 2 C+ 2a+ 1
Plugging in the designated valueε ′ = 1+a C+a to (9), we get C= C+a 1 +ε ′ +. . .+ε ′a−1 ≥ C+a 1 +ε ′ = C+a 1 + 1+a C+a = (C+a) 2 C+ 2a+ 1 . The inequality is true for allC > a 2. Now observe that the RHS of (9) is strictly decreasing inε, and we confirmed that evaluating it atε ′ resulted in a value that was less thanC. The optimal symmetric equilibrium ...
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.