Recognition: 1 theorem link
· Lean TheoremSoK: A Systematic Bidirectional Literature Review of AI & DLT Convergence
Pith reviewed 2026-05-12 04:57 UTC · model grok-4.3
The pith
A systematic review of AI-DLT convergence finds research clustered on execution/consensus layers for AI-to-DLT and data/model layers for DLT-to-AI, with no demonstrated production-scale deployments and calls for cross-layer co-design.
A machine-rendered reading of the paper's core claim, the machinery that carries it, and where it could break.
Core claim
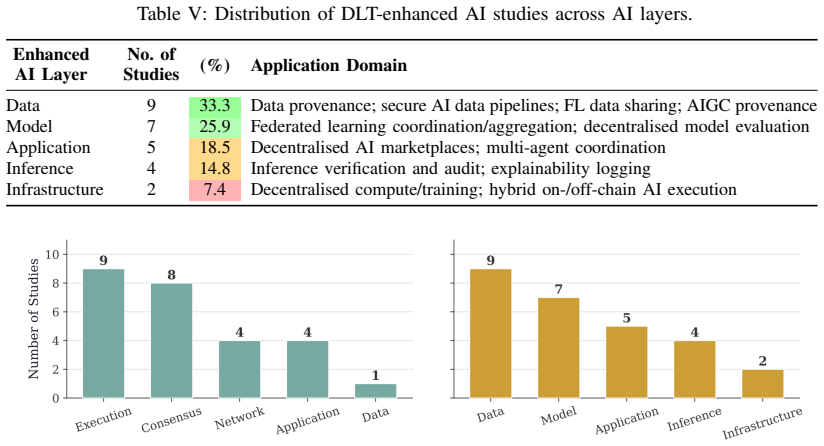
The analysis reveals that most works concentrate on a small subset of layers: execution and consensus for AI-enhanced DLT, data and model for DLT-enhanced AI. Other layers remain comparatively neglected. Despite reported improvements in controlled settings, no study demonstrates deployment at production scale, and the field has not yet offered satisfying answers to fundamental questions around scalability, interoperability, and verifiable execution.
Load-bearing premise
That the chosen time window (2020-2025), peer-reviewed sources, and the five-layer taxonomies for each direction sufficiently capture the architectural interplay without missing major contributions or imposing an artificial structure that distorts the literature.
Figures
read the original abstract
The integration of Artificial Intelligence (AI) with Distributed Ledger Technology (DLT) has become a growing research area, yet contributions tend to cluster around specific application domains or examine only one direction of the integration, leaving the broader architectural interplay between the two technologies poorly understood. This work addresses that gap through a structured, bidirectional review of peer-reviewed studies published between 2020 and 2025. We classify contributions along two directions: AI-enhanced DLT, and DLT-enhanced AI. In the first case, we examine how AI techniques improve DLT systems across five layers: data, network, consensus, execution, and application layers. In the second case, we analyse how DLT supports AI systems across five layers: infrastructure, data, model, inference, and application layers, with particular attention to federated learning, model evaluation, and multi-agent coordination. The analysis reveals that most works concentrate on a small subset of layers: execution and consensus for AI-enhanced DLT, data and model for DLT-enhanced AI. Other layers remain comparatively neglected. Despite reported improvements in controlled settings, no study demonstrates deployment at production scale, and the field has not yet offered satisfying answers to fundamental questions around scalability, interoperability, and verifiable execution. We argue that progress will require cross-layer co-design and empirical validation in real-world settings.
Editorial analysis
A structured set of objections, weighed in public.
Referee Report
Summary. The manuscript presents a systematization of knowledge (SoK) via a bidirectional structured literature review of peer-reviewed AI-DLT papers from 2020-2025. It classifies contributions into AI-enhanced DLT (five layers: data, network, consensus, execution, application) and DLT-enhanced AI (five layers: infrastructure, data, model, inference, application), with emphasis on federated learning and multi-agent systems. The central claims are that works concentrate on execution/consensus and data/model layers respectively, other layers are neglected, no studies show production-scale deployment despite controlled-setting gains, and the field lacks answers on scalability, interoperability, and verifiable execution, calling for cross-layer co-design.
Significance. If the methodological foundations hold, the review would usefully map the AI-DLT landscape, identify under-explored architectural layers, and underscore the controlled-vs-real-world gap. This could steer the community toward empirical validation and integrated designs rather than isolated layer improvements.
major comments (3)
- [Abstract and layer taxonomy descriptions] The concentration claims and 'neglected layers' conclusion rest on the five-layer taxonomies for each direction. The manuscript does not indicate whether these partitions are taken from prior standards or defined ad hoc, nor does it specify disambiguation rules for papers that span multiple layers or how subjective assignment was mitigated. This renders the reported distributions sensitive to the chosen structure and potentially artifactual.
- [Abstract (methodology description)] The abstract states a 'structured, bidirectional review' with a time-bounded search (2020-2025) on peer-reviewed sources, yet supplies no search strings, queried databases, inclusion/exclusion criteria, or inter-rater reliability statistics. These omissions directly undermine the reliability of the layer-concentration statistics and the assertion that other layers remain comparatively neglected.
- [Abstract and conclusions] The claim that 'no study demonstrates deployment at production scale' is load-bearing for the maturity assessment but lacks an explicit, reproducible definition of 'production scale' versus 'controlled settings.' Without stated criteria (e.g., user base, transaction volume, or deployment duration thresholds), the conclusion cannot be independently verified.
Simulated Author's Rebuttal
We thank the referee for the constructive and detailed feedback. The comments highlight important areas for improving transparency and rigor in our SoK. We address each major comment point by point below, with plans for revisions where appropriate.
read point-by-point responses
-
Referee: [Abstract and layer taxonomy descriptions] The concentration claims and 'neglected layers' conclusion rest on the five-layer taxonomies for each direction. The manuscript does not indicate whether these partitions are taken from prior standards or defined ad hoc, nor does it specify disambiguation rules for papers that span multiple layers or how subjective assignment was mitigated. This renders the reported distributions sensitive to the chosen structure and potentially artifactual.
Authors: The taxonomies synthesize standard architectural models from the DLT literature (data, network, consensus, execution, and application layers, as commonly referenced in blockchain surveys) and AI systems (infrastructure, data, model, inference, and application). They are not taken verbatim from any single prior standard but adapted to support the bidirectional analysis. We will add a dedicated subsection in the revised manuscript that (1) traces the rationale for each layer to established references, (2) states explicit disambiguation rules (primary contribution determines the layer; multi-layer papers are flagged and counted separately with discussion), and (3) describes the mitigation of subjectivity (independent classification by two authors on a 20% sample, followed by consensus discussion for the full set). These additions will make the layer distributions and 'neglected layers' conclusion more robust and reproducible. revision: yes
-
Referee: [Abstract (methodology description)] The abstract states a 'structured, bidirectional review' with a time-bounded search (2020-2025) on peer-reviewed sources, yet supplies no search strings, queried databases, inclusion/exclusion criteria, or inter-rater reliability statistics. These omissions directly undermine the reliability of the layer-concentration statistics and the assertion that other layers remain comparatively neglected.
Authors: We acknowledge that the submitted manuscript does not fully document these elements. The review was performed with a structured protocol, but the details were not included in the text. In the revision we will add a methodology subsection that lists the search strings (combinations such as 'artificial intelligence' AND 'distributed ledger' OR 'blockchain' with layer-specific terms), the databases queried (IEEE Xplore, ACM Digital Library, SpringerLink, ScienceDirect, and arXiv cross-checked against peer-reviewed versions), explicit inclusion/exclusion criteria (peer-reviewed English-language papers 2020-2025 focused on AI-DLT integration), and inter-rater reliability (Cohen's kappa for layer assignments). A brief summary of the protocol will also be added to the abstract. This will directly strengthen the reliability of the reported distributions. revision: yes
-
Referee: [Abstract and conclusions] The claim that 'no study demonstrates deployment at production scale' is load-bearing for the maturity assessment but lacks an explicit, reproducible definition of 'production scale' versus 'controlled settings.' Without stated criteria (e.g., user base, transaction volume, or deployment duration thresholds), the conclusion cannot be independently verified.
Authors: We agree that an explicit definition is necessary. In the revised manuscript we will define 'production scale' operationally as a live deployment meeting all three thresholds: (i) at least 500 distinct real-world users, (ii) sustained average daily volume of 1,000+ transactions or model inferences, and (iii) continuous operation for at least three months outside testnets or simulations. We will re-evaluate the surveyed papers against these criteria, report any borderline cases, and confirm that none satisfy the definition. This will make the maturity assessment verifiable while preserving the original observation. revision: yes
Circularity Check
No circularity: observational synthesis from external literature
full rationale
The paper is a systematization of knowledge review that classifies peer-reviewed external studies (2020-2025) according to explicitly stated five-layer taxonomies for AI-enhanced DLT and DLT-enhanced AI. Central claims about layer concentration, absence of production-scale deployments, and open questions on scalability are direct observational aggregates drawn from the reviewed corpus, with no equations, fitted parameters, predictions, or derivations present. No load-bearing self-citations, self-definitional loops, or reductions of results to inputs by construction occur; the methodology is self-contained against the external literature base.
Axiom & Free-Parameter Ledger
axioms (2)
- domain assumption The five layers defined for AI-enhanced DLT (data, network, consensus, execution, application) and for DLT-enhanced AI (infrastructure, data, model, inference, application) form a valid and exhaustive classification scheme.
- domain assumption Peer-reviewed publications from 2020-2025 provide a representative sample of the AI-DLT research landscape.
Lean theorems connected to this paper
-
IndisputableMonolith/Foundation/AbsoluteFloorClosure.lean; IndisputableMonolith/Cost/FunctionalEquation.leanreality_from_one_distinction; washburn_uniqueness_aczel unclear?
unclearRelation between the paper passage and the cited Recognition theorem.
We classify contributions along two directions: AI-enhanced DLT... across five layers: data, network, consensus, execution, and application layers. ... DLT-enhanced AI... across five layers: infrastructure, data, model, inference, and application layers... most works concentrate on a small subset of layers: execution and consensus... data and model...
What do these tags mean?
- matches
- The paper's claim is directly supported by a theorem in the formal canon.
- supports
- The theorem supports part of the paper's argument, but the paper may add assumptions or extra steps.
- extends
- The paper goes beyond the formal theorem; the theorem is a base layer rather than the whole result.
- uses
- The paper appears to rely on the theorem as machinery.
- contradicts
- The paper's claim conflicts with a theorem or certificate in the canon.
- unclear
- Pith found a possible connection, but the passage is too broad, indirect, or ambiguous to say the theorem truly supports the claim.
Reference graph
Works this paper leans on
-
[1]
Proof- of-learning: A blockchain consensus mechanism based on machine learning competitions,
F. Bravo-Marquez, S. Reeves, and M. Ugarte, “Proof- of-learning: A blockchain consensus mechanism based on machine learning competitions,” inProc. IEEE Int’l Conf. on Decentralized Applications and Infrastructures (DAPPCON). IEEE, 2019, pp. 119–124
work page 2019
-
[2]
A survey on zero-knowledge machine learning,
Z. Liet al., “A survey on zero-knowledge machine learning,”arXiv preprint arXiv:2501.01234, 2025
-
[3]
Ai verification on blockchain: Conver- gence of zero-knowledge proofs and oracles,
N. Jagannath, “Ai verification on blockchain: Conver- gence of zero-knowledge proofs and oracles,” 2025
work page 2025
-
[4]
Blockchain-enabled federated learning: A comprehensive survey,
Y . Quet al., “Blockchain-enabled federated learning: A comprehensive survey,”IEEE Access, 2022
work page 2022
-
[5]
Blockchain-based federated learning for securing inter- net of things: A comprehensive survey,
W. Issa, N. Moustafa, B. Turnbull, N. Sohrabi, and Z. Tari, “Blockchain-based federated learning for securing inter- net of things: A comprehensive survey,”ACM Computing Surveys, vol. 55, no. 9, pp. 191:1–191:37, 2023
work page 2023
-
[6]
Blockchain-empowered Federated Learning: Challenges, Solutions, and Future Directions,
J. Zhu, J. Cao, D. Saxena, S. Jiang, and H. Ferradi, “Blockchain-empowered Federated Learning: Challenges, Solutions, and Future Directions,”ACM Computing Surveys, vol. 55, no. 11, 11 2023. [Online]. Available: https://dl.acm.org/doi/pdf/10.1145/3570953
-
[7]
Ai agents meet blockchain: A survey on secure and scalable collaboration for multi-agents,
M. M. Karim, D. H. Van, S. Khan, Q. Qu, and Y . Kholodov, “Ai agents meet blockchain: A survey on secure and scalable collaboration for multi-agents,” Future Internet, vol. 17, no. 2, p. 57, 2025
work page 2025
-
[8]
Architecture of automated crypto-finance agent,
A. Raheman, A. Kolonin, B. Goertzel, G. Hegykozi, and I. Ansari, “Architecture of automated crypto-finance agent,” inInt’l Symposium on Knowledge, Ontology and Theory (KNOTH), 2021, pp. 10–14
work page 2021
-
[9]
(2024) Bittensor: A peer-to- peer intelligence market
Bittensor Foundation. (2024) Bittensor: A peer-to- peer intelligence market. [Online]. Available: https: //bittensor.com/whitepaper
work page 2024
-
[10]
The evolution and design of digital economies,
F. Foundation, “The evolution and design of digital economies,” https://fetch.ai/blog/ fetch-ai-economics-white-paper, 2018, accessed August 2025
work page 2018
-
[11]
Singularitynet: A decentralized ai net- work (whitepaper),
S. Foundation, “Singularitynet: A decentralized ai net- work (whitepaper),” whitepaper, 2018
work page 2018
-
[12]
S. K. Singh, S. Rathore, and J. H. Park, “BlockIoTIntelligence: A Blockchain-enabled Intelligent IoT Architecture with Artificial Intelligence,”Future Generation Computer Systems, vol. 110, pp. 721–743, 9 2020. [Online]. Available: https://www.sciencedirect. com/science/article/pii/S0167739X19316474
work page 2020
-
[13]
Blockchain-enabled Federated Learning: A Survey,
Y . Qu, M. P. Uddin, C. Gan, Y . Xiang, L. Gao, and J. Yearwood, “Blockchain-enabled Federated Learning: A Survey,”ACM Computing Surveys, vol. 55, no. 4, p. 70, 4 2022. [Online]. Available: https://dl.acm.org/doi/ pdf/10.1145/3524104
-
[14]
Systematic Review on AI- Blockchain Based E-Healthcare Records Management Systems,
A. Haddad, M. H. Habaebi, M. R. Islam, N. F. Has- bullah, and S. A. Zabidi, “Systematic Review on AI- Blockchain Based E-Healthcare Records Management Systems,”IEEE Access, vol. 10, pp. 94 583–94 615, 2022
work page 2022
-
[15]
Blockchain for AI: Review and open research challenges,
K. Salah, M. H. U. Rehman, N. Nizamuddin, and A. Al- Fuqaha, “Blockchain for AI: Review and open research challenges,”IEEE Access, vol. 7, pp. 10 127–10 149, 2019
work page 2019
-
[16]
J. L. Vilas-Boas, J. J. Rodrigues, and A. M. Alberti, “Convergence of Distributed Ledger Technologies with Digital Twins, IoT, and AI for fresh food logistics: Challenges and opportunities,”Journal of Industrial Information Integration, vol. 31, p. 100393, 2 2023. [Online]. Available: https://www.sciencedirect. com/science/article/pii/S2452414X22000607
work page 2023
-
[17]
S. Gupta, S. Modgil, T. M. Choi, A. Kumar, and J. Antony, “Influences of artificial intelligence and blockchain technology on financial resilience of supply chains,”International Journal of Production Economics, vol. 261, p. 108868, 7 2023. [Online]. Available: https://www.sciencedirect.com/science/article/ pii/S0925527323001007
work page 2023
-
[18]
Artificial intelligence for the metaverse: A survey,
T. Huynh-The, Q. V . Pham, X. Q. Pham, T. T. Nguyen, Z. Han, and D. S. Kim, “Artificial intelligence for the metaverse: A survey,”Engineering Applications of Artificial Intelligence, vol. 117, p. 105581, 1
-
[19]
Available: https://www.sciencedirect
[Online]. Available: https://www.sciencedirect. com/science/article/pii/S0952197622005711
-
[20]
AI-enhanced blockchain technology: A review of advancements and opportunities,
D. Ressi, R. Romanello, C. Piazza, and S. Rossi, “AI-enhanced blockchain technology: A review of advancements and opportunities,”Journal of Network and Computer Applications, vol. 225, p. 103858, 5 2024. [Online]. Available: https://www.sciencedirect. com/science/article/pii/S1084804524000353
work page 2024
-
[21]
DLchain: Blockchain with deep learning as proof-of-useful-work,
X. Chenli, Z. Liu, Z. Zheng, and Y . Zhou, “DLchain: Blockchain with deep learning as proof-of-useful-work,” inProc. IEEE Int’l Conf. on Blockchain. IEEE, 2021, pp. 266–273
work page 2021
-
[22]
Skychain: A deep reinforcement learning-empowered dynamic blockchain sharding system,
J. Zhang, Z. Hong, X. Qiu, Y . Zhan, S. Guo, and W. Chen, “Skychain: A deep reinforcement learning-empowered dynamic blockchain sharding system,” inProc. IEEE ICCCN, 2020, pp. 1–9
work page 2020
-
[23]
Auto-tuning with reinforcement learning for permissioned blockchain systems,
M. Li, Y . Wang, S. Ma, C. Liu, D. Huo, Y . Wang, and Z. Xu, “Auto-tuning with reinforcement learning for permissioned blockchain systems,”Proceedings of the VLDB Endowment, vol. 16, no. 5, pp. 1000–1012, 2023
work page 2023
-
[24]
L. Liu and Z. Li, “Permissioned blockchain and deep rein- forcement learning enabled security and energy efficient healthcare internet of things,”Ieee Access, vol. 10, pp. 53 640–53 651, 2022
work page 2022
-
[25]
Ai-enabled blockchain: An outlier-aware consensus protocol for blockchain-based iot networks,
M. Salimitari, M. Joneidi, and M. Chatterjee, “Ai-enabled blockchain: An outlier-aware consensus protocol for blockchain-based iot networks,” in2019 IEEE global communications conference (GLOBECOM). IEEE, 2019, pp. 1–6
work page 2019
-
[26]
Predicting blockchain forks with machine learning techniques,
M. Mohammadi, N. Alikhani, and M. Li, “Predicting blockchain forks with machine learning techniques,”Fu- ture Generation Computer Systems, vol. 137, pp. 12–24, 2022
work page 2022
-
[27]
Deep autoencoder ensembles for anomaly detection on blockchain,
F. Scicchitano, A. Liguori, M. Guarascio, E. Ritacco, and G. Manco, “Deep autoencoder ensembles for anomaly detection on blockchain,” inInternational Symposium on Methodologies for Intelligent Systems. Springer, 2020, pp. 448–456
work page 2020
-
[28]
Reinforcement learning- based automated market maker for decentralized ex- changes,
T. Zhang, B. Li, and X. Wang, “Reinforcement learning- based automated market maker for decentralized ex- changes,”IEEE Transactions on Computational Social Systems, vol. 10, no. 2, pp. 355–367, 2023
work page 2023
-
[29]
Blockchain-based federated learning: A survey and new perspectives
W. Ning, Y . Zhu, C. Song, H. Li, L. Zhu, J. Xie, T. Chen, T. Xu, X. Xu, and J. Gao, “Blockchain-based federated learning: A survey and new perspectives.”Applied Sci- ences (2076-3417), vol. 14, no. 20, 2024
work page 2076
-
[30]
A survey on blockchain-based federated learning,
L. Wu, W. Ruan, J. Hu, and Y . He, “A survey on blockchain-based federated learning,”Future Internet, vol. 15, no. 12, p. 400, 2023
work page 2023
-
[31]
Blockchain meets machine learning: a survey,
S. Kayikci and T. M. Khoshgoftaar, “Blockchain meets machine learning: a survey,”Journal of Big Data, vol. 11, no. 1, p. 9, 2024
work page 2024
-
[32]
A survey of blockchain, artificial intelligence, and edge computing for web 3.0,
J. Zhu, F. Li, and J. Chen, “A survey of blockchain, artificial intelligence, and edge computing for web 3.0,” Computer Science Review, vol. 54, p. 100667, 2024
work page 2024
-
[33]
Is your ai truly yours? leveraging blockchain for copyrights, provenance, and lineage,
Q. Wang, G. Yu, Y . Sai, H. D. Bandara, and S. Chen, “Is your ai truly yours? leveraging blockchain for copyrights, provenance, and lineage,”IEEE Transactions on Services Computing, 2025
work page 2025
-
[34]
Toward decentralized intelligence: A systematic literature review of blockchain-enabled ai systems,
M. S. Al Jasem, T. De Clark, and A. K. Shrestha, “Toward decentralized intelligence: A systematic literature review of blockchain-enabled ai systems,”Information, vol. 16, no. 9, p. 765, 2025
work page 2025
-
[35]
Hidden technical debt in machine learn- ing systems,
D. Sculley, G. Holt, D. Golovin, E. Davydov, T. Phillips, D. Ebner, V . Chaudhary, M. Young, J.-F. Crespo, and D. Dennison, “Hidden technical debt in machine learn- ing systems,”Advances in neural information processing systems, vol. 28, 2015
work page 2015
-
[36]
Soft- ware engineering for machine learning: A case study,
S. Amershi, A. Begel, C. Bird, R. DeLine, H. Gall, E. Ka- mar, N. Nagappan, B. Nushi, and T. Zimmermann, “Soft- ware engineering for machine learning: A case study,” in2019 IEEE/ACM 41st International Conference on Software Engineering: Software Engineering in Practice (ICSE-SEIP). IEEE, 2019, pp. 291–300
work page 2019
-
[37]
In-datacenter performance analysis of a tensor processing unit,
N. P. Jouppi, C. Young, N. Patil, D. Patterson, G. Agrawal, R. Bajwa, S. Bates, S. Bhatia, N. Boden, A. Borchers et al., “In-datacenter performance analysis of a tensor processing unit,” inProceedings of the 44th annual in- ternational symposium on computer architecture, 2017, pp. 1–12
work page 2017
-
[38]
Large scale distributed deep networks,
J. Dean, G. Corrado, R. Monga, K. Chen, M. Devin, M. Mao, M. Ranzato, A. Senior, P. Tucker, K. Yang et al., “Large scale distributed deep networks,”Advances in neural information processing systems, vol. 25, 2012
work page 2012
-
[39]
Why and where: A characterization of data provenance,
P. Buneman, S. Khanna, and T. Wang-Chiew, “Why and where: A characterization of data provenance,” in International conference on database theory. Springer, 2001, pp. 316–330
work page 2001
-
[40]
Automating large-scale data quality verification,
S. Schelter, D. Lange, P. Schmidt, M. Celikel, F. Biess- mann, and A. Grafberger, “Automating large-scale data quality verification,”Proceedings of the VLDB Endow- ment, vol. 11, no. 12, pp. 1781–1794, 2018
work page 2018
-
[41]
Model cards for model reporting,
M. Mitchell, S. Wu, A. Zaldivar, P. Barnes, L. Vasserman, B. Hutchinson, E. Spitzer, I. D. Raji, and T. Gebru, “Model cards for model reporting,” inProceedings of the conference on fairness, accountability, and transparency, 2019, pp. 220–229
work page 2019
-
[42]
Cryptonets: Applying neural networks to encrypted data with high throughput and accuracy,
R. Gilad-Bachrach, N. Dowlin, K. Laine, K. Lauter, M. Naehrig, and J. Wernsing, “Cryptonets: Applying neural networks to encrypted data with high throughput and accuracy,” inInternational conference on machine learning. PMLR, 2016, pp. 201–210
work page 2016
-
[43]
Privacy-preserving deep learning via weight transmission,
T. T. Phuonget al., “Privacy-preserving deep learning via weight transmission,”IEEE Transactions on Information Forensics and Security, vol. 14, no. 11, pp. 3003–3015, 2019
work page 2019
-
[44]
Dignum,Responsible artificial intelligence: how to develop and use AI in a responsible way
V . Dignum,Responsible artificial intelligence: how to develop and use AI in a responsible way. Springer, 2019, vol. 2156
work page 2019
-
[45]
A review on layered architecture and application domains of blockchain technology,
M. Birje, R. Goudar, C. Rakshitha, and M. T. Tapale, “A review on layered architecture and application domains of blockchain technology,” in2022 International Confer- ence on Electrical, Computer and Energy Technologies (ICECET). IEEE, 2022, pp. 1–5
work page 2022
-
[46]
Understanding blockchain: Definitions, architecture, de- sign, and system comparison,
M. H. Tabatabaei, R. Vitenberg, and N. R. Veeraragavan, “Understanding blockchain: Definitions, architecture, de- sign, and system comparison,”Computer Science Review, vol. 50, p. 100575, 2023
work page 2023
-
[47]
M. B. Saif, S. Migliorini, and F. Spoto, “A survey on data availability in layer 2 blockchain rollups: Open challenges and future improvements,”Future Internet, vol. 16, no. 9, p. 315, 2024
work page 2024
-
[48]
A taxonomy of blockchain- based systems for architecture design,
X. Xu, I. Weber, M. Staples, L. Zhu, J. Bosch, L. Bass, C. Pautasso, and P. Rimba, “A taxonomy of blockchain- based systems for architecture design,” in2017 IEEE international conference on software architecture (ICSA). IEEE, 2017, pp. 243–252
work page 2017
-
[49]
Sok: Consensus in the age of blockchains,
S. Bano, A. Sonnino, M. Al-Bassam, S. Azouvi, P. Mc- Corry, S. Meiklejohn, and G. Danezis, “Sok: Consensus in the age of blockchains,” inProceedings of the 1st ACM Conference on Advances in Financial Technologies, 2019, pp. 183–198
work page 2019
-
[50]
A survey of blockchain consensus protocols,
J. Xu, C. Wang, and X. Jia, “A survey of blockchain consensus protocols,”ACM Computing Surveys, vol. 55, no. 13s, pp. 1–35, 2023
work page 2023
-
[51]
A taxonomy for characterizing blockchain systems,
F. E. Alzhrani, K. A. Saeedi, and L. Zhao, “A taxonomy for characterizing blockchain systems,”IEEE Access, vol. 10, pp. 110 568–110 589, 2022
work page 2022
-
[52]
B. Bellaj, A. Ouaddah, E. Bertin, N. Crespi, and A. Mezri- oui, “Drawing the boundaries between blockchain and blockchain-like systems: A comprehensive survey on dis- tributed ledger technologies,”Proceedings of the IEEE, vol. 112, no. 3, pp. 247–299, 2024
work page 2024
-
[53]
Taxonomy of blockchain technologies. principles of identification and classifica- tion,
P. Tasca and C. J. Tessone, “Taxonomy of blockchain technologies. principles of identification and classifica- tion,”arXiv:1708.04872, 2017
-
[54]
{COLE}: A column- based learned storage for blockchain systems,
C. Zhang, C. Xu, H. Hu, and J. Xu, “{COLE}: A column- based learned storage for blockchain systems,” in22nd USENIX Conference on File and Storage Technologies (FAST 24), 2024, pp. 329–345
work page 2024
-
[55]
S. Maaroufi and S. Pierre, “Bcool: A novel blockchain congestion control architecture using dynamic service function chaining and machine learning for next genera- tion vehicular networks,”IEEE Access, vol. 9, pp. 53 096– 53 122, 2021
work page 2021
-
[56]
J. Kim, M. Nakashima, W. Fan, S. Wuthier, X. Zhou, I. Kim, and S.-Y . Chang, “A machine learning approach to anomaly detection based on traffic monitoring for secure blockchain networking,”IEEE Transactions on Network and Service Management, vol. 19, no. 3, pp. 3619–3632, 2022
work page 2022
-
[57]
De- centralized security and data integrity of blockchain using deep learning techniques,
S. T. Abdulrazzaq, F. S. Omar, and M. A. Mustafa, “De- centralized security and data integrity of blockchain using deep learning techniques,”Periodicals of Engineering and Natural Sciences (PEN), vol. 8, no. 3, pp. 1911–1923, 2020
work page 1911
-
[58]
Z. Ning, S. Sun, X. Wang, L. Guo, G. Wang, X. Gao, and R. Y . Kwok, “Intelligent resource allocation in mobile blockchain for privacy and security transactions: a deep reinforcement learning based approach,”Science China Information Sciences, vol. 64, no. 6, p. 162303, 2021
work page 2021
-
[59]
W. Villegas, R. Guti ´errez, and J. Govea, “Adaptive con- sensus optimization in blockchain using reinforcement learning and validation in adversarial environments,” Frontiers in Artificial Intelligence, vol. 8, p. 1672273, 2025
work page 2025
-
[60]
Secure trust- based delegated consensus for blockchain frameworks using deep reinforcement learning,
Y . Goh, J. Yun, D. Jung, and J.-M. Chung, “Secure trust- based delegated consensus for blockchain frameworks using deep reinforcement learning,”IEEE access, vol. 10, pp. 118 498–118 511, 2022
work page 2022
-
[61]
K. Venkatesan and S. B. Rahayu, “Blockchain secu- rity enhancement: an approach towards hybrid consensus algorithms and machine learning techniques,”Scientific Reports, vol. 14, no. 1, p. 1149, 2024
work page 2024
-
[62]
Proof of learning (pole): Empowering machine learning with consensus building on blockchains,
Y . Lan, Y . Liu, B. Li, and C. Miao, “Proof of learning (pole): Empowering machine learning with consensus building on blockchains,” inProceedings of the AAAI Conference on Artificial Intelligence, vol. 35, no. 18, 2021, pp. 16 063–16 066
work page 2021
-
[63]
From cryptic to clear-training on llm explanations to detect smart contract vulnerabilities,
Y . Chen, Z. Sun, G. Wang, Q. Liang, X. Yu, and D. Hao, “From cryptic to clear-training on llm explanations to detect smart contract vulnerabilities,”ACM Transactions on Software Engineering and Methodology, 2025
work page 2025
-
[64]
Deep learning-based solution for smart contract vulnerabilities detection,
X. Tang, Y . Du, A. Lai, Z. Zhang, and L. Shi, “Deep learning-based solution for smart contract vulnerabilities detection,”Scientific Reports, vol. 13, no. 1, p. 20106, 2023
work page 2023
-
[65]
Deep learning-based malicious smart contract and intru- sion detection system for iot environment,
H. Shah, D. Shah, N. K. Jadav, R. Gupta, S. Tanwar, O. Alfarraj, A. Tolba, M. S. Raboaca, and V . Marina, “Deep learning-based malicious smart contract and intru- sion detection system for iot environment,”Mathematics, vol. 11, no. 2, p. 418, 2023
work page 2023
-
[66]
Smart contract vulnerability detection based on deep learning and multimodal decision fusion,
W. Deng, H. Wei, T. Huang, C. Cao, Y . Peng, and X. Hu, “Smart contract vulnerability detection based on deep learning and multimodal decision fusion,”Sensors, vol. 23, no. 16, p. 7246, 2023
work page 2023
-
[67]
Evaluating capabilities and perspectives of generative ai tools in smart contract de- velopment,
S. Khalid and C. Brown, “Evaluating capabilities and perspectives of generative ai tools in smart contract de- velopment,” inProceedings of the 7th ACM International Symposium on Blockchain and Secure Critical Infrastruc- ture, 2025, pp. 1–12
work page 2025
-
[68]
Ai-powered blockchain- a decentralized secure multiparty computation protocol for iov,
G. Raja, Y . Manaswini, G. D. Vivekanandan, H. Sampath, K. Dev, and A. K. Bashir, “Ai-powered blockchain- a decentralized secure multiparty computation protocol for iov,” inIEEE INFOCOM 2020-IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS). IEEE, 2020, pp. 865–870
work page 2020
-
[69]
L. Yu, Z. Huang, H. Yuan, S. Cheng, L. Yang, F. Zhang, C. Shen, J. Ma, J. Zhang, J. Luet al., “Smart-llama-dpo: Reinforced large language model for explainable smart contract vulnerability detection,”Proceedings of the ACM on Software Engineering, vol. 2, no. ISSTA, pp. 182–205, 2025
work page 2025
-
[70]
A smart contract vulnerability detection mechanism based on deep learning and expert rules,
Z. Liu, M. Jiang, S. Zhang, J. Zhang, and Y . Liu, “A smart contract vulnerability detection mechanism based on deep learning and expert rules,”IEEE Access, vol. 11, pp. 77 990–77 999, 2023
work page 2023
-
[71]
E. Chen, X. Tang, Z. Xiao, C. Li, S. Li, T. Wu, S. Wang, and K. K. Chalkias, “Suigpt mad: Move ai decompiler to improve transparency and auditability on non-open-source blockchain smart contract,” inProceedings of the ACM on Web Conference 2025, 2025, pp. 1567–1576
work page 2025
-
[72]
P. Chinnasamy, B. Subashini, R. K. Ayyasamy, A. Kiran, B. K. Pandey, D. Pandey, and M. E. Lelisho, “Blockchain based electronic educational document management with role-based access control using machine learning model,” Scientific Reports, vol. 15, no. 1, p. 18828, 2025
work page 2025
-
[73]
Qlammp: A q- learning agent for optimizing fees on automated market making protocols,
D. Churiwala and B. Krishnamachari, “Qlammp: A q- learning agent for optimizing fees on automated market making protocols,” in2023 Fifth International Confer- ence on Blockchain Computing and Applications (BCCA). IEEE, 2023, pp. 274–281
work page 2023
-
[74]
Connecting large language models with blockchain: Making smart contracts smarter,
X. Zeng, Y . Xian, D. Xuan, D. Yang, C. Li, J. Chen, P. Fan, and P. Liu, “Connecting large language models with blockchain: Making smart contracts smarter,”ACM Transactions on the Web, 2025
work page 2025
-
[75]
A. Idowu, “Leveraging ai and integrated data streams for predictive risk intelligence in decentralized finance markets.”
-
[76]
Aiarena: A blockchain-based decentralized ai training platform,
Z. Wang, R. Sun, E. Lui, T. Zhou, Y . Wen, and J. Sun, “Aiarena: A blockchain-based decentralized ai training platform,” inCompanion Proceedings of the ACM on Web Conference 2025, 2025, pp. 1375–1379
work page 2025
-
[77]
Doctrina: Blockchain 5.0 for artificial intelligence,
K. Tulkinbekov and D.-H. Kim, “Doctrina: Blockchain 5.0 for artificial intelligence,”Applied Sciences, vol. 15, no. 10, p. 5602, 2025
work page 2025
-
[78]
Privacy and trust redefined in fed- erated machine learning,
P. Papadopoulos, W. Abramson, A. J. Hall, N. Pitropakis, and W. J. Buchanan, “Privacy and trust redefined in fed- erated machine learning,”Machine Learning and Knowl- edge Extraction, vol. 3, no. 2, pp. 333–356, 2021
work page 2021
-
[79]
P. Guo, S. Xu, and W. Liang, “Verifiable blockchain- empowered federated learning for secure data sharing in the internet of medical things,”Intelligent Computing, vol. 4, p. 0132, 2025
work page 2025
-
[80]
Fled-block: Federated learning ensembled deep learning blockchain model for covid-19 prediction,
R. Durga and E. Poovammal, “Fled-block: Federated learning ensembled deep learning blockchain model for covid-19 prediction,”Frontiers in Public Health, vol. 10, p. 892499, 2022
work page 2022
discussion (0)
Sign in with ORCID, Apple, or X to comment. Anyone can read and Pith papers without signing in.